It was created by “Tim Berners-Lee”, who was also the creator of HTML and the Web itself. However, unlike commercial search engines, This is run by a confederation of volunteers. The site started as a fork of the ahmia search engine, this will remain a central part of the site. At the moment they are making minor improvements to the search engine and working on the Beta version of their new link directory.
News RFERL & VOA
So take this guide as you explore where to go on the Tor Browser without risking your online security. Cybersecurity has to also cover everything physically on your computer too—which law enforcement or government authorities might have the right to seize if they come calling. If you want to be untraceable and undetectable, connecting to the dark web via the Tor browser is a major step towards that, but not the only step you’ll need. Support systems for victims are crucial in helping survivors of CP regain their lives and recover from the harm they have experienced. Comprehensive assistance, including counseling, rehabilitation, and legal aid, is provided to ensure the well-being and reintegration of victims into society.
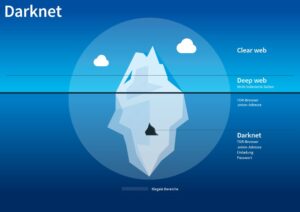
To access the dark web, you’ll need a specific set of tools – more about that later in the step-by-step section. The surface web (often referred to as the “visible web”) is the portion of the web available to the general public and indexed in the standard web search engines such as Google, Bing, and Yahoo. Pixel Privacy believes in digital privacy and does not believe in using it for heinous and/or illegal activities, and so the focus of this article will be on legal activities. When you access an onion site, your connection is routed through a series of nodes, each adding a layer of encryption. This process makes it nearly impossible to trace the user’s origin or destination, providing a secure browsing experience. Understanding and reporting CP content on the dark web plays a vital role in combating online exploitation.
What Is The Best Dark Web Search Engine?
These platforms monitor uptime and authenticity for many popular dark web sites, including forums, marketplaces, and directories. They list verified mirrors and often display digital PGP signatures posted by site administrators. These signatures are a powerful trust signal — they confirm the identity of the site’s operator and help you distinguish between real and fake versions. Haystak is a specialized dark web search engine with one of the largest indexes of .onion domains. Unlike surface engines, Haystak offers deep crawling and metadata previews to help users navigate through hidden content.
Since the dark web is a hidden and uncontrolled part of the web, there is a high amount of malware infections present there. As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. For this reason, you must watch out and avoid opening anything that looks suspicious to you. Your online activity and communications remain private and secret on the dark web. Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons. For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship.
Resources
Just bear in mind that the addition of anonymity to a platform like Reddit causes people to behave without a filter. However, for many, this appears to have been a simple publicity stunt, as they’ve since abandoned them. BBC News is still around, though, along with a handful of others, ensuring that users can access impartial information, wherever they are in the world. It is an archive stored on the Dark Web that keeps a snapshot of websites on the surface internet.
What Are The Best Onion Sites
Many surface web results claiming to link to the “real” Hidden Wiki are actually trap sites. These often include links to malware-infected downloads, phishing sites, or scam forums. Some are so well-built that they appear trustworthy until it’s too late. Even more dangerous are fake clones of legitimate services like SecureDrop. These clones mimic the design and purpose of the original, often going so far as to copy privacy statements and security warnings.
No, it isn’t illegal to browse the dark web, and there’s nothing inherently wrong with visiting a Tor website. Stay private with a tool like Surfshark’s Alternative ID to mask your contact details and use generated data on sites you don’t trust. Given the above threats, it’s a good idea to use Tor over a VPN to access the dark web.
BBC News /persian فارسی
The dark web (often referred to as the “dark net”, “black web”, or “black net”) is a small section of the deep web that is hidden and kept inaccessible to regular internet users on purpose. Using a VPN like Forest VPN not only enhances your security but also contributes positively to global causes. Forest VPN prides itself on not logging user data and offers an environmentally friendly approach by reducing CO2 emissions, thanks to its battery-saving technology. With competitive pricing, Forest VPN makes secure and ethical browsing accessible to everyone.
- Yippy is a search engine that started in 2009, since then it has evolved.
- It can only interact with the gateway, the most effective method by which the browser protects user applications from learning a device’s IP address.
- By following these precautions, you can explore the dark web with a greater degree of safety and security.
- Because Tor is very slow, many dark web-only websites avoid complex designs and fancy graphics to deliver a faster experience.
- Victim-centered approaches focus on providing counseling, rehabilitation, and legal aid to individuals who have been exploited and abused.
Why Use The Hidden Wiki Instead Of Google?
The dark web is not easily accessible, especially with browsers like Chrome or Safari, as it requires specialized protocols like Tor’s onion routing. As a result, the recommended browser for accessing the dark web is the Tor (The Onion Router) browser. But the reality is that millions of people rely on the social media platform to keep in contact with friends and family all around the world. It’s also a place for discussion and organization during political unrest.
We check all comments within 48 hours to ensure they’re real and not offensive. By following these precautions, you can explore the dark web with a greater degree of safety and security. Ahmia promotes transparency by being open-source and allowing contributions. Its operations focus on respecting user privacy and maintaining anonymity through the use of the Tor network.
- Therefore, if you do decide to explore it, exercise extreme caution.
- Both DuckDuckGo and Ahmia are safe choices for finding Tor Browser links without being tracked.
- These clones mimic the design and purpose of the original, often going so far as to copy privacy statements and security warnings.
- The New York Times can also be anonymously accessed via the dark web.
- Tl;dr – HTTP-over-Onion should not be considered as secure asHTTPS-over-Onion, and attempting to force it thusly will create afuture compatibility mess for the ecosystem of onion-capable browsers.
Just bypass your standard web browsers and fire up your tor browser to get on the dark web to access one of the best tor sites. Clicking on random onion links is quite risky and isn’t recommended. A random dark web link can lead you to malicious software, phishing sites, and illegal content. It’s a part of the internet that’s less regulated and more shadowy, for better and for worse. The distribution of child pornography (CP) on the dark web is a grave issue that demands urgent attention. It is essential to understand the nature of the dark web and the distribution methods of CP to effectively combat this illegal and harmful activity.
What Are Tor Onion Services?
ZeroBin is a minimalist paste-bin tool that allows users to share text securely and privately on the Tor network. Insights like these help researchers and advocates understand how and why Tor is being used. With this info, the wider online community can grasp Tor’s impact and its ability to provide secure and anonymous internet access. Although Hidden Answers offers an outlet for anonymous dialogs, users should stay cautious while browsing.