In fact, it accounts for a huge chunk of the $914,349,424 lost to credit card fraud. With carding becoming a bigger threat than ever, it’s wise to learn more about it and take protective measures. Read along to find out how it works, red flags to watch for, and tips for keeping yourself safe. Chinesecybercriminals have become highly active in defrauding consumersworldwide by exploiting NFC technology and leveraging specializedtools to abuse NFC-enabled point-of-sale (POS) terminals.
Why Cybercriminals Use Dark Web Forums
Law enforcement agencies face significant challenges in tracking down and shutting down these illicit carding sites due to the dark web’s encryption and decentralized nature. Typically, fullz are most valuable on dark web markets, and useful to threat actors, when they include payment information and logs (See Figure 1). They are commonly utilized to cash out money from the victims’ accounts, as the complete PII in possession of the threat actor can be exploited to bypass online banking verification processes. Crucially, she also outlines what service providers—including telcos, financial services, and insurers—can do to help protect consumers from carding in today’s shifting cyber threat landscape. Stolen credit card details can be categorized into different types, making it easier for cybercriminals to exploit them. Ultimately, successful future defense against carding will require collaborative efforts among financial institutions, technology providers, law enforcement agencies, and consumers.
- Banks use sophisticated fraud monitoring systems to continuously oversee credit card transactions.
- They’ve essentially created a parallel economy with its own reputation systems, escrow services, and even customer support channels.
- While this does not prevent cracking, it makes it more difficult for criminals to create large numbers of fake accounts, and renders it almost impossible for them to take over existing accounts.
- For instance, in January this year, it was the target of Operation Talent, the law enforcement initiative that was coordinated by the FBI and international agencies.
The site was infamous for using the image of former US President Donald Trump for its branding. Some new forums joined the underground scene in 2023, including BlackForums, a blackhat forum that specializes in database leakage and contains discussions about malware and tools. The forum remains comparatively small with just over 2,500 members but is noteworthy for partnering up with the ThreatSec hacktivist group. The RAMP forum is also considered “friendly” to Exploit and XSS, with one key differentiating factor. The forum widely accepts discussions about ransomware and seeks to welcome actors speaking languages other