Steam accounts (Steam being the most popular store for PC games) are also sold on the black market and can be used for cash-outs or simply to gain access to games purchased by the victim. The term “fullz” is used by criminals on the darkweb when they are buying or selling stolen credentials. Use of fullz by bad actors presents a risk to businesses who allow for digital identity verification, as fullz give fraudsters a deep ability to impersonate a legitimate customer. Its site is active and stolen credit card data appears to be updated routinely. However, its continued ban from major cybercriminal outlets indicates that the site is still withholding payments. Carding forums — where cybercriminals chat about stealing card information, share tips for how to hack into websites and more — and marketplaces, where card data is actually bought and sold, are prolific on the dark web, Thomas says.
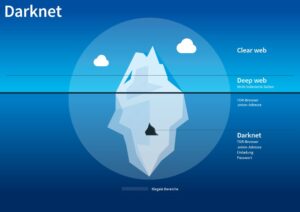
Detecting Dark Web And Deep Web Credit Card Fraud
While it offers unprecedented opportunities for communication, commerce, and innovation, it also harbors shadowy corners where illicit activity thrives. Among bclub these, digital black markets have become increasingly sophisticated, providing platforms for the trade of stolen financial data. One of the most notorious examples is Bclub, a private CVV2 shop known for its organization, exclusivity, and high-value offerings.
Table Of Contents
Another issue is that some sellers inflate their listings with fake credentials, such as generic email addresses like “exampleatgmail.com,” exploiting the high demand for domains like Gmail. Buyers see only the domain name before purchase, uncovering the deception only after the transaction is complete. For example, a hacker may first steal card data (dumps) and then use that information to gain access to an organization’s network via RDP. Once inside, they can extract additional sensitive data, such as CVV2 codes, which can then be sold for profit or used for fraudulent transactions. In the ever-evolving landscape of cybersecurity, the term “RussianMarket” has become synonymous with underground activities that pose significant threats to both individuals and organizations.
This information comes in several flavors, with “CVVs” and “dumps” being the most popular. While many cybercriminals are out to simply steal our information, satisfied with creating havoc for individuals or businesses, the majority do it for the money. Infosec Insider content is written by a trusted community of Threatpost cybersecurity subject matter experts. Each contribution has a goal of bringing a unique voice to important cybersecurity topics.
New Payment Processing Services
Looking at the actual numbers, we can identify the provinces with the most occurrences of credit card theft. Unfortunately it isn’t always possible to know with authority the origin of a card, as many shops and markets do not list the country of origin. However, this doesn’t prevent us from compiling the issuing bank of all those 50,309 cards.
The underground economy in which hackers operate is laden with forums, chat rooms, websites and other communities designed to facilitate, streamline, and industrialize cybercrime. Taking a look at what gets sold and traded in these communities can give us a pretty good understanding of what’s most valuable to hackers — and what we need to focus on protecting. IDScan.net offers the leading adaptive AI identity verification platform focusing on ID fraud prevention, age verification, and access management for security and compliance. If you’re in a coffee shop or anywhere else you don’t trust network security, use a virtual private network (VPN) to encrypt all communications. But if an attacker has access to an unencrypted network that you’re using, it’s easy to view your account data and steal or alter your information.
Unlike public forums, these platforms operate under strict access controls, creating a sense of exclusivity and trust among users. Criminals often obtain the information in fullz through hacking or data leaks. If you have been the victim of a company’s data breach, there could be fullz with your data available for sale on the Internet. In the relentless battle against cyber threats, financial institutions must deploy proactive strategies and technologies to mitigate risks and protect customers, especially in the context of compromised credit card feeds. Additionally, securing transactions with a 3-D Secure ACS (Access Control Server) solution plays a pivotal role in bolstering the overall fraud prevention strategy.
Simultaneously, customers face the risks of identity theft, damaged credit scores, and the emotional toll of financial fraud. Although there’s a variety of goods to be purchased on the dark web, one of the most sold resources by volume on the dark web, if not the most sold commodity, is stolen credit cards. Just last week, the largest carding site operator announced they would be retiring, after allegedly selling 358$ millions worth of stolen cards. Between October 2022 and February 2023, the BidenCash marketplace published 3.3 million individual stolen credit cards for free to promote the use of their services. The stolen data included credit card numbers, expiration dates, Card Verification Value (CVV) numbers, account holder names, addresses, email addresses, and phone numbers.
The Top 7 Dark Web Marketplaces In 2025

This marketplace has garnered attention for its illicit trade involving dumps, RDP access, and CVV2 shops. But what exactly do these terms mean, and why should they be a concern for you? In this article, we will explore the intricacies of the RussianMarket and the implications of its offerings.
How GC Buying Makes Selling Gift Cards For Bitcoin Simple And Instant
- By obtaining RDP access, criminals can execute various malicious activities, including data theft, installation of malware, and unauthorized financial transactions.
- These suppliers then sell this data to vendors such as Yale Lodge, where buyers can purchase them and use them to withdraw money from ATMs or make purchases online.
- Quality and validity of the data it provides justify its higher cost over other marketplaces.
- As the cost of the service increases and gets into the thousands of dollars, the technical skill required to execute the ransomware decreases sharply.
- This not only protects against financial losses but also reinforces customer trust.
A quick guide for developers to automate mergers and acquisitions reports with Python and AI. Use this guide to learn how to easily automate supply chain risk reports with Chat GPT and news data. Some fullz even include photos or scans of identification cards, such as a passport or driver’s license. The average price of a cloned, physical card is $171, or 5.75 cents per dollar of credit limit.
Assess Stablecoin Ecosystem Activity
With the advent of crypto-currencies, it became not only possible to complete trades online without leaving a money trail but easy. As a result, the trading of illegal goods online has become more commonplace, and vast dark web marketplaces have been created. No, black market websites operate illegally and pose high risks of scams, fraud, and law enforcement action.
Dumps are also credit card records but in their raw form (what’s on the magnetic strip of your credit card). Since this data is physically tied to the card itself, hackers need to skim the card. That can happen when it gets swiped on a POS device – the machines you swipe your card through to pay – or if hackers compromised the retailer’s network.

Impact On Financial Institutions And Customers
The BidenCash stolen credit card marketplace is giving away 1.9 million credit cards for free via its store to promote itself among cybercriminals. Increasing digital surveillance, stricter financial regulations, and the growth of cryptocurrencies have driven underground marketplaces to adopt sophisticated security measures. Platforms like Bclub combine selective access, encryption, and community-based oversight to maintain operations in a highly regulated digital world. The digital black market continues to evolve, driven by technology, anonymity, and demand for high-value financial data.
Top 5 Deep Web Black Markets
Dumps refer to the data extracted from the magnetic stripe of credit and debit cards. Cybercriminals are particularly interested in dumps because they provide direct access to an individual’s financial resources. The existence of Bclub’s CVV2 economy underscores the importance of robust cybersecurity measures. Financial institutions, e-commerce platforms, and regulators must remain vigilant against the misuse of cardholder information.