
This allows you not only to visit sites with the added privacy provided by the Tor network, but also search the web as privately as possible from inside the Tor browser. We are a Tor network dark web directory listing created in order to monitor and study popular darknet marketplaces and onion services. Onion websites use onion routing, a technique for encrypting and anonymizing data transmitted over the Tor network.
Are Dark Web Links Illegal?
PageOn.ai’s intelligent presentation tools ensure your content stands out, improving overall engagement and effectiveness. The following steps are beneficial when trying to access the deep web. Unfortunately we have not deployd non-JavaScript version of Ahmia yet. It offers outstanding privacy features and is currently available at a discounted rate. This information can be used to target ads and monitor your internet usage.

Also referred to as “non-indexed” content, it’s any content hidden behind some kind of access control such as a log-in or code word. It contains 7,500 terabytes of information, compared with only 19 terabytes of information in the “surface” web. To look at it in a different way, it makes up between 90% and 95% of the internet. Onion sites are considered part of the deep web because search engines like Google and Bing can’t index them.
Quick Comparison Table: The Dark Web Search Engine Features
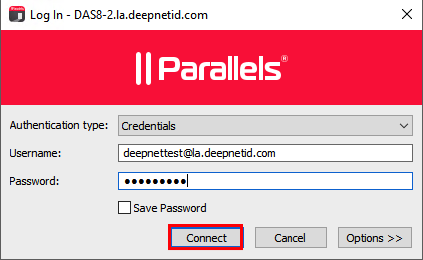
It means you cannot access websites on the dark web with regular browsers like Firefox or Chrome. Instead, you need a specific configuration, software, or authorization, such as Tor, to access it. Many reputable websites and news outlets like ProPublica and SecureDrop often share official domain addresses of onion sites on their pages. Some users also share links on encrypted apps like Telegram or Keybase that you can check.
Safe Browsing Practices On The Hidden Wiki
- Click its “Onionize” button to search the onion links for any other dark web websites.
- In many places, including the U.S., the UK, and the EU, accessing the dark web is legal for legitimate purposes.
- Whether you’re looking for stronger privacy, a simple interface, or a tool designed specifically for hidden services, there’s likely an option that fits your needs.
- The core functionality of the dark web relies on onion routing, a method that encrypts and routes user communications across multiple servers, known as nodes.
- If this sounds similar to The Wayback Machine, the concept is indeed the same.
- This .onion link makes it impossible for hackers to impersonate your profile.
Always verify the legitimacy of the sites you visit, as even filtered platforms can occasionally index questionable content. Unlike some dark web search engines, Candle does not overwhelm you with advanced settings or filters. Instead, it provides a streamlined experience that prioritizes usability. This makes it a great choice for beginners exploring the invisible web for the first time. The free version provides basic search functionality, while the premium version unlocks advanced features like detailed filtering and enhanced search results. This flexibility makes Haystak a valuable resource for researchers and casual users alike.
Is It Safe To Visit onion Sites On The Dark Web?
The dark web is a hidden part of the internet that requires specialized software to access. It indexes a wide array of content, including both legal and illegal sites. While it primarily indexes the surface web, it can also be accessed via the Tor browser and used as a general search engine. Unlike the regular internet, the Tor network can’t be accessed via standard browsers. Download Avast SecureLine VPN to encrypt your internet connection and protect your privacy wherever you go online.

Dark Web Websites: 10 Onion Sites To Explore
The platform started primarily as a blockchain explorer, allowing users to view and analyze transactions on the Bitcoin blockchain in real-time. The Comic Book Library is a digital archive dedicated to the preservation and dissemination of comic books, graphic novels, and related paraphernalia. This repository serves as a comprehensive resource for enthusiasts, scholars, and the general public interested in the rich history and diverse culture of comic books. The library’s mission is to provide free access to a wide range of comic book genres and periods, ensuring the preservation of this unique form of art and storytelling for future generations.
Types Of Dark Web Sites (and What Really Goes On There)
Agentic empowers you to turn abstract ideas into visually compelling presentations. By leveraging AI-driven content generation, you can create high-quality materials that captivate your audience. This feature enhances the value of your output, making it ideal for both professional and academic applications.

What Are Dark Web Websites?
It holds private databases, personalized information such as bank account details, social media account details, and even medical records. The fact that the deep web contains personal information makes it safe to explore, but if misused can lead to hacking. The dark web is a small part of the much larger “deep web,” which also isn’t indexed by search engines — but authorized users can access it using common web browsers. The deep web is made up of email platforms, workplace portals, subscription services, and banking websites — basically anything that requires a login. The “surface web,” on the other hand, is the publicly available part of the internet that search engines index.
Riseup provides email and chat services that keep no record of your online activity. Unlike the surface web, where pages are easily searchable, dark web sites use encryption to hide their IP (Internet Protocol) addresses. The CIA’s onion site allows users to securely report threats or suspicious activity, especially in regions where online surveillance is common. Its presence on the dark web also supports intelligence gathering and helps track cybercriminal activity. Unfortunately, many dark web websites are devoted to the illegal trade of leaked personal information. If you’ve ever experienced an uptick in phishing attacks and spam after a data leak or breach, it may be because your personal information has been posted to the dark web.
However, the payment mechanism is not the same as it is in normal life; we are used to transacting with cash, credit cards, or PayPal. On the dark web, there is just one way to pay, and that’s with cryptocurrencies like Bitcoin and Monero. Smart people never get caught since they know how to anonymize themselves, but the new user faces difficulty. So you have to use the dark web with whatever security precautions you can manage. Just don’t be stupid and ruin your lovely life by doing foolish things.
Hidden Answers

If you want to access this site, do it only for fair purposes and with proper security measures. Read about the adventures of modern-day explorers who have made it their mission to venture into the tunnel network of huge American universities. The site is different from our whole list, but still worth a mention. Sci-hub has more than 80 million research documents, and more than 80% of the database contains journal research articles. Since these pages would otherwise be behind paywalls, it stands to reason that this would go against copyright laws.
News, Media, And Other Information Organizations
Users have reported a 25% increase in success rates for marketing pitches, highlighting the platform’s ability to deliver impactful results. Beyond the Tor browser, consider using VPNs, encrypted communication tools, and secure operating systems. These tools add layers of privacy and protect against data leaks and surveillance. Because we can only download and install it on Windows, macOS and Linux, not available for mobile devices. However, there are important changes to highlight, such as a system to protect the user’s IP address in any type of activity.
Countries differ in how aggressively they monitor Dark Web activity. In some authoritarian states, accessing Tor nodes can flag you for surveillance. The Darknet is a subset of the Internet operating over encrypted, anonymous overlay networks that require special software like Tor, Freenet, or I2P. Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. Bear in mind too, that your internet provider will be able to see you connecting to Tor nodes, even if it doesn’t know exactly what you’re doing. Many people install a VPN as well, but then you’re putting your trust in an additional third party to not track your activities or report them to anyone else.



