A virtual private network (VPN) is a good way to mask Tor activities. It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor. The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. It will encrypt your traffic and data so no one can intercept it. Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web. As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing.
Method II – VPN Over Tor
That said, many of the actors on the dark web are highly skilled digital adversaries who can easily outmaneuver basic security measures. As a leading cybersecurity vendor, CrowdStrike cautions all organizations and individuals to refrain from using the dark web. Despite its legitimate uses, cryptocurrency’s untraceable payment nature has raised concerns around money laundering and illicit trade, driving regulatory scrutiny. To provide anonymity, Tor is generally quite effective, but not completely foolproof. If the person tracking you is very advanced and has unlimited resources, they could conceivably de-anonymize you when you make certain mistakes, like downloading files or enabling scripts.

Malware And Viruses

A VPN can help disguise your use of Tor and your visits to dark web resources. ZDNET tested the best VPNs available based on speed, number of servers, security features, price, and more. ExpressVPN is our pick for the best VPN overall, thanks to its fast and reliable connection and the wide range of platforms it works on. The area of the internet we access daily is known as the clear or surface web. When you click through from our site to a retailer and buy a product or service, we may earn affiliate commissions. This helps support our work, but does not affect what we cover or how, and it does not affect the price you pay.
Tor Metrics
The dark web is used by journalists, whistleblowers, and political activists who need the protections that it offers. Anything you need to do that has to be off the books to some extent, for noble or ignoble reasons, can be done on the dark web. It requires specific software and knowledge to access, creating a barrier that keeps casual internet users away. In short, the deep web is about restricted access, whereas the dark web is about engineered anonymity. On the software end, the use of Tor and other anonymized browsers is not strictly illegal. In fact, these supposed “dark web” browsers are not tethered exclusively to this portion of the internet.
- We also recommend using a virtual private network (VPN) such as NordVPN — the best dark web VPN — to add an extra layer of protection.
- Most of our usage of the “private” internet is through authenticated portions of the deep web.
- With only about 4 percent of all online content freely accessible (making up the surface web), the remainder is tucked away in the deep web.
- To counter takedowns, developers are turning to decentralized DNS systems like Handshake and InterPlanetary File System (IPFS).
- It is a good website for finding out which websites are currently working.
Unlike the Dark Web, which requires a special web browser called Tor, you can use any browser to get to the Deep Web. Perhaps the best-known thing you can buy on the Dark Web is information collected in what seems like the almost daily data breaches we read about in the news. That information can include checking and credit card account numbers, social security numbers, and other sensitive information. NordVPN offers a 30-day, no-risk trial subscription when you sign up on this page. This provides a full month’s access to all of the features of the #1 VPN for the Dark Web. This is an excellent way for Dark Web users to provide additional privacy protection when accessing the Dark Web.
How The Deep Web Is Different From Traditional Internet
Samson has over 3 years of experience writing about VPNs for Cloudwards. Apart from his professional endeavors, Samson is passionate about soccer and enjoys reading, table tennis and watching sports in his spare time. He has also contributed to platforms like Financesonline.com and Timeero.com.
The 10 Best Dark Web Browsers In 2025
Tails is a privacy-focused live operating system that you can boot from a USB stick. It is designed to be used without leaving a trace on your computer. It forces all internet connections to go through the Tor network.
Hidden Answers
Beyond the paywalled and pay-to-access content, the deep web has crawlable web pages that aren’t indexed because the owners have blocked search engine crawlers from accessing them. This includes websites in the design stage and draft blogs in content management systems such as WordPress. Law enforcement officials can exploit that weakness using “Tor-exit-node” monitoring techniques to expose users’ IP addresses and potentially trace activity back to the original users.
Deep Web Search Engines
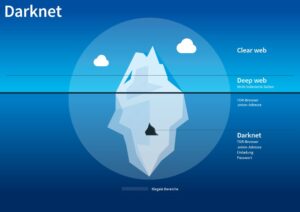
Others go somewhat deeper to download pirated music or steal movies that aren’t yet in theaters. If we continue to visualize the entire web like an iceberg, the open web would be the top portion that’s above the water. From a statistical standpoint, this collective of websites and data makes up under 5% of the total internet.
Which Is Better — Tor Over VPN Or VPN Over Tor?
In addition, they share information of great importance, about the Tor network and the Tor project. Legal uses include forums for free speech and privacy, while illegal activities may involve the sale of drugs, weapons, or stolen data. Opting for Forest VPN ensures your privacy remains intact while browsing the dark web. With its no-log policy and battery-saving technology, Forest VPN not only protects your data but also minimizes your carbon footprint. Many users have praised its ease of use and affordability, making it a popular choice for those venturing into the unknown territories of the internet.
Onion sites are websites on the dark web that use the ‘.onion’ top-level domain. They require the Tor browser for access, ensuring encrypted connections and anonymous communication. While criminal activity does occur on the dark web, how people choose to use the dark web is what matters. Merely exploring the dark web out of curiosity or for research purposes is typically not a problem. If your Social Security number is found on the dark web, take immediate action to protect yourself. Place a credit freeze or lock on your credit reports, monitor your credit reports and financial accounts closely for any unauthorized activity, and consider enrolling in a credit monitoring service.
Dark Web Search Engine
- We don’t want to leave you with the impression that everything on the dark web is nefarious or illegal.
- If your website is only accessible through the deep net, tracking down the physical location of your servers is much harder than it would be for a regular website.
- The dark web’s layered encryption and routing methods make it extremely difficult for security teams to identify who is behind malicious activities.
- That’s helpful because Tor can suffer IP leaks and malicious actors can run Tor servers.
Depending on your activity, it can be okay to look at the dark web, but we recommend using extreme caution and researching exactly where you want to go before you start clicking around. While many people use it for legitimate purposes, the dark web also hosts illegal activities that you don’t want to stumble upon or engage with. Most of what you see in search results is just a small slice of the internet. In fact, only about 4% of the web is indexed, meaning it shows up in standard search engines.
We don’t want to leave you with the impression that everything on the dark web is nefarious or illegal. The Tor network began as an anonymous communications channel, and it still serves a valuable purpose in helping people communicate in environments that are hostile to free speech. “A lot of people use it in countries where there’s eavesdropping or where internet access is criminalized,” Tiquet said. Dark web websites look pretty much like any other site, but there are important differences. Instead of ending in .com or .co, dark web websites end in .onion.
That’s how we were able to discover the remains of the RMS Titanic. The search engine crawlers do the same work as done by the explorer submarines. Law enforcement agencies all over the world are aware that the Dark Web enables criminality. This is why they carefully monitor the dark web and dark web marketplaces. In the digital world, “Deep Web” and “Dark Web” often get mixed up, leading to misunderstandings.