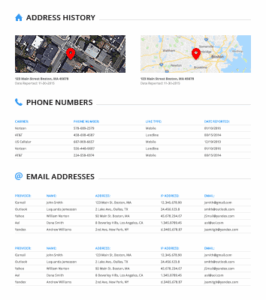
One of the main categories is Databases, where stolen databases are published, often containing sensitive information. In...
Uncategorized
A “Get in Contact” button will either bring the user to a page with a chat box...
I think it’s safe to say that these are unsanctioned exploits, all the more reason to boast...
However, some sites, namely, the Empire Market, forced users to log out when the life span of...
Since many dark web platforms lack the sophisticated resources needed to defend against such large-scale disruptions, affected...
Also, try its services risk-free with the 30-day money-back guarantee. A top-of-the-line VPN network that ensures maximum...
Due to the privacy-forward ethos of the Tor project, Tor Metrics stresses that the data it collects...
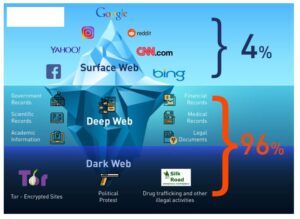
These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be...
This overwhelming response confirmed our vision and motivated us to continue developing and expanding TorDex into the...
Formerly, Darren served on the Committee of Technology Infrastructure under Mayor Richard Daley. Most e-commerce providers offer...