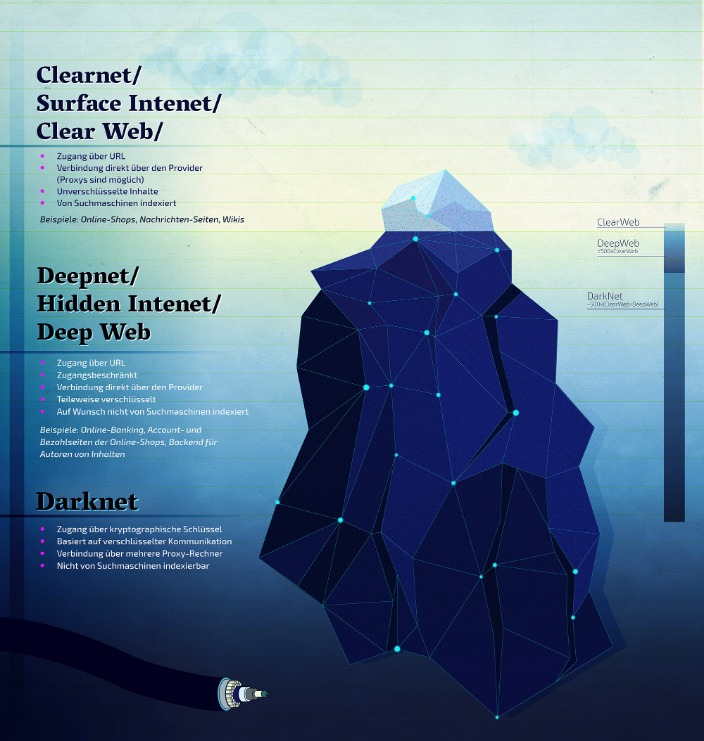
Malicious files might bypass Tor’s security, giving away your real IP address. If you must download files, ensure you’re using a separate, secure environment — such as a virtual machine. Cybercriminals often leverage the anonymity to leak sensitive information, like stolen credentials, credit card numbers, or company data. The dark web is a hidden part of the internet that requires specialized software to access. While it primarily indexes the surface web, it can also be accessed via the Tor browser and used as a general search engine.
Best Wallets For Monero And Bitcoin
- Another good practice is to cross-reference links with multiple sources to confirm consistency.
- The cost can be exorbitant, but for victims, it’s always higher and devastating.
- Criminals prefer the dark web because it offers anonymity like never before.
- It’s a hub for illicit activities, with cybercriminals ready to exploit any weakness.
- Whether you’re sending personal photos, important documents, or just having a conversation, it all stays private and protected from prying eyes.
- However, please note this article is for research and educational purposes only.
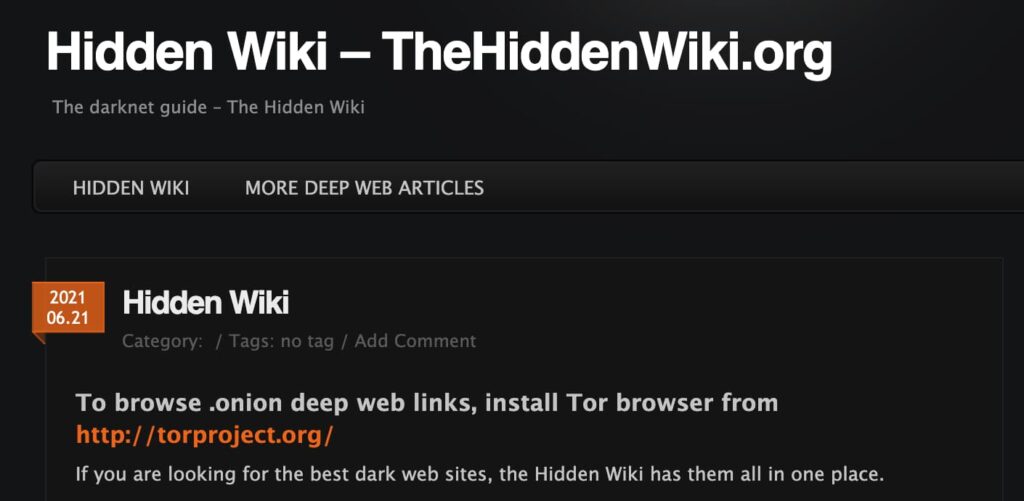
The Hidden Wiki is a gateway to these deep web resources, offering links to .onion sites that cannot be found via Google or other surface web search engines. Thus, users who want to explore hidden, uncensored, or private content often rely on tools like the Hidden Wiki because it provides structured access to resources beyond Google’s reach. To safely use the Hidden Wiki, verifying the authenticity of links is essential. First, rely on community-vetted sources and updated link lists from trusted forums like Dread or The Hub, where users report scams and share verified onion addresses. Check for recent user reviews or feedback to ensure the site is still operational and legitimate. Always use PGP keys when available to verify the identity of marketplaces or services.
DuckDuckGo (Dark Web Version)
TorLinks maintains one of the most reliable directories of verified .onion sites. Its strength lies in regular updates and community-driven verification of links. I especially like how TorLinks categorizes links based on their type, letting you easily find what you need.
Is The Hidden Wiki Safe?
For instance, stolen data can result in unauthorized payments, the draining of accounts, or even registered loans. Moreover, sensitive personal documents are made available on the dark web. Some things, like medical records, driver’s licenses, and passport information. The consequences can be lethal to those whose data is stolen, like identity theft, emotional distress, and even financial loss. Perhaps, hiring a hacker can feel impossible, but it’s a genuine threat that you need to be aware of.

