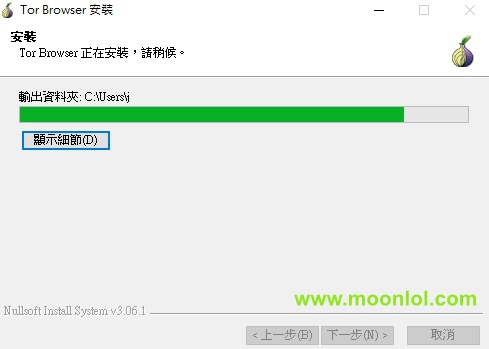
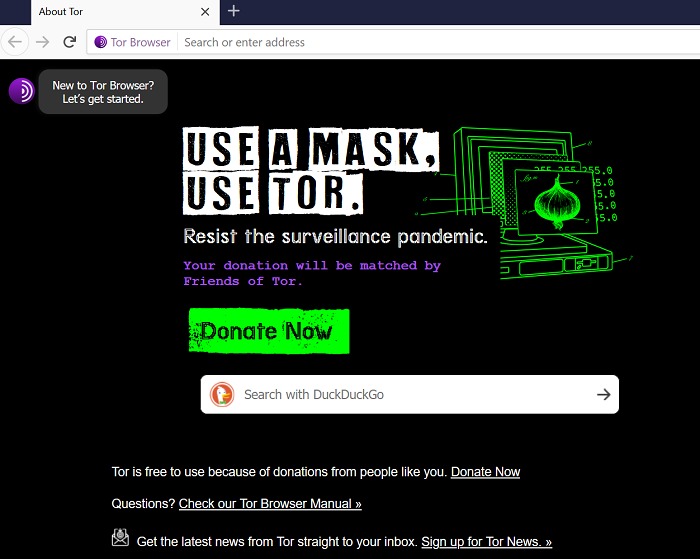
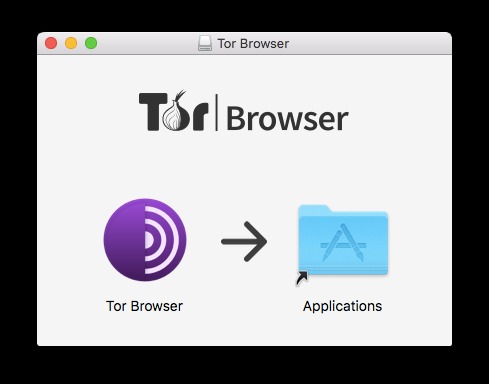
Used ethically, such as for privacy or study, one can search this area lawfully and safely. Combined with smart surfing behaviour and technologies like Tor and a VPN, even the darkest reaches of the internet may be securely traversed. If you’re new to Tor, setting up the browser software and connecting to the network might seem intimidating, but it’s actually straightforward. We’ll guide you through how to connect on Windows, Mac, Android, and even iOS. Upon visiting the official download page and selecting the macOS option, a disk image (.dmg) file will be downloaded. After the download, the user needs to open the .dmg file, which will mount a virtual drive containing the Tor Browser application.
Invisible Internet Project
As the images below illustrate, Tor consists of a three-layer proxy, like layers of an onion (hence Tor’s onion logo). Among the many benefits of using a VPN vs a proxy or Tor is that it provides full encryption for all the data you send and receive online. So not only is your web activity hidden, but you can mask your IP address by connecting via a wide range of global VPN server locations. Plus, most top VPNs (like ExpressVPN) support Tor traffic on their servers. Yes — the Tor browser and a VPN are similar, but there are some differences between them.
Tor Browser Bundle
Anonymity means much less risk of getting caught, which makes cybercriminals more daring on Tor. This combination can make malware threats more prevalent on the dark web than on the surface web. It’s easy to let your guard down on Tor, with all the promise of anonymity. But if authorities get a piece of information on you, or trick you into giving it to them, they can put together the rest. Using a VPN over Tor Browser can help protect your anonymity further, among other benefits. Such hacking techniques ought to concern everyone, as innocent Tor users will inevitably get caught up in such fishing expeditions.
Top Dark Web Browsers You Can Use And How They Work
Nevertheless, due to IP masking, users may appear to connect from a different location, potentially leading to some sites attempting to block Tor users, limiting access. Layered encryption and IP masking via onion or garlic routing make it extremely difficult to link dark web activities to specific users. However, situations including firewalls, malware, of incorrect setups, or user error provides a risk of identity disclosure. For example, state-level actors can execute traffic correlation attacks, wherein they monitor both incoming traffic at the entry nodes and outgoing traffic at the exit nodes. By observing these patterns, they can link a Tor user’s request to a server and reveal their intended destination. Tor traffic is decrypted at the exit node, which opens a vulnerability for malicious actors to inject malware or intercept traffic.
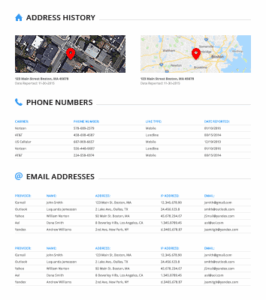
Hackers Use Exit Nodes
The dark web is used by journalists, whistleblowers, and political activists who need the protections that it offers. Anything you need to do that has to be off the books to some extent, for noble or ignoble reasons, can be done on the dark web. Digital surveillance and cybercrime continue to rise, underscoring the need for disciplined cybersecurity habits. Protecting your digital identity is crucial when navigating the dark web. Password managers and anonymous email services prevent unauthorized access and ensure private communications. Selecting the right browser for accessing the dark web is crucial, as it significantly impacts anonymity, security, and overall usability.
Step 4: Configure Basic Settings
For recommendations on choosing a VPN, look for expert reviews and articles. If you’ve ever checked your medical results online through a portal that required a login, you were navigating the deep web. It’s huge, making up about 90% of the internet, but it’s mostly mundane, hidden behind login screens for privacy and security.
Do I Need A VPN To Access The Dark Web Using Tor?
It helps journalists, human rights activists, and privacy-conscious people who need to keep their actions and identities safe from being watched or tracked. Whonix is similar to Subgraph, which means it isn’t a standalone browser but an OS like Subgraph built on TOR’s free software. This includes journalists, activists, and workers who care about security and need to keep sensitive information safe from advanced threats.
Online Freedom In Your Hands
- Let’s go through the setup process for each, as well as how to use them effectively.
- While it is true that the dark web is sometimes used for illicit purposes, not everything on the dark web is illegal.
- DuckDuckGo, known for its privacy-focused approach on the surface web, also has a presence on the dark web.
- LibreY is a secure dark web search engine that prioritizes user privacy by operating without JavaScript.
Once the file is downloaded, run it to launch the installer and follow the prompt until the Tor browser is installed. You can block out the constant surveillance and restore your privacy with a few quick changes. While not a browser itself, Orbot can encrypt traffic from your mobile browser, Gmail app, Google Maps, instant messaging apps, etc., using the Tor protocol.
Step 2: Download And Verify The Tails OS Image
A top-of-the-line VPN network that ensures maximum security while accessing dark sites online. NordVPN is one of the best VPNs to combine with the Tor browser whenever you want to surf dark sites. It offers top-of-the-line security and fast speeds for a smooth browsing experience on the dark web. The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. It will encrypt your traffic and data so no one can intercept it.
Uninstalling Tor Browser is as easy as deleting it and emptying your recycle bin. Some people get confused when trying to uninstall Tor, since it doesn’t show up in system programs. That’s because Tor is a fully portable, self-contained .exe file. Tor does not make any changes to the Windows Registry, so don’t worry about leaving a trace after you uninstall your Tor Browser.
Despite some skepticism about its origins and privacy due to its military development, Tor remains the preferred choice for safe dark web navigation. This part of the internet is notorious for illegal activities, facilitated by the anonymity it offers. Crimes range from data theft and selling illegal goods for cryptocurrencies to human trafficking and more severe offenses. In this setup, the VPN connection acts as a middle layer between your device and Tor, routing your internet traffic through the VPN before it reaches the Tor network. When you use the Tor network, your traffic is layered in encryption and routed via a random relay, where it’s wrapped in another layer of encryption.
Unlike the surface web, which we access daily through browsers like Chrome and Firefox, the dark web requires specific browsers to maintain user anonymity and ensure secure access. Users should never share any personal information, such as their real name, email address, or any details that could potentially link their dark web activities to their real-world identity. This includes avoiding logging into any personal accounts (social media, email, banking, etc.) while using Tor Browser.