Tools like Tor are used to bypass government-imposed firewalls and surveillance, ensuring open communication. The significance here...
search
Upon detecting a threat, Scout raises an alert in the monitoring dashboard. It is then up to...
While you cannot “see” someone on the dark web, there are valid, legal .onion services you can...
It provides all the same resources—contacts, services, and information—that are available on the official CIA website. Those...
These crawlers are designed to respect the network’s anonymity protocols and provide search results based on query...
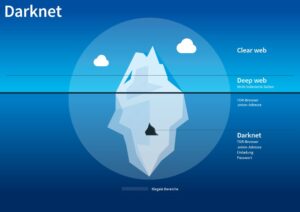
It contains 7,500 terabytes of information, compared with only 19 terabytes of information in the “surface” web....
It uses encrypted networks like Tor (The Onion Router) and I2P to keep users anonymous and content...
With over 32 million indexed websites and 14 million .onion links, its database is substantial, rivaling Torch’s...
Clicking on random onion links is quite risky and isn’t recommended. A random dark web link can...
While it is true that the dark web is sometimes used for illicit purposes, not everything on...