Bitcoin therefore is proving very advantageous to law enforcement, which can be a good thing when capturing...
However, by following the tips outlined in this article, you can reduce the risk of fraud and...
I, for one, have basically given up on Washington, DC’s street “heroin.” Distressingly, it’s mostly oddly colored...
Furthermore, the anonymity provided by Bitcoin complicates the efforts to trace transactions back to their source. Bitcoin’s...
TAILS (The Amnesic Incognito Live System) is a portable OS that runs from a USB or DVD,...
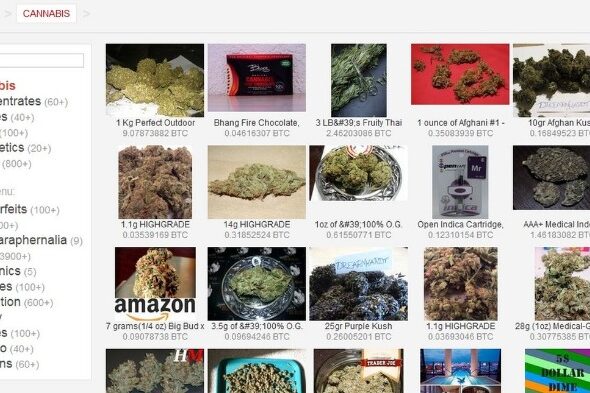
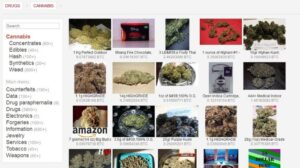
Yet according to a recent study, the online drug market is booming. There are well over 1,000...
Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed. Besides, victims...
“Bitcoin has been a major factor in the growth of the dark web, and the dark web...
It is hard to gauge actual risk, but I’d wager that buying MLP merchandise face to face...
Obviously, finding these .onion websites is the first challenge, as they won’t show up in Google search...