Top 5 Dark Web Marketplaces To Monitor
It does not store logs and is protected from interference and malicious attacks. The platform is free and is run by volunteers in the US who prefer privacy and security. It is important to note that the people or journalists who use ProPublica to spread their truth recognize the risk of doing so.

Browse Privately
Always access the Hidden Wiki through the official Tor Browser, never via a standard browser. Disable JavaScript and other potentially risky browser features unless necessary, as they can be exploited to reveal your identity. Avoid downloading files or opening attachments from unknown sources, as these can contain malware. Use strong, unique passwords and enable two-factor authentication where possible. You can use a dark web scan tool to tell if your data has landed on the dark web.
- This is especially beneficial for professionals in cybersecurity or research, who require quick access to specific types of information.
- While it doesn’t index dark web content, it’s the default search engine on the Tor Browser because of its strong privacy features and lack of tracking.
- Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies.
- After more than a year of no updates, the site admin shut it down, reasoning that he couldn’t keep the list of onion links up-to-date.
Bitcoin Mixer / Tumbler Services:
This isolates any potential malware and prevents cross-contamination with your personal data. Using Tails OS can further security, as all your data is reset every time you close the device. Alt Address provides disposable email addresses specifically designed for dark web use.
Dark.fail is an easy-to-use .onion platform equipped with a status checker that tracks website uptime. The site offers access to PGP-verified URLs and runs free of JavaScript or tracking. This platform’s library of websites currently totals 50, which may not sound impressive until you consider that all the links are active and popular. You can access onion sites only through the Tor browser or special network configurations. On the Tor network, the onion domain name reflects the fact that, like the layers of an onion, the Tor browser consists of layers of protection. Tor encrypts traffic, masks your IP address, blocks trackers and browser fingerprinting, and doesn’t store a record of your activity.
Avoid clicking on suspicious links, disable JavaScript where possible, and never share personal or financial information on dark web sites. The Dark Lair is another strong contender for those looking for dark web directories beyond the Hidden Wiki. It boasts a broad catalog of .onion sites categorized into marketplaces, forums, crypto services, and more. What sets The Dark Lair apart is its intuitive design and clear categorization, making it easier for new users to find reliable sites without getting overwhelmed. Additionally, it provides community ratings and user feedback, adding an extra layer of trust. However, some caution is warranted as the directory includes user-submitted links that may occasionally slip through without thorough verification.
Is It Safe To Visit The Dark Web On An IOS Or Android Device?

Unfortunately, the platform was shut down in 2013 after an extensive investigation that was spearheaded by US Senator Charles Schumer. The closure led to the arrest of the platform’s founder Ross Ulbricht. According to the United Nations Office on Drugs and Crime (UNODC), all guns are manufactured legally.
This is no different from the “.net” or “.com” of the regular Internet. The Tor browser is the most preferred browser for surfing the dark web because it creates encrypted pathways for user traffic, ensuring all the activities are anonymous. The dark web is not easily accessible, especially with browsers like Chrome or Safari, as it requires specialized protocols like Tor’s onion routing.
Some believe STYX is the OG darknet market when it comes to financial crimes. It trades in hacked bank accounts, stolen credit card information, and other services that facilitate cryptocurrency laundering. The popular Silk Road was the first dark web marketplace that you could only access via the Tor Browser.