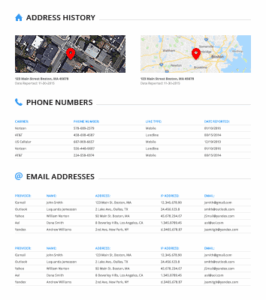
The open or surface web is what you access daily through search engines like Bing or Google. Before you even turn on the device, search engines have crawled through the web, looking for information, evaluating the sources, and listing your options. Data breaches happen all the time, and your login credentials and other data might be on the dark web already. Avast BreachGuard scans the dark web and will alert you immediately if and when it detects your personal data. BreachGuard will guide you through the process of recovering your accounts, helping you lock them down before a hacker can use your leaked credentials. Some hackers offer ransomware as a service (RaaS), where cybercriminals can “rent” a strain of ransomware from its creator in exchange for a fee or a percentage of their ransom payments.
How To Access The Dark Web
You’ll often see a sign in stores that says “look, don’t touch,” and it’s not a bad adage to bear in mind as you navigate around the dark web. Pushing your hardware to its full potential — such as by enabling XMP — ensures that you get the best performance which is crucial for all sorts of heavy tasks including gaming. Memory is one of the key components that can bring a noticeable improvement in video quality and speed. To use the dark web safely, use as many privacy-enhancing tools or programs as you can, and do not identify yourself in any way to anyone for any reason. While visiting any of the sites you find on those Wiki sites, do not maximize your browser, as it can help identify you by your monitor resolution.
Can A VPN And Tor Make The Dark Web Completely Private And Secure?
PHILADELPHIA, Miss. — Military veteran Obbie Riley is “sad, angry, and all of the above” as he thinks about the high cost and lack of broadband access in his rural Mississippi hometown. With our free newsletter, Seen & Heard, you can get the biggest stories of Black America delivered to your inbox each week. Sign up for our free newsletter and get our biggest stories of the week every Saturday in your inbox. In an ever-changing world, we’re here to help you stay ahead of what’s to come with the tools to measure, connect with, and engage your audiences. West Elm Caleb went from a local Hinge player to dating supervillain, the target of a massive, righteous internet investigation. Moreover, the president uses the official United States government @POTUS Twitter account now, per his profile page.
Dark Web Chat/Social Networks
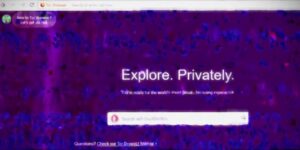
There are also privacy and anonymous browsers, which are designed to keep you safe on the regular ‘open’ web. For example, the Epic browser is programmed to always run in private mode, so it doesn’t store data about which sites you visit. It is based on Chromium, the open-source of Google chrome but the developers claim to have removed all Google tracking software and that the browser stops other companies from tracing you too. Unlike the open web, these sites aren’t really worried about being found by on-page SEO tools like web crawlers.

The CSO Guide To Top Security Conferences
Some media outlets also maintain an online presence via the dark web when their surface websites are blocked, and other websites do the same when they are banned at the ISP level by countries during periods of unrest. For example, this can include tools hosted for combating censorship — critical services for individuals in countries with stringent government surveillance and control, as well as privacy-enhancing anonymous email and whistleblower drop boxes. If you make use of a password manager, then it may come with a feature that monitors the dark web for mentions of your email address and password, or any other personal details.
Even in normal times, completing homework, finding a job, working from home, starting a business, making appointments, and accessing government services all require an internet connection. However, too many low-income families don’t have this critical service and are on the wrong side of the “Digital Divide,” a term used to describe the gap between those who have access to computers and the internet and those who do not. Frequently, low-income communities of color sit on the wrong side of this digital divide.
- The best VPN options are paid-for and subscription-based, as many free options will either throttle your speed or collect your data.
- By using Tor, and especially in combination with a VPN, your internet signal is encrypted, making it invisible to your ISP.
- Bear in mind too, that your internet provider will be able to see you connecting to Tor nodes, even if it doesn’t know exactly what you’re doing.
