When possible, using a credit card instead of a debit card is a good move too. As data breaches become more common, and scammers grow more sophisticated, this is a reality many people are having to contend with. To make this theft more difficult, measures like personal information numbers (PINs) and security chips have been implemented, but hackers continue to find new ways to exploit weaknesses in the electronic payments system. Comparitech researchers sifted through several illicit marketplaces on the dark web to find out how much our private information is worth. The Australian Federal Police is also running two inquiries into who obtained and attempted to sell the data and protections for more than 10,000 customers whose records were posted online.
How Stolen Credit Card Information Is Sold

A credit card dump is the unauthorized digital copy of a credit card, where the data is stolen from either the physical card or through hacked payment networks. This illegally obtained information can have devastating consequences for consumers, leading to financial losses, potential long-term damage to their credit scores, and identity theft. Historically, some of the most significant credit card dump attacks have resulted in staggering numbers of affected consumers. For instance, Capital One’s 2019 breach led to approximately 106 million customers and applicants in the U.S. and Canada having their personal information compromised, including credit card details.
Passionate about blending creativity with functionality, Alex specializes in crafting visually compelling websites that drive results. His expertise spans across web design, SEO, and digital marketing, making him a key contributor to Web Design Booth’s mission of empowering digital creators. Joker’s Stash still has imitators that masquerade as the now-defunct site, researchers say, with the goal of capturing that old traffic.
Card Data And Markets
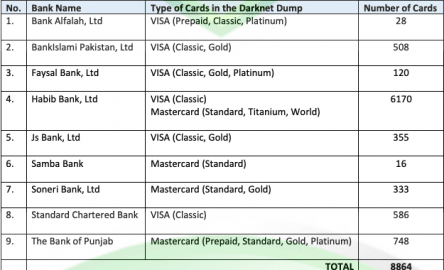
These groups invest in advanced tools, techniques, and infrastructure to target victims and monetize their stolen data. They sell the information in various forms, such as individual card numbers, cardholder details, or entire databases, depending on the demand and price range. Dark web transactions play a key role in fund transfers for credit card fraud.
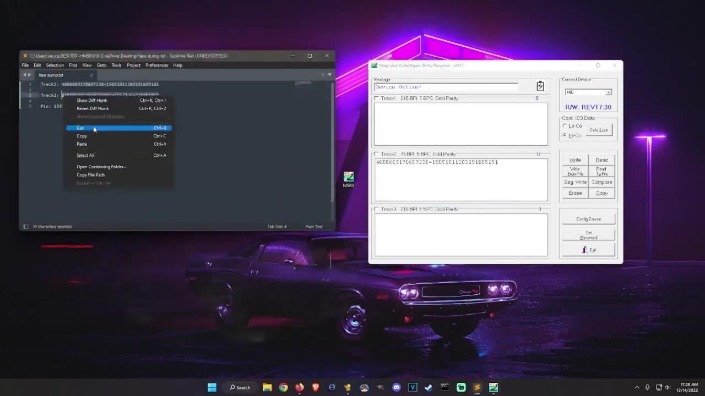
This information is then used to create counterfeit credit cards or make fraudulent online purchases. The term “dump” comes from the process of extracting the data from the magnetic strip. Cyberint, the Impactful Intelligence company, reduces risk by helping organizations detect and mitigate external cyber threats before they have an adverse impact. A team of global military-grade cybersecurity experts work alongside customers to rapidly detect, investigate, and disrupt relevant threats – before they have the chance to develop into major incidents.
Credit Card Skimming: Understanding A Common Method Of Obtaining Stolen Credit Card Information
Instead, credit card dumps involve the acquisition and sale of digital copies of card information. The stolen data is often sold in batches on the dark web or used by cybercriminals to commit large-scale online purchases. B1ack’s Stash’s emergence and rapid growth highlight the ongoing evolution of dark web marketplaces and the persistent threats they pose to global cybersecurity. By strategically releasing millions of stolen credit card details for free, the marketplace has garnered significant attention—both from cybercriminals looking to exploit the data and security researchers tracking its impact. B1ack’s Stash, a new dark web marketplace, recently gained significant attention by releasing 1 million stolen credit card details for free upon their debut on April 30, 2024. The carding shop promoted this giveaway through several known carding forums on the darknet to attract a larger customer base.
