The site has a unique news section, where the admin updates the buyers about new leaks and dumps, the source of the dumps, structural site updates and more. Another unique feature Brian’s Club has is the auctions it offers during which users can reserve, bid, and outbid other users who want to purchase exotic BINs. Active buyers are also eligible for free gifts and dumps depending on their volume. Since then, BidenCash has continued to operate using the “dumping” method. This involves adding daily listings of stolen credit card details to the site and periodically dumping large amounts of stolen credit card details at the same time.
Accessing Dark Web Sites
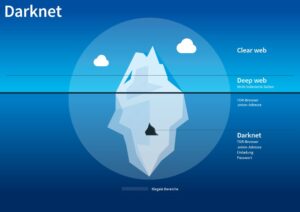
What most people think of as the “Internet” or the world wide web is actually what is known as the Surface Web, or Clear Web. This is the part of the Internet that is visible to search engines like Google and accessible via normal web browsers. The Gray Web is referred to the part of the Surface Web where fraudsters discuss or research their activities. However, the Surface Web represents only the tip of the iceberg when it comes to the internet – the majority of it is actually hidden. Protecting yourself and your organization from fake document fraud begins with proactive measures aimed at safeguarding personal data and strengthening overall security practices. While complete protection may not always be possible, consistently applying strong preventive steps can significantly reduce vulnerability to identity fraud and misuse.
Even so, they concede they may never crack the counterfeiter’s dark web of secrets. As he drove out of his gravel driveway in Noble on May 17, 2018, a 10-car convoy of federal and local law enforcement officials led by the U.S. U.S. postal inspectors studied Johnson’s tracking numbers and examined dozens of bags of mail.
Police Swoop On Suspected Darknet Fake Banknote Buyers
Law enforcement officers conducting routine traffic stops, public event checks, or investigations often detect counterfeit IDs through portable scanners and specialized software. Officers are trained to recognize physical inconsistencies like poor printing quality, incorrect fonts, mismatched data, or suspicious behavior. Additionally, verification against national databases can instantly identify fraudulent documents, resulting in immediate arrest or further investigation.
The goal of TOR was to allow secure communication by intelligence sources in dangerous environments and has since been adopted by the general public for secure, anonymous browsing. The scale and impact of the Dark Web expanded with the development of cryptocurrencies like Bitcoin, which allow semi-anonymous financial transactions to be performed on the Internet. Purchasing and using fake IDs or fraudulent documents from the dark web is a high-risk endeavor that carries severe legal, technical, and ethical consequences. Although counterfeit documents might initially seem attractive due to perceived convenience or anonymity, the dangers far outweigh any temporary benefits. Users face significant legal penalties, including hefty fines, criminal charges, imprisonment, and permanent damage to their personal and professional reputations.
A quick guide for developers to automate mergers and acquisitions reports with Python and AI. Learn to fetch data, analyze content, and generate reports automatically. These details are needed for physical use such as withdrawing money from ATMs.
Credit Card Monitoring Alerts
Hence, you never know when a popular .onion site is going to vanish, or even die. Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though). The best thing is to actually understand how to find the fresh, new links.
How To Delete Yahoo Account In 2025
Within a month, thanks to analysis by Secret Service experts in Washington, the agents knew they were chasing Daniel Johnson, a notorious counterfeiter who had been printing and passing fake bills since at least 2015. An analysis by Secret Service experts linked the fraudulent bills to thousands of others that had been passed with a total face value of $4.1 million. That made Billmaker the nation’s most prolific domestic counterfeiter. Reporting from Savannah, Ga. — When Secret Service Agent Matthew Britsch began trawling for major counterfeiters in the shadowy marketplaces of the dark web, he acted like any smart consumer on eBay — he studied the reviews.
Posts By Angus Bancroft
Therefore, you can prevent this exploitation by setting up a non-admin account. ActiveX and Java frameworks are susceptible to being exploited by hackers. Since you are navigating in uncharted territories with all the myriad threats today, you’ll have to disable them in your network settings to stay safe. You risk being targeted for attacks if you explore the dark web without protection. The threat can extend to your entire network of devices connected to the internet. Many services that are allegedly offered on the dark web are scams.
Table Of Contents
- Ultimately, addressing fake document usage necessitates more than law enforcement—it requires broader societal reflection and moral education emphasizing integrity, accountability, and the importance of shared societal values.
- Yet, even seemingly minor infractions have ripple effects, leading increasingly to public calls for stronger enforcement and accountability.
- A network browser gives you access to sites with the ‘.onion’ registry operator.
- He even had a loyal fan base who praised his work and customer service with scores of positive reviews.
- The Deep Web, which includes sites accessible via normal browsers but not visible to search engines, makes up a much larger portion of the Internet.
Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links. It is one of the most notorious credit card shops on the dark web. It has built a reputation for being a reliable source of stolen credit card data and PII.
Torzon Market
Dark web forums are online platforms that can only be accessed using anonymous networks, mainly Tor…. This will help you to remain anonymous and secure at all Tor entry and exit nodes. It uses TrustedServer technology on the entire server network to wipe out your data after every session. The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. It will encrypt your traffic and data so no one can intercept it.
It’s a wallet, explorer service, not a dark web marketplace itself, but still a helpful resource. It is a hub for financial cybercrime and offers a wide range of illicit services and stolen data that cater to sophisticated cybercriminals. Wizardshop.cc was established in 2022, and offers a wide range of leaked CVVs, database dumps and even RDPs. In the past 6 months, the site has increased the volume of cards sold, placing itself as one of the top sites selling credit cards today.
Legitimate Use Cases For The Average User
In today’s digital era, where information is constantly on the move across all digital platforms, an… If the VPN connection fails, the automatic kill switch will kick in, temporarily breaking your traffic. The provider also offers a dedicated CyberSec suite that prevents annoying ads and blocks malware and trackers. This includes military-grade 256-bit encryption reinforced with a 2048-bit DH key and SHA2-384 authentication to ensure your traffic arrives at its destination safely.

Marketplaces For Everything Illegal
These Deep Web sites are not indexed by search engines, making them impossible to find via traditional search engines like Google, Bing, etc. It’s safe because we don’t reveal your details right here or when contacting you. Please define the amount of cash you’d like to get and fill in various other called-for areas to buy funny money. When our crews work on actual and fake money offer for sale, they leave no rock unturned in researching the banknote variations that are currently distributed in your region.

The bills were even treated with iodine in case a money pen was used to test their authenticity. Taking the necessary precautions makes tracing your activities on the dark web difficult. For example, I strongly advise using a reliable VPN like NordVPN. Although the Tor browser has sufficient encryption, combining it with a VPN offers better protection.