Alongside pills and powders, sellers offer passports, driver’s licenses and Social Security numbers—often bundled with “fullz” (complete identity profiles). The same forgers advertise printing templates and hologram overlays, turning any high‑resolution printer into a fake‑ID mill. I take great pride in my team of reviewers to provide high quality content that is informative and entertaining. Each review is thoroughly researched and written to ensure readers have a complete understanding of the subject matter. Hi, I’m William Jones, the administrator of the exciting website explainedthis.com, which offers movie, music, and book reviews. With a deep passion for entertainment, I created this platform to provide a trusted source of information for fellow enthusiasts who want to stay up-to-date on the latest releases and trends.
Understanding BlackCat Ransomware: Threat Overview And Protective Measures
Cryptocurrency enables buyers and sellers to exchange goods and services without revealing their identities, making it ideal for illegal activities. The biggest differentiator between the deep and dark web is that dark web activity is made anonymous through a variety of encryption and routing techniques. First — and this is strongly recommended — you should install a Virtual Private Network (VPN). Also, you need to use a privacy-focused browser such as the Tor network to connect via nodes and proxy servers, which are more secure and aim to anonymize traffic requests. The Tor browser is able to access the special domain names, with the suffix .onion, used in the dark web. ZDNET’s recommendations are based on many hours of testing, research, and comparison shopping.
Search Darknet
The dark web came into existence as an offshoot of government experiments with anonymous communication. Naval Research Laboratory, and the Tor Project, starting early 2000s, put this technology into the public domain, giving rise to the dark web. Even when explaining what is Dark Web, one should not focus only on negative cases. While its primary focus is based on criminal trades, there are many legitimate dark web uses for these onion services.
Final Thoughts: Is The Darknet Dangerous?
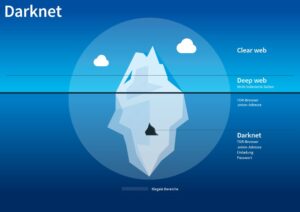
Thus, while the dark web carries significant risks, it also highlights complex issues related to privacy and expression in the digital landscape. The size of the Deep Web surpasses the Surface Web while remaining secure as an Internet zone. Almost 90% of all the websites are on Deep Web and are majorly used by Government agencies, corporations amongst others.
Anonymity And Privacy

While the Tor Browser hides your online browsing, it only hides your online activity through the Tor Browser. Because of the relaying of data through the onion nodes, and the encrypting and decrypting taking place at each node, your internet connection will slow considerably. This means the Tor Browser is not recommended for streaming video, playing games, or downloading large files.
- Indeed, most nations; including the United States, the United Kingdom, and India, allow access to the dark web as a lawful activity.
- Even if you never make a purchase, you could be watched and incriminate yourself for other activities later in life.
- The moderators enforce a strict policy against posting links to illegal products or services, so you’re more likely to find safer dark web addresses here.
- You’ve no doubt heard talk of the “dark web” as a hotbed of criminal activity — and it is.
Potential Risks And Threats On The Dark Web
In this article, we will dive deep into the world of “Dark” and explore the many layers of its plot, characters, and themes. We will examine the show’s time-traveling concept, the significance of Winden, and the characters that populate the town. We will also explore the symbolism and themes of the series, and analyze the show’s ending and its impact on the science fiction genre. Finally, we will delve into popular fan theories and unanswered questions, and conclude with our final thoughts on the show. The dark web’s origins are often traced back to March 20, 2000, with the launch of Freenet, a peer-to-peer sharing network designed to prioritize anonymity.

A Three‑Stop Postal Route For Data
Data gleaned from ransomware and data breaches is available on the dark web. Millions of customers’ personal data, including names, addresses, bank account and credit card account information, and many other forms of sensitive data. The users of the dark web are typically aiming to block governments from snooping on them. This can often be for political reasons, but also because they may be involved in illegal activities, such as the ones listed above. Unlike the surface and deep web, you can’t access the dark web via a standard or specialized search engine.
Confusingly, ‘Dark Internet’ is also a term sometimes used to describe further examples of networks, databases or even websites that cannot be reached over the internet. In this case either for technical reasons, or because the properties contain niche information that few people will want, or in some cases because the data is private. For example we have a ‘staging’ version of this very website that is blocked from being indexed by search engines, so we can check stories before we set them live. Thus for every page publicly available on Tech Advisor (and there are literally millions), there is another on the Deep Web. The dark web offers powerful privacy tools, but it also hosts real dangers—from malware and phishing to deanonymization and law-enforcement traps.
Name Of Browsers
Meanwhile, Facebook also offers dark web access to their social network. Darknet markets facilitate transactions for illegal goods and services. Silk Road was one of the first dark web marketplaces and it allowed users to trade multiple types of nefarious goods and services, including weapons and identity fraud resources. While many dark marketplaces have been shut down by authorities, new ones soon appear in their place. For instance, several major media organizations, including ProPublica and The New York Times, operate mirror versions of their websites on the dark web.
- Navigating the dark web requires extra layers of privacy, not just because of its content but due to legal scrutiny.
- The term “dark internet” can mean a lot of different things to a lot of different people.
- Phishing is when someone contacts you pretending to be someone else to gain access to your personal information, which often results in identity theft.
- Place a credit freeze or lock on your credit reports, monitor your credit reports and financial accounts closely for any unauthorized activity, and consider enrolling in a credit monitoring service.
You’ll need a purpose-built browser that uses The Onion Router (TOR) to access dark web content. Because of their anonymity, dark web sites are breeding grounds for illegal activity and transactions. For many people, the answer is by using regular websites such as Reddit. The moderators enforce a strict policy against posting links to illegal products or services, so you’re more likely to find safer dark web addresses here. Mail providers Mailbox.org and Protonmail can also be accessed via an .onion link.
All commonly public-facing websites accessed via traditional browsers like Google Chrome, Internet Explorer, and Firefox are contained here. Websites are usually labeled with registry operators like “.com” and “.org” and can be easily located with popular search engines. You don’t need special tools or a special browser like you need to access the dark web (more about that later). Anyone can access the deep web by using specialized search engines, dedicated web directories, and other sources that can help you find the data or information.
Organizations can also consider dark web monitoring services that search through data available on the dark web for anything related to their specific company or employees. Dark web monitoring can supplement other tools used to gather preemptive threat intelligence, such as the Mitre ATT&CK framework. As hoped, the Tor anonymous network grew in popularity among computer enthusiasts, privacy advocates, journalists, dissidents under repressive governments, and others desirous of strict secrecy. At the same time, Tor became an effective shield for the illicit sale of heavily controlled goods, such as guns and drugs. The Tor network also gave hackers, terrorists, and distributors of illegal pornography a secure method of communication.