Google Previews Cyber ‘disruption Unit’ As US Government, Industry Weigh Going Heavier On Offense
Tor encrypts traffic, masks your IP address, blocks trackers and browser fingerprinting, and doesn’t store a record of your activity. Thank you for joining us on this exploration of credit card transactions on the Dark Web. Stay vigilant, protect yourself and others, and make ethical decisions when navigating the vast landscape of the internet. Now that we have covered the necessary steps to access the Dark Web safely, let’s move on to the process of buying credit cards on the Dark Web. When engaging in any transaction, it is essential to take protective measures and precautions to safeguard personal information and privacy. This includes using a secure and anonymous internet connection, using a reputable VPN (Virtual Private Network), utilizing trusted marketplaces and vendors, and practicing good online security hygiene.

Joker’s Stash, Once A Forum For Credit Data, Grows As Breaches Yield More Stolen Data
The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods. These platforms sell everything from drugs and fake IDs to weapons and hacking tools, resembling a digital black-market bazaar. Fill in your credit card/debit card details, including the card number, expiration date, and CVV. BidenCash shop was established in April 2022, following the seizure of other card shops and carding platforms by the Russian authorities. Since its inception, it has been attracting the attention of both old and new cybercriminal customers.
B1ack’s Stash is a dark web carding marketplace that specializes in the distribution of stolen credit and debit card information. Emerging on April 30, 2024, it quickly gained notoriety by releasing 1 million stolen payment card details for free, a strategy aimed at attracting cybercriminals to its platform. The market sells credit card information to users occasionally shares free credit card dumps (as seen below). In this blog, DarkOwl analysts take a deep dive into the market, how it operates and what the reaction to the site has been on the dark web. A credit card dump refers to a situation when criminals make unauthorized digital copies of credit card information, either by physically copying data from the card or through hacking the payments network. These stolen credit card details are then sold on the black market for illicit activities, including identity theft and unauthorized purchases.
Legal Consequences Of Fraud
This FAQ aims to clarify some of the most common questions regarding credit card dumps and their implications. Additionally, limit the number of people who have access to your credit card information. Be cautious when sharing your card details online, especially on social media platforms or unfamiliar websites. When making an online purchase, ensure the website is secure by checking for the padlock symbol in the address bar and “https” in the URL.
- Due to its extensive inventory and reputation for reliability, Brian’s Club has maintained a significant presence on the dark web.
- Xfinity is the name of Comcast Communications’ internet, TV, and phone service; it is the most significant cabled internet service in the states, with more than 32 million residential customers.
- The financial burden is immense, resulting in a loss of $5 billion to consumers annually.
- Stolen credit cards are often used to make purchases at specific sites that don’t have protections against fraud.
These listings can include information such as the BIN number, credit card number, expiration date, and CVV number. Credit card details can be sold as digital items on the dark web, with the basics costing around $17.36. Physical cards, on the other hand, are cloned from stolen online details and can be used to withdraw cash from ATMs. These checkers are often offered and sold on the dark web, and are complimentary tools that individuals and organizations use to verify credit card information.
In Which Countries Can I Buy Bitcoin With A Debit Card And Credit Card?
Credit card dumps can lead to a wide range of negative consequences for consumers, including identity theft, unauthorized transactions, and damaged credit scores. In some cases, victims may spend months or even years working to restore their financial situation. Companies that suffer from data breaches are required by law to offer free identity theft protection services to affected customers as part of their response efforts.
By offering free access to such a vast amount of stolen data, the operators aim to build credibility among cybercriminals and entice them to purchase premium services or datasets from their platforms. The stolen data reportedly includes a mix of credit and debit cards from major providers like Visa, MasterCard, American Express, and JCB. In this hypothetical scenario, let us study the actions of a cybercriminal, Alex.
Monitor your account statements closely for any unauthorized transactions. If you detect any suspicious activity, report it to your bank immediately. They can help you dispute the charges and may provide additional security measures such as a new card or a temporary freeze on your account.