Our rigorous vetting process ensures that only the most reputable, trustworthy, and customer-centric platforms make it onto our platform. With our aggregator, you can say goodbye to endless searches and hello to a seamless shopping experience that delivers the finest cypher url and cypher darknet link at your fingertips. Elevate your shopping journey and discover the true potential of our exceptional cypher darknet aggregator. Labels can group similar nodes together by assigning zero or more node labels. Labels are kind of like tags and allow you to specify certain types of entities to look for or create. Our cypher url aggregator is more than just a platform – it’s a promise of uncompromising quality, customer-centric service, and a shopping experience that redefines the norm.
Dark Matter Market
This guide explains how to create a walkthrough (in slideshow format) for the Neo4j Browser that enables your audience to explore your database and model interactively. According to Cloudflare, the server name indication (SNI aka the hostname) can be encrypted thanks to TLS v1.3. Let’s see how it looks within the TCP packets of cloudflare.comSo, I caught a “client hello” handshake packet from a response of the cloudflare server using Google Chrome as browser & wireshark as packet sniffer. I still can read the hostname in plain text within the Client hello packet as you can see below.
Cartesian Products With Bounded Symbols
To optimize queries that fetch nodes with a certain label and property combination, you need to create a label-property index. For the best performance, create indexes on properties containing unique integer values. Cypher differentiates itself with an uncluttered yet dynamic approach. Among common items such as drugs and fraud-related materials, the market is a treasure trove of rare and intriguing products, each accompanied by engaging descriptions. It exclusively supports Bitcoin (BTC), Monero (XMR) for transactions, emphasizing the importance of privacy and security, and features a direct payment system for each purchase, catering to the needs of privacy-focused users. Cypher is an open data query language, based on the openCypher initiative.
Access The CSV File Path With File()
Create varied levels of message security with different coding algorithms. Accessing web-APIs is a simple task in all stacks and languages and JSON as transport format is ubiquitous. Using the neo4j-core Gem, we can talk to Neo4j Server or embedded (using jRuby) by just changing a single line of configuration. To pass in the JSON to Cypher we have to programmatically call the Cypher endpoint of the Neo4j server, which can be done via one of the many drivers for Neo4j or manually by POSTing the necessary payload to Neo4j. For each question we access the direct attributes but also related information like the owner or contained collections like tags or answers which we deconstruct in turn. With this API-URL below, we load the last 10 questions with the Neo4j tag.
Rewire Your Integration Strategy: A Graph-First Approach With Neo4j And AI
Elevate your shopping game and let our aggregator be your guide to the world of exceptional cypher website. The Cypher query language depicts patterns of nodes and relationships and filters those patterns based on labels and properties. Cypher’s syntax is based on ASCII art, which is text-based visual art for computers.
User Interface
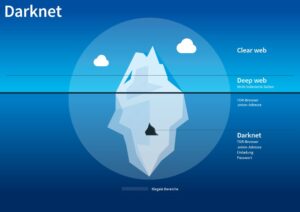
Just your app and the server will know any parameters sent through https. After a relational dataset has been imported, there may be further labels that can be added, depending on the use case.Additional labels can speed up pinpointing a node if you use them in your queries. Since 2020, 2easy has sold massive stealer logs with sensitive data like passwords, bank cards, and initial access credentials. It supports operations in multiple languages and operates on both clearnet and Tor.

Breadth-First Search
The Neo4j implementation of the Cypher parser, planner, and runtime is open source. As a cypher url enthusiast, I’ve tried countless online marketplaces, but this aggregator has become my go-to destination. The curation of cypher mirror is unparalleled, and I always find exactly what I’m looking for. I’ve been using this cypher website aggregator for months and I’m absolutely thrilled with the quality and variety of cypher darknet link it offers. The platform is incredibly user-friendly, and the customer service is top-notch. As in any query language, there are many commands in the form of reserved keywords and keyword combinations used to perform different actions.
So as you can see, even with LOAD JSON not being part of the language, it’s easy enough to retrieve JSON data from an API endpoint and deconstruct and insert it into Neo4j by just using plain Cypher. Here are some simple example queries that I now can run on top of this imported dataset. Use Qury API or Qury free singular cipher to encode your URL’s query string and hide sensitive data. Though both examples above are accepted by the interpreter, they are not equivalent and refer to two different types of Nodes/Relationships, and node properties follow this same logic. In the context of Neo4j, the interpreter itself doesn’t care how you write out your query so long as you follow the proper patterns such as surrounding Nodes with ( ) and Relationships with , etc.
Cast CSV Columns To Neo4j Data Types
The property graph data model is increasingly popular across a wide variety of application domains, with growing adoption in multiple products and projects. Cypher is the most established and intuitive query language to learn for working with property graphs. Cypher is Neo4j’s declarative query language, allowing users to unlock the full potential of property graph databases. Let’s start at the highest level with an overview of the structure of a graph database composed of Nodes and the Relationships between them. Loosely speaking, you can think of a single Node as being one row of data with the Label being the table name. The Cypher query language expresses this with symbols directly incorporated into the language syntax.
- At the heart of our cypher url aggregator lies a dedicated team of experts who meticulously curate the best online marketplaces.
- Let’s start at the highest level with an overview of the structure of a graph database composed of Nodes and the Relationships between them.
- Whenever you are not sure how to write a Cypher query, you can take a look at this cheat sheet and try again.
- It actually can’t negotiate even a single suite, but just proposing to negotiate is enough for servers to tell you if they support a suite or not.
- There is no better or faster way to get a list of available ciphers from a network service.
Additionally, a scarcely observed “Latest Orders” segment is featured in the lower left panel of the primary market screen, which exhibits the most recent purchases made by buyers on the market. Due to its relatively diminutive size, Cypher has waived the vendor bond for vendors who have conducted over 200 sales on other markets. Although the market has yet to gain as much momentum as its competitors, it exhibits no indications of deceleration. The Cypher Market, a relatively small darknet market, has been in operation for over three years, yet has not garnered significant recognition from the broader community.
- You can explicitly create indexes on a data with a specific label or label-property combination using the CREATE INDEX ON syntax.
- It tests connecting with TLS and SSL (and the build script can link with its own copy of OpenSSL so that obsolete SSL versions are checked as well) and reports about the server’s cipher suites and certificate.
- I can quickly generate different types of ciphers that actually work, which adds an extra layer of realism to my stories.
- Graph pattern matching sits at the very core of Cypher.It is the mechanism used to navigate, describe, and extract data from a graph by applying a declarative pattern.
I think I would be more inclined to write a custom browser guide than try to run queries from the url (which I’m not entirely sure is possible). Counting data from the dataset, to get an idea of how much data will get loaded. If you want to delete a node, delete its relationships first using DETACH. Not only is the URL available in the browsers history, the server side logs but it’s also sent as the HTTP Referer header which if you use third party content, exposes the URL to sources outside your control.

The file acted_in.csv contains data about the relationship between actors and the movies they acted in (from persons.csv and movies.csv).Actors and movies are linked through their ID columns person_tmdbId and movieId. Dark web markets have exploded in scale and reach in 2025, becoming the most dangerous hubs for trading drugs, stolen data, and hacking tools. These anonymous marketplaces—operating mainly on the Tor network—are now a primary threat vector for businesses and cybersecurity professionals. Cypher’s main advantage is simplicity for sellers and buyers alike. It doesn’t require previous dark web experience, extensive knowledge, or serious investments to sign in.