- The BlackPlanet interface feels dated, with an early-2010s-Facebook quality to it, even as the posts crawling across the main feed reference music or events from 2024.
Choose A Dark Web Search Engine
When accessing the dark web, the first step is to install a dark web-friendly browser on your computer. Unlike traditional browsers, this will route your internet traffic through an anonymizing network and mask your IP address. Dark web search engines exist, but even the best are challenged to keep up with the constantly shifting landscape. Even one of the best search engines, called Grams, returns results that are repetitive and often irrelevant to the query. Link lists like The Hidden Wiki are another option, but even indices also return a frustrating number of timed-out connections and 404 errors.
View Within Art Histories
- As such, the dark web has attracted many parties who would otherwise be endangered by revealing their identities online.
- Phillips who is also COO uses her background which spans the legal and tech industries to contribute to the retail side of the brand.
- While major takedowns have disrupted parts of the dark web, it remains resilient, with new technologies and changing criminal strategies.
- Privacy coins like Zcash and emerging protocols leveraging zero-knowledge proofs are gaining attention for their ability to further mask transactions.
Achieving an aggressive and inspired broadband vision will help families stay connected, provide economic opportunity, increase resiliency during crises, and improve the quality of life for all Californians. We don’t want to change to a more expensive WiFi because my mom and dad aren’t working. Research indicates that average users will need speeds of 150 Mbps by 2025. However, the majority of low-income internet plans only provide speeds of Mbps today(5). When we asked people about the limitations of their internet access through only their smartphone, they mentioned missing out on career opportunities.
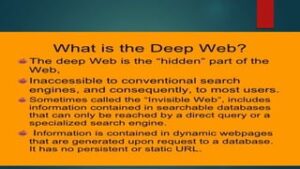
A groundbreaking work, Misogynoir Transformed highlights Black women’s remarkable efforts to disrupt mainstream narratives, subvert negative stereotypes, and reclaim their lives. Many of this generation’s most important social movements were birthed on Black Twitter, including #BlackLivesMatter, #OscarsSoWhite, #SayHerName and the #MeToo movement. The platform, which has been around for nearly two decades, has been instrumental in the spreading of news and information, and has played a vital role in activism and advocacy within society. Dark web, websites not indexed by search engines and theoretically possible to visit with complete anonymity. The dark web is a hidden part of the internet not indexed by regular search engines, accessed through specialized browsers like Tor.

Sally Doty, executive director of BEAM, Mississippi’s broadband office, says it’s a huge undertaking to get all Mississippians connected to high-speed internet. Before any money is awarded, the federal government has to approve their plan. She’s hosted community engagement sessions across the state, including the Delta region where Washington lives.
Drugs, weapons, and stolen IP and data are all hot businesses on the dark web, with terabytes of information on offer. Traders cash in on stolen credit card data dumps, initial access points to vulnerable systems, credentials, and intellectual property belonging to companies compromised during cyberattacks. The internet opened the door to a realm of possibilities that permanently changed the business landscape and our personal lives.
Article CitationsMore>>
Rather, it is bound to a complex history, simultaneously recalling the experiences of one individual and the condition of race relations across the United States. ZDNET’s recommendations are based on many hours of testing, research, and comparison shopping. We gather data from the best available sources, including vendor and retailer listings as well as other relevant and independent reviews sites. And we pore over customer reviews to find out what matters to real people who already own and use the products and services we’re assessing. The moderators enforce a strict policy against posting links to illegal products or services, so you’re more likely to find safer dark web addresses here. Tor is both a type of connection – with the extended relays – and a browser.
However, if you go poking around in illegal sites and services or don’t practice good operational security by offering up personal information or trying to perform illegal activities, it very much isn’t safe. You may be targeted by law enforcement, exploited by hackers, or threatened by criminals using the dark web for nefarious purposes. Still, there’s reason to hope that we may be entering a new era of social networking that prioritizes real connection over conflict-fueled engagement.