Using common sense like avoiding clicking on shady links or download buttons, sticking to known sites and adding a VPN for an extra layer of protection, you should be fine. Anonymity of the dark web is one of the main draws for using onion sites, and most dark web links use a “.onion” domain. This is usually due to the sensitive nature of the businesses or services they offer. Onion sites may offer secure access to cryptocurrency wallets or anonymous email clients.
Avoid Downloading Dark Web Files
In addition, even if the Tor node fails, your data won’t be exposed because the VPN’s encryption still holds up. As mentioned, we recommend using a safe provider like NordVPN, which also offers Onion Over VPN servers perfect for accessing the dark web safely. When using Tor for enhanced privacy and anonymity, it’s crucial to consider the security of your email communications. While popular email providers may be convenient, they often track user data, impose stringent monitoring, and may not be optimized for anonymous browsing. These services can potentially log your IP address or expose your information through various means, undermining the benefits Tor offers.

Vorm Web Search Engine
This means that using the dark web may attract attention from your ISP or even law enforcement. To reinforce your privacy while on the dark web, consider adding on a VPN like Windscribe as an extra layer of protection. SimplyTranslate is an onion based language translation service using the google translate engine.
What Challenges Does Tor Face Regarding Legal Accountability?
It’s a bit of a contradiction to talk about search engines for dark web sites because, by definition, these are not sites that get indexed by traditional search engines. Many dark web search engines on the darknet suffer from spam, because these spammy sites want to be indexed and found by the search engines as opposed to genuine onion sites. Vorm Web focuses on quality over quantity and splits findable results into three security categories, from secure to risky.
Awazon Market
In this guide, we’ll explore essential tools and best practices for locating and verifying working .onion links and their mirrors safely and effectively. One of the most frequently recommended security measures is to use a Virtual Private Network (VPN) in conjunction with Tor Browser, a practice often referred to as “Tor over VPN”. While Tor itself encrypts traffic within its network, the connection between the user’s device and the first Tor node (the entry node) is visible to the ISP. A VPN encrypts this initial connection, making it more difficult for the ISP to detect Tor usage. Some VPN providers offer “Onion over VPN” features, which route traffic through the VPN’s servers and then into the Tor network, providing a convenient way to access onion sites. Another significant factor behind disappearing .onion links is action taken by law enforcement agencies.
Even people with little to no knowledge can buy ready-made ransomware and launch attacks on their victims. Too-good-to-be-true investment offers are another classic scam on the dark web. Early participants may see some profit, but that money usually comes from new victims, not actual earnings.
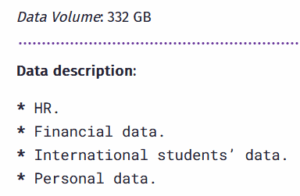
- This can include everything from full names, email logins, and passwords to credit card details, social security numbers, and bank account information.
- We are a Tor network dark web directory listing created in order to monitor and study popular darknet marketplaces and onion services.
- So, to clarify again, this tutorial will cover how to access the dark web privately and safely – not the deep web.
- Your ISP can’t see which websites you’re visiting on the dark web when you’re using Tor, but they might be able to predict or assume you are using Tor if they analyze your monitored internet traffic.
- Stay vigilant, respect others’ privacy, and consistently practice safe, responsible browsing.
Getting familiar with the tactics scammers use will go a long way in helping you protect your online data and assets. BidenCash is another latest marketplace that started in 2022, and is now home to sensitive financial data transactions. This is where cybercriminals go to buy and sell things like stolen credit card numbers, personally identifiable information (PII), and even SSH login details. One thing that distinguishes BidenCash on the dark web, however, is how it markets itself. Next up is Abacus, another newer market that has already made a massive name for itself, especially following AlphaBay’s closure. It contains 40,000+ listings for illegal products (mostly) and is worth an estimated $15 million, so it’s one of the largest markets out there.
The New York Times — Globally Recognized News Coverage
Anyone can archive or retrieve data on any site they want, wherever available. Immediately change your passwords, enable two-factor authentication, and notify your bank or credit card provider if the leaked information includes your financial data. You should also consider freezing your credit to prevent identity theft. If you think the Dark web marketplaces are just online shops, you’re wrong — these sites are the actual weapon stores for criminals.
Is Tor A VPN?
The Tor Network provided a way to open safe communication channels for political dissidents, while also offering a channel for American intelligence operatives to communicate from around the globe. Journalists in overly restrictive countries also appreciate the anonymity of the dark web. Silk Road became one of the most famous online black markets on the dark web for illegally selling drugs. The deep web contains sites and pages that are often prevented from being indexed by search engines and contain unlinked content.
MULTI-LAYERED ENCRYPTION
The VPN will protect your traffic when you connect with military-grade AES 256-bit encryption. This is high-level protection; no one can intercept your data or activities. The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. It will encrypt your traffic and data so no one can intercept it.
- It contains 40,000+ listings for illegal products (mostly) and is worth an estimated $15 million, so it’s one of the largest markets out there.
- Impreza Hosting is a service that helps you host a site on the Tor network.
- This ensures that your real IP address is hidden from the first Tor relay (it sees the IP address that your VPN provider supplies).
- Furthermore, it is strongly recommended to avoid downloading any files from the dark web unless absolutely certain of their safety and origin.
- Unlike other search engines, it does not collect or share web activities and personal data of users.
Then the Tor anonymity network relays further obfuscate your true location, as the browser relays your browser traffic through several relay locations. This encrypts your internet traffic using your VPN’s servers, protecting against outside parties monitoring all of your device’s internet activities. This encryption and relaying of your browsing data prevents anyone who is watching from detecting which websites you are visiting. Tor volunteers have been subjected to legal inquiries and investigations, including cases tied to child sexual abuse material (CSAM). Because volunteers host the Tor system, clients using the network can pass illicit materials through these volunteer relays without the volunteers’ knowledge.
Create new handles or pseudonyms to protect your identity throughout your online engagements. Here are some of the popular ones, exclusively hosted in the darknet. Web search in late 90x, total fun – that required luck and skill. Search algorithms back then used to be based on exact words matching and presented based on resource popularity and number of cross-references. Btw today’s search engine provides you with information that the algorithm considers being your intend (adjusted to probability), and there is far more complexity involved. It’s not illegal per se to access an onion website, but that doesn’t mean your actions while connected to the dark web are immune from law enforcement.