Ahmia promotes transparency by being open-source and allowing contributions. Its operations focus on respecting user privacy and maintaining anonymity through the use of the Tor network. Before exploring, make sure you’re familiar with the laws in your jurisdiction. Even someone’s accidental exposure to illegal content can result in them experiencing legal consequences. We’re back with another video in our Webz Insider video series on everything web data. Tor Browser already comes with HTTPS-Only mode, NoScript, and other patches to protect your privacy and security.
Why Our Site Is Better: Up-to-Date, Secure, And No Tracking
It’s ideal for first-time users and researchers looking for real, working .onion resources in a safer environment. Websites are grouped into categories like marketplaces, financial services, forums, search engines, whistleblowing platforms, and privacy tools. This makes it easy for users to find legitimate resources without having to sift through broken or malicious links. Each entry typically includes a short description, and many have been manually verified to ensure they’re live and relatively safe to visit with appropriate precautions. Some dark web engines try to filter out illegal content or prioritize verified, non-malicious services.
The interface works smoothly, but it usually loads slower due to Tor routing. Adamant offers blockchain-based secure messaging without needing phone numbers or email addresses. The platform stood out during my testing for its commitment to anonymity — all messages are fully encrypted and stored on a decentralized network. It’s particularly useful for sensitive communications that need to remain private.
Unlike regular websites, .onion addresses are long, complex strings of letters and numbers designed for anonymity and can be difficult to remember. Therefore, users often rely on trusted directories or updated links shared on community forums to ensure they access legitimate sites. Copy the .onion link carefully to avoid mistakes, as typos can lead to error pages or potentially malicious sites designed to impersonate the Hidden Wiki.

How To Access The Deep Web? (
However, this same anonymity also makes onion websites a breeding ground for illicit activities. The darknet represents a hidden layer of the internet that operates on encrypted networks, requiring specialized software for access. At its core, darknet links serve as gateways to this parallel digital universe, functioning differently from regular web addresses we use daily. They help users find real dark web links, verify them through uptime tracking, and avoid dangerous clones. Whether you’re browsing out of curiosity or pursuing sensitive research, using dark web sites that are safe in 2025 is a matter of both security and responsibility.
- However, there are a few countries that have banned access to BBC’s official homepage on the Web.
- The links are organized into categories such as general resources, marketplaces, and email services.
- This website used to host over 7,000 onion sites, giving users access to many dark web links.
- Keybase is an encrypted communication platform that enables secure file-sharing and messaging using public key cryptography.
- These platforms keep changing their addresses to avoid DDoS attacks or law enforcement agencies.
Marketing
If you don’t take the necessary measures, many unsavory activities can expose you to unnecessary risks. The use of the dark web raises suspicion as it shows there is something you want to do privately. The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved.
How The Hidden Wiki Works
Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too. It’s, ironically, more conspicuous than using popular browsers and sites. Because of its anonymity, the dark web is filled with illegal services and is used by numerous criminal groups, including ransomware gangs.
Best Dark Web Websites: Video
Cryptocurrency miners and other malicious software often target dark web users. Using a reliable antivirus to scan your device is worthwhile if you spot suspicious spikes in system resource usage. SecureDrop stands out as the leading platform for secure document sharing used by major news organizations. This open-source whistleblowing system enables anonymous file transfers with strong encryption. ZeroBin’s onion address ensures your traffic is routed through multiple nodes, so it’s challenging for any third party to trace any message back to your original location. It’s similar to Reddit or Quora but designed for anonymous users.
LostMyPassword – Dual Use Password Recovery And Credential Dumping Tool
This would verify if it’s a browser issue or just an issue with the site. Naturally, this makes the dark web a breeding ground for illegal activity. But onion sites can also serve nobler goals, like providing access to information and independent journalism in countries with government censorship. A favorite of journalists and their anonymous sources, SecureDrop makes it easy to share confidential information without revealing your identity. Many news publications, like the ones listed above, have a SecureDrop on their .onion sites. Search engines on the dark web are a bit of a contradiction because dark web sites by definition are not indexed by traditional search engines.
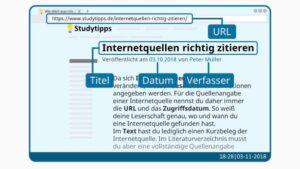
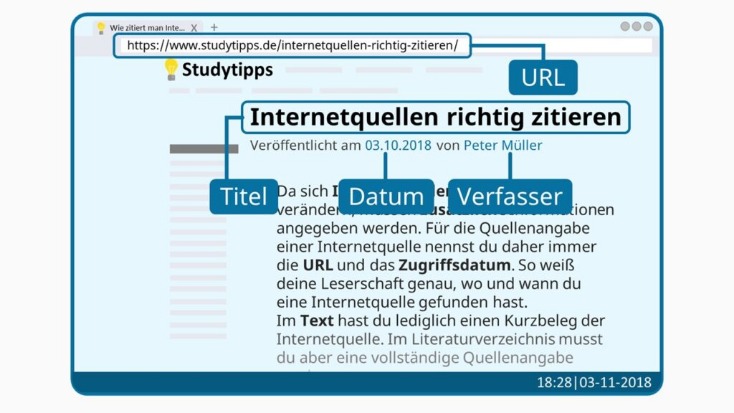
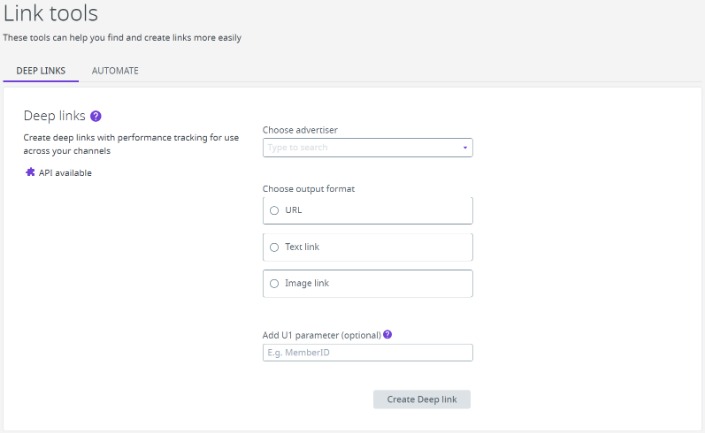
Web directories, also known as link directories, are websites that list useful and interesting Internet sites and pages, usually organized by categories. They are a kind of guide or indexes of pages and internet websites, sometimes with a short description of each site they recommend. Although they all serve a similar purpose, these search engines differ significantly in terms of usability, safety features, and how they index content.
- This is because law enforcement often actively monitors these sites.
- Always remember that while the above measures significantly reduce risks, no method guarantees complete security on the dark web.
- Viruses, ransomware, and other types of malware are more common on onion sites than on the normal internet.
- The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s.
- It is also used by whistle-blowers, journalists, and other individuals who are not involved in illegal activity but need to protect their communications and identities.
Deepweburl is the collections of deep web links, where you can find all that you need. As the name suggests, a blockchain contains blocks that record transactions. Each block has a fitting together with the block after and before.

OnionShare
In an age of surveillance and data leaks, these hidden networks still offer something the surface web often can’t — freedom and anonymity. To safely use the Hidden Wiki, verifying the authenticity of links is essential. First, rely on community-vetted sources and updated link lists from trusted forums like Dread or The Hub, where users report scams and share verified onion addresses. Check for recent user reviews or feedback to ensure the site is still operational and legitimate.