Despite their controversial nature, these marketplaces continue to evolve, offering a glimpse into the darker side of online commerce. As cyber threat intelligence professionals monitor these markets, they gain insights into emerging threats and malicious activities that can impact organizations and individuals. Some believe STYX is the OG darknet market when it comes to financial crimes. It trades in hacked bank accounts, stolen credit card information, and other services that facilitate cryptocurrency laundering.

Darknet Communications In 2025 – From IRC Forums To Telegram Crime Networks
Abacus Market appeared on the scene in 2021 and quickly became one of the heavyweights among English-speaking markets on the dark web. The categories are well organized, ranging from drugs and fraud to digital products, guides, and malware.What really sets it apart is its focus on security and usability. It supports PGP encryption, two-factor authentication (2FA), alerts against fake sites (antiphishing), and a verification system for sellers. Its interface is easy to navigate, and it has a reliable escrow system, as well as allowing payments with Bitcoin and Monero. All of this has made it one of the most reliable markets still active in 2025.
Criminal Hacking Services
Total darknet market revenue fell from $2.3 billion in 2023 to $2 billion in 2024. One of the most common types of illicit goods is stolen login credentials, often collected from data breaches. These “credential dumps” allow criminals to access online accounts, steal identities, and commit fraud. Even if you’ve never visited these markets, your personal and financial data might already be there, having been leaked through a data breach. Criminals use this information for money laundering, opening bank accounts, applying for loans, and draining your finances.
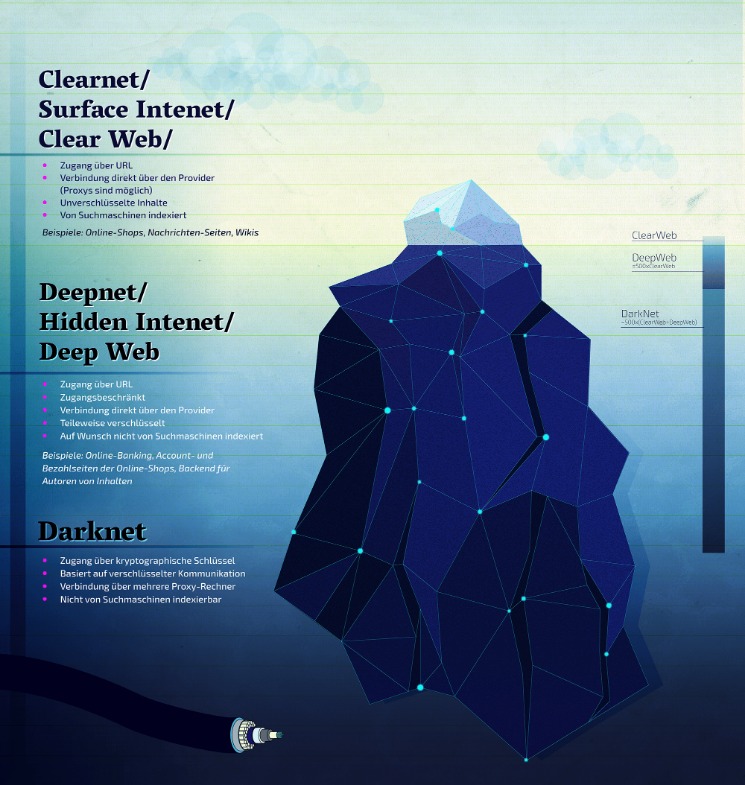
Built on Tor, these sites mask IP addresses by routing traffic through encrypted relays, ensuring anonymity for both buyers and sellers. Bitcoin was initially used to process payments, offering pseudonymity rather than full anonymity. Torzon market made its debut in September 2022, and ever since, it has been on an upward trajectory. In fact, it now features more than 11,600 illegal items, which include hacking tools, hard drugs, and all types of cybercrime services. The market started in 2021 in Canada and features both international and Canadian users. The market offers things like malware, fake documents, and financial fraud services.

The Full List Of Trusted Darknet Markets:
However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired. We deliver contextualized, actionable intelligence through our dedicated platform or API integration, ensuring that you can respond effectively to darknet threats. Radar Rundown Private search engines use the metasearch or proxy search model and the proprietary cr… Radar Rundown Free firewall software allow privacy ethusuiasts to secure their network and block mal…
Loss Of Anonymity
These listings often include detailed descriptions, user reviews, and even shipping guarantees. Dark web markets work much like regular e-commerce websites but with extra layers of anonymity and encryption. Buyers browse listings, place orders, and pay with cryptocurrency — typically Bitcoin or Monero — to obscure transaction trails. In this article, we’ll explore what dark web markets are, how they work, and why they’re so risky. We’ll also discuss examples of major marketplaces, myths about the dark web, and tips on staying safe in case your personal data ever ends up there. To access darknets, users typically need to download and configure the Tor Browser; a modified version of Mozilla Firefox that routes all traffic through the Tor network.
Anonymity Through Tor
We randomly allocate 20% of the samples for each label to the validation set, ensuring the selection of at least one sample, while the remaining samples form the training set. This method ensures that data partitioning maintains label equilibrium while concurrently reducing the impact of class imbalance on model evaluation. The objective of this loss function is to refine the embedding space by simultaneously minimizing intra-class distances and maximizing inter-class separations. This method ensures that each product category is represented as a binary vector, where only the element corresponding to the category is 1, and all others are 0. The sale of fentanyl its derivatives or synthetic drugs containing such compounds is banned.

In response, cybersecurity professionals, law enforcement agencies, and policymakers around the world are working to combat this growing menace. They employ various techniques, such as tracking and infiltrating dark markets, developing advanced threat intelligence, and enhancing international cooperation. As darknets and dark markets continue to evolve, understanding their dynamics and implications is crucial for fortifying the cybersecurity defenses of individuals, organizations, and nations in the digital age.
This study utilizes the BERT model to extract the stylistic elements of product titles and descriptions provided by sellers. Research in 42 indicates that BERT can acquire extensive linguistic knowledge during its pre-training phase. The lower layers of the model capture syntactic data at the phrase level, the intermediate layers acquire more intricate language features, and the upper layers concentrate on semantic information. Researchers investigating virtual identity profiling on the dark web have shifted from single-attribute analysis to multi-feature integration. This represents a transition from surface-level to deep-level methods and from one-way to multi-way processes.
Exodus Marketplace
Interestingly, the USA seems to account for 5% of counterfeits on dark markets while only accounting for 0.4% in seized goods. Subsequently, we (IV) compare dark web counterfeit prices with prices of the same products on the surface web to understand possible profit margins for the various product types identified. We then (V) compare our results to observations made through border seizures, complaint statistics, and activities from authorities to contribute to the overall understanding of the counterfeit economy. Investigators discovered a plethora of black market goods available on Silk Road. There were various illegal drugs including heroin, Ecstasy, LSD, marijuana and steroids. Also, illegal weapons, books on how to construct bombs, counterfeit identification and counterfeit merchandise.
The clear layout of Nexus Market enables users to easily search by category or conduct more specific searches by using the search bar. With a vast selection of over 22,000 listings in different categories there is plenty to choose from. Tor2door Market is among the largest dark net shops you must visit in 2025 if you’ve decided to visit such sites. On average, the marketplace consists of more than 11,000 items and 1000 vendors.

The LabelSimCos Loss is a novel loss function designed for multi-label classification tasks. It leverages label embeddings and cosine similarity to measure how closely the predicted labels match the true labels. The core objective of this loss function is to maximize the similarity for true labels while minimizing the similarity for non-true labels. A day consists of 24 hours, which are divided into several time segments based on a predefined segment length (segment_length, e.g., 4 hours). For each hour, the corresponding time segment is calculated and represented using one-hot encoding. This formula adjusts all price data to the range 0, 1, ensuring that different price values can be compared on the same scale and mitigating the impact of virtual currency price fluctuations.
- This malware-as-a-service model allows less tech-savvy criminals to launch malware-driven cyberattacks without building the tools themselves.
- This secure setup is useful for those who want to avoid government surveillance or keep their personal information safe from online threats.
- That push led to the arrest of Ross Ulbricht, the founder of Silk Road, after a long and intense investigation.
- The dark web features all types of hackers, from solo hackers to well-organized hacker groups that take care of high-stakes or more complex projects.
History Of Virtual Currencies And Cryptocurrencies: A Brief And Informative Idea About Cryptocurrency
We will moderate and monitor these reviews in order to ensure fair reviewing system. Nexus’s professional support team is always available to assist you in navigating its features with ease. With growing audiences globally, Nexus plans to introduce more localized offerings tailored to different markets. Nexus is deploying UI updates that promise even smoother navigation, optimized for mobile users and quicker browsing experiences. Access the Nexus Market Darknet through a privacy-focused browser like Tor. Tor encrypts your internet traffic and routes it through a series of servers, allowing you to remain anonymous.
Despite using a VPN, there’s always a risk of the VPN leaking your IP address through DNS or WebRTC leaks or misconfigurations when on a dark web forum or marketplace. Therefore, you must run an IP leak test to ensure that the VPN is working completely fine and is not risking your digital security. It doesn’t use JavaScript, meaning the website won’t track your activities or exploit vulnerabilities. The website allows a personalized searching experience, where you can search according to your geographical location, country-specific, and keyword or price-specific search results. Users can leave feedback on finalized orders, providing valuable insights into vendor reliability and product quality. Since 2020, 2easy has sold massive stealer logs with sensitive data like passwords, bank cards, and initial access credentials.