And it hides your IP address from hackers, your internet service provider (ISP), and even government spies. DuckDuckGo also has a no-log policy, meaning they don’t keep a record of your search history or collect other user data. When used with a dedicated private browser, DuckDuckGo can be a powerful search engine and a potent privacy tool. On the software end, the use of Tor and other anonymized browsers is not strictly illegal. In fact, these supposed “dark web” browsers are not tethered exclusively to this portion of the internet.
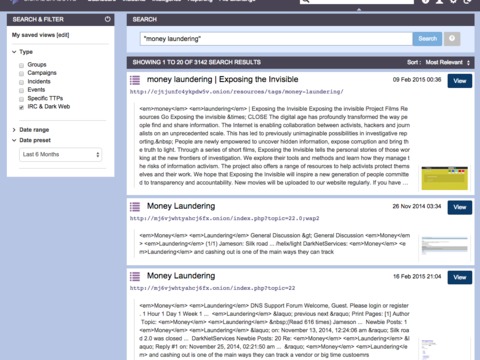
However, engaging in illicit activities on the dark web is illegal—just as it would be anywhere else—and punishable by law. Search engines are integral to the web browsing experience, but only about 10% of all websites are indexed on a typical search engine. The remaining sites, including those on the dark web, won’t show up when you search Google—they can be accessed only with a direct URL, IP address, or deep web search application.
The 12 Best Deep Search Engines To Explore The Invisible Web
- Torch is one of the oldest dark web search engines, having served the darknet community for years.
- VPN encryption protects your data from being intercepted while on the dark web.
- If one doesn’t work for you, you can always count on the other to help you find what you require.
- However, engaging in illicit activities on the dark web is illegal—just as it would be anywhere else—and punishable by law.
- This extensive database makes it a reliable tool for searching hidden services and uncovering a broad range of invisible web content.
- For example, this is the place to start if you want to study scientific research, historical documents, or specialized databases.
A reputable provider ensures that you can explore the invisible web without unnecessary risks. Haystak is one of the best search engines for dark web exploration, boasting an impressive index of over 1.5 billion .onion pages. This extensive database makes it a reliable tool for searching hidden services and uncovering a broad range of invisible web content. Haystak offers both free and premium search options, allowing you to choose the level of access that suits your needs. In 2008, a significant breakthrough occurred with the creation of Tor2web. This proxy application allowed you to access .onion sites using standard browsers.
Difficulty In Accessing Information:
The core functionality of the dark web relies on onion routing, a method that encrypts and routes user communications across multiple servers, known as nodes. It also promotes transparency and security by openly sharing its source code and inviting contributions. Founded in 1998 as Ixquick.com, we later changed the name to Startpage.com. At Startpage.com, they take into account the privacy dangers of recording people’s search behavior, and given their team’s strong convictions about privacy, they decided to act accordingly.
H5: Is DeepSeek Free To Use?
NordVPN allows you to create your private encrypted network for safe file sharing and work using its Meshnet feature. It uses dedicated IP addresses, enabling you to access IP-restricted networks. Recon Dark Web Search Engine emerges as a newcomer to the realm of premier Dark Web Search Engines in 2024.
Best Deep Search Engines To Explore The Invisible Web
Users in countries with strict access and user laws are often prevented from accessing even public sites unless they use Tor clients and virtual private networks (VPNs). Tor (“The Onion Routing” project) network browser provides users access to visit websites with the “. This browser is a service originally developed in the latter part of the 1990s by the United States Naval Research Laboratory. In case you’re wondering how to access the deep web, chances are you already use it daily. The term “deep web” refers to all web pages that that are unidentifiable by search engines.
It is a relatively new provider but offers better features than most established VPNs. The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers. This includes military-grade 256-bit encryption reinforced with a 2048-bit DH key and SHA2-384 authentication to ensure your traffic arrives at its destination safely. This adds extra protection since opening Tor itself encrypts your traffic.
Unlocking The Secrets Of The Deep Web Search Engine
Veridian Software is the company behind the now-dead portal for historical newspapers, Elephind. If you loved Elephind and want an alternative, you’ll be happy to know that all of its library is still accessible via Veridian’s website. The current repository has over 20,000 journals with over 10 million articles across all subjects.
DuckDuckGo: More Than A Dark Web Search Engine
The dark web refers to sites that are not indexed and only accessible via specialized web browsers. Significantly smaller than the tiny surface web, the dark web is considered a part of the deep web. Using our ocean and iceberg visual, the dark web would be the bottom tip of the submerged iceberg. At the dark end of the web, you’ll find the more hazardous content and activity. Tor websites are located at this far end of the deep web, which are deemed the “dark web” and are only accessible by an anonymous browser.
Having written about TV shows and series for over 3 years, Ademilade strives to create high-quality content consistently. Ademilade watches his favorite episodes or plays Valorant when not writing. Characters meeting the above requirements are more difficult to brute force, making them safer. If you can’t think of a strong password, consider using a password generator. Google and other companies can also help you generate strong passwords when you sign up on a website and store them in your profile.

Directory Of Open Access Journals – Best For Researchers And Academics
Install Avast SecureLine VPN to encrypt your internet connection and protect your privacy wherever you go online. Download Avast SecureLine VPN to encrypt your internet connection and protect your privacy wherever you go online. Whenever you’re online, but especially if you go on the dark web, you need a VPN to encrypt your online communications and data. If you have a legitimate or viable need to access the dark web, you’ll want to make sure you stay safe if you decide to use it. With many Tor-based sites being overtaken by police authorities across the globe, there is a clear danger of becoming government target for simply visiting a dark website.
What Are EWallets And How Safe Are They?
The Wayback Machine is a tool for those interested in internet history. It’s part of the Internet Archive, allowing users to access historical versions of web pages, making it an important resource for examining the changes of websites over time. While it works as a remarkable tool for scholars and researchers, it will be equally resourceful for genealogists and family historians.