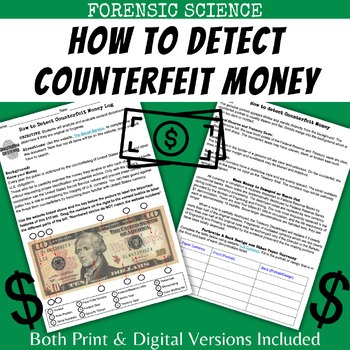
The quality of counterfeit bills varies, with some almost indistinguishable from genuine currency. Correct super notes offers you the best undetectable counterfeit money with features like security strip,water mark, hologram, passes the UV test and pen test. At Dark Web Notes, our experts use cutting-edge technology to create the best fake banknotes and security paper for documents that convey value, identity, and confidence.

Dark Web Counterfeit Money Vs Real,dark Web Sites Counterfeit Money,deep Dark Web Counterfeit Money
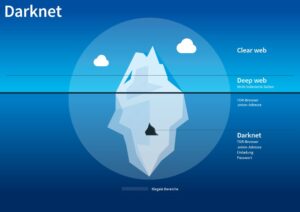
One of the most significant barriers to finding deep and dark web sources is that you must use the exact URL to access sources that are not indexed — even with a browser like Tor. For example, to access the popular dark web forum CryptBB, you must know the exact onion link; conducting a web search for the forum will not turn up anything useful. Many dark web sites deploy tools that prevent bots and web crawlers from accessing the site. Some well-known underground sources can be easier to find because there are dedicated sites that share links and maintain regular status updates. But in many cases, finding the exact URLs through manual search methods can be next to impossible.
These tools include for example different types of checkers, which assist threat actors in verifying whether the stolen card information they possess is valid and can be used to make unauthorized purchases. Since the Dark Web is a collection of websites that are only accessible via darknets, let’s take a moment to define what darknets are. Darknets are encrypted overlay networks that sit on top of the public Internet.
Enhance Your Business Resilience By Securing Your Mainframe
Some fake sellers take your crypto and never ship what you ordered, or phishing sites that look like real marketplaces but steal your login info. And then there’s malware—click the wrong link or download the wrong file, and your device could get infected. Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in. By supplying stolen data, these dark web links fuel many online scams and identity theft operations, playing a critical role in the darker aspects of the internet. All of these features, its competitive pricing, along with the volume of credit card information listings, make Real and Rare one of the prime sites to trade credit card information online.
Contact Details
The sheriff is encouraging businesses to check for the watermarks and lines that are on real $100 bills. “The money really looked good. The feel of the bills was the giveaway,” Powell stated. “As far as marking them with the pen, they would mark true as a good one hundred dollar bill but the texture of the bill was different.” After looking at all of the receipts, additional agencies were contacted because they indicated the counterfeit money was passed at many other locations.
Without a proactive cybersecurity strategy, businesses risk severe financial losses, reputational damage, and even legal repercussions due to compliance violations. Wizardshop.cc was established in 2022, and offers a wide range of leaked CVVs, database dumps and even RDPs. In the past 6 months, the site has increased the volume of cards sold, placing itself as one of the top sites selling credit cards today.
Q1: Is It Safe To Access The Darknet For Legitimate Purposes?
If you have suggestions on additional sections—projects, certifications, or portfolio links—feel free to propose them.If crafting results-driven tech resumes is in your wheelhouse, I look forward to collabo… End-to-end test with a dummy prospect shows data flowing from intake through signed engagement to kickoff project without manual intervention. I receive a short hand-off guide (written or video) explaining how to tweak each stage.If you have deep SuiteDash experience and can script Zapier/Make or native API calls where needed, this should be straightforward. Let me know your proposed timeline and which integrations or custom fields you foresee so I can provide access promptly…. The Darknet, often referred to as the “dark web,” Darknet Counterfeit Money For Sale Deep Web is a part of the World Wide Web that is intentionally hidden and can’t be accessed through standard web browsers. It operates on encrypted networks and requires specialized software like Tor to access.
US Takes Down Illegal Cryptocurrency Mixing Service Samourai Wallet
- Buyers put forward justificatory strategies for using counterfeit currency.
- Well, not all clients have a good mastery of the tor private mode browser.
- I want some developer who can work full time on this project because I am fed up with developers working on multiple projects and project getting delayed.
- The site also has a unique news section, listing new leaks and their size.
- It also opened the way for sharing illegal pornographic material and pirated data.
This guarantee underpins your financial wellness, safety, and security upon the invoice of our money. It’s supported by our performance history of duplicating the world’s most popular counterfeit money offers for sale online and having no issues on the client’s side. The Darknet’s counterfeit money trade remains a disturbing facet of the digital age.

Is The Dark Web Illegal?
The illicit activities of fraudsters are happening across the Gray, Deep, and Dark Web. But the real battle against fraudsters is on the Deep and Dark Web, where tracking their activity is much more difficult. Choosing the right Cyber Threat Intelligence platform can be the best weapon to win the war and protect your organization and customer data. Deploying a CTI solution will allow you to monitor and gather data on what’s happening on the Deep and Dark Web get alerts on activity specific to your organization. Unlike the Dark Web, sites on the Deep Web can be accessed using normal web browsers like Firefox, Google Chrome, and Safari. Also, these sites are often linked to publicly accessible pages, making them findable and accessible by users with the right login credentials and willingness to pay.
Top Grade Fake Bills
We profit from our work, but money doesn’t directly dictate our development. We’re up for experiments — that’s how we stay the industry pioneers.About the RoleWe are looking for a passionate and proactive Community Manager to lead and grow our German-speaking community. You will be the bridge between our product team and the community, ensuring our users are engaged, heard, and supported. We don’t want to leave you with the impression that everything on the dark web is nefarious or illegal. The Tor network began as an anonymous communications channel, and it still serves a valuable purpose in helping people communicate in environments that are hostile to free speech. “A lot of people use it in countries where there’s eavesdropping or where internet access is criminalized,” Tiquet said.
Understanding The Darknet
There are a number of legal retail stores where criminals can purchase prepaid credit cards in an open loop while remaining anonymous. The next stage is when they launder money in a method that is called “smurfing”, in which offenders load hundreds of prepaid cards, while avoiding identification procedures, but still meeting the KYC threshold. Then they claim to sell the loaded cards but their buyers unknowingly purchase an empty prepaid debit card.
It also opened the way for sharing illegal pornographic material and pirated data. One of the key tools used on the Dark Web today was first released in 2002 – Tor, The Onion Router. Users gain greater anonymity online when using Tor because it encrypts Internet traffic and passes through several nodes. Government developed Tor so their operatives could remain untraceable. You can also find websites to download copyrighted material such as music, movies, games, software, and even Netflix credentials. Some downloads contain malware for the fraudsters to hack the unsuspecting user later.