“The most important thing is for people to keep an eye on their transactions and report any fraud immediately,” Krebs says. “When vDOS got breached, that basically reopened cases that were cold because the leak of the vDOS database supplied the final piece of evidence needed,” she said. If you ever decide to explore the dark web, protecting your identity is crucial.
Customers
EMV cards generate unique transaction codes that cannot be reused, thereby preventing certain types of fraud. While many cybercriminals are out to simply steal our information, satisfied with creating havoc for individuals or businesses, the majority do it for the money. The threat actor behind the AllWorld Cards marketplace has a clear goal in mind. They are actively promoting the platform on Dark Web hacking-related platforms since late May 2021. Telegram carding groups have become a significant threat in the cybercriminal community, with tens of thousands of members easily accessible through the chat application.
How To Conduct A Secure Code Review – Tools And Techniques
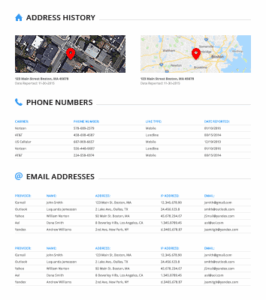
Black market credit cards are often obtained through the dark web or by purchasing them from unscrupulous sellers. A credit card dump is a type of crime where a criminal makes an unauthorized digital copy of a credit card. Once your card is canceled and the statement reviewed, the next step is to go to IdentityTheft.gov. This website, run by the Federal Trade Commission (FTC), will help you report and recover from your credit card fraud.
How To Use Tools To Detect And Flare Up Potential Fraud
This information comes in several flavors, with “CVVs” and “dumps” being the most popular. Learn the basics of credit card cards, including features, fees, and rewards to make informed decisions about your credit card usage. The price for cloned cards varies depending on the credit limit, with an average price of $171. These groups often originate from leaked credit card credentials, which have become a common phenomenon, particularly in the past months. Canceling your credit card is a bit more complex, but you can start by contacting your bank or credit card issuer to report the card as stolen.
As one of the prominent platforms supporting such activities, card shops make carrying out such scams relatively easy and popular. We want our guests to understand that just because they shopped at Target during the impacted time frame, it doesn’t mean they are victims of fraud. In fact, in other similar situations, there are typically low levels of actual fraud. Most importantly, we want to reassure guests that they will not be held financially responsible for any credit and debit card fraud.
Table Of Contents
This stolen information is then used to create counterfeit credit cards or make fraudulent online purchases. The term “dump” refers to the act of extracting the data from the credit card’s magnetic strip or chip. B1ack Stash’s primary motive from the outset has clearly been financial gain, which they have pursued by building a strong reputation as a card seller within the carding community. Our analysis of the payment card details leaked by B1ack over the past six months and the data we’ve collected for the affected local banks indicates that these were largely obtained through phishing campaigns.
- Credit card dumps are a serious threat in today’s digital landscape, putting individuals and businesses at risk of financial loss.
- It offers counterfeit documents, financial fraud tools, hacking and malware services.
- Multiple new shops, including BidenCash, appeared after UniCC, the initial new market leader, fell to a Russian crackdown in January 2022.
- Japan, the UAE, and Europe have the most expensive identities at an average of $25.
- Our analysis showed that 42,310 of these stolen cards were unique or first observed in the Argos intel collection.
Is It Best To Get Rid Of Unused Credit Cards?
In line with b1ack’s freebie marketing strategy, they announced the release of 1 million stolen payment cards for free on several popular carding forums on the last day of April this year. This massive giveaway served as the grand launch celebration for their “carding shop”. The threat group mentioned that users could claim their share by signing up at their shop and visiting the freebies section. According to them, this gesture was their way of saying thank you for choosing b1ack’s Stash for carding needs. They also highlighted the premium section of their shop, which offers CCS/FULLZ/NON-VBV/DUMPS. Implementing a 3-D Secure ACS solution, like Outseer 3-D Secure, fortifies the fraud prevention strategy.

Daily Banking
B1ack’s Stash is a dark web carding marketplace that specializes in the distribution of stolen credit and debit card information. Emerging on April 30, 2024, it quickly gained notoriety by releasing 1 million stolen payment card details for free, a strategy aimed at attracting cybercriminals to its platform. The market sells credit card information to users occasionally shares free credit card dumps (as seen below).
It’s a wake-up call for all of us to be more vigilant about our online security. They can be used to make purchases online or in-store, just like a regular credit card. Established in 2022, WizardShop is one of the biggest data stores on the dark web, focusing mainly on carding and financial data. Valued at approximately $15 million, Abacus Market is one of the most lucrative platforms in the dark web ecosystem.
Why Physical Security Maintenance Should Never Be An Afterthought
Sure enough, the bank’s database showed that all had been used by customers to make purchases at Target stores around the country between Nov. 29 and Dec. 15. According to the “base” name for all stolen cards sold at this card shop, the proprietor sells only cards stolen in the Target breach. The Google hacks, popularly known as Google dorks for credit card details,48 are also used often in obtaining credit card details. It is important to note that the consequences can extend beyond legal penalties. Individuals convicted of credit card dump activities may also face reputational damage, making it difficult to secure employment, obtain credit, or maintain personal relationships.
Those involved in credit card dump activities can face criminal charges, leading to fines, imprisonment, or both. The specific legal consequences vary depending on the jurisdiction and the extent of the individual’s involvement in credit card dump fraud. It is essential to note that credit card dump activities are carried out by skilled individuals who exploit vulnerabilities in security systems. As technology advances, so do their methods, making it crucial for both consumers and businesses to stay vigilant and employ robust security measures to prevent credit card information from falling into the wrong hands. In this article, we will delve into the world of credit card dumps, exploring how they are obtained, the different types of dumps, the dangers they pose, and how you can protect yourself from falling victim to this form of fraud.
Criminals Are Selling Millions Of Stolen Credit And Debit Card Numbers On The Dark Web
Considering this backdrop, it is evident that b1ack’s primary goal has consistently been to profit from the sale or use of these stolen credit card details. By leveraging dark web markets, underground forums, and direct transactions, they aim to capitalize on the extensive reputation and reach they have established through their effective marketing strategy. In a more recent development, on February 19, 2025, B1ack’s Stash escalated its operations by claiming to leak an additional 4 million stolen credit card details for free. This massive data dump was publicized on underground cybercriminal forums like XSS and Exploit, serving both as a marketing tactic and a means to establish credibility within the cybercrime community. It has built a reputation for being a reliable source of stolen credit card data and PII. Renowned for its extensive inventory of financial data and sophisticated operating methods, Brian’s Club is a key player in the underground economy of financial cybercrime.
- The story of dark web marketplaces kicks off with Silk Road, launched in 2011.
- By adding an extra layer of authentication, financial institutions reduce the risk of fraudulent activities during transactions.
- Considering this backdrop, it is evident that b1ack’s primary goal has consistently been to profit from the sale or use of these stolen credit card details.
- They can check for any suspicious objects on or around ATMs, gas pumps, and POS machines.
- Black market credit cards often have high credit limits, making them attractive to scammers and identity thieves.
All of the card data stolen from BriansClub was shared with multiple sources who work closely with financial institutions to identify and monitor or reissue cards that show up for sale in the cybercrime underground. By following these precautions, you significantly decrease the chances of falling victim to credit card dumps and safeguard your financial well-being. The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods.
BidenCash shop was established in April 2022, following the seizure of other card shops and carding platforms by the Russian authorities. Since its inception, it has been attracting the attention of both old and new cybercriminal customers. When the bank examined the common point of purchase among all the dumps it had bought from the shady card shop, it found that all of them had been used in Target stores nationwide between Nov. 27 and Dec. 15. Subsequent buys of new cards added to that same shop returned the same result. These methods are deliberately designed to cast a wide net, targeting users across multiple platforms where significant groups are likely to input their payment card information, thereby maximizing the potential to capture valuable data. WeTheNorth is a Canadian market established in 2021 that also serves international users.
Deep and dark web credit card sites include forums and marketplaces that host the trade and share of illicit content relating to credit cards. But there are basic steps anyone can take to minimize becoming an identity theft victim and having fullz with their personal and account information sold around the Internet. The prevalence of credit card dump activities highlights the need for improved security measures in our financial systems. Financial institutions, merchants, and individuals must prioritize robust security protocols, employ encryption technologies, and stay updated on the latest threats to prevent credit card information from falling into the wrong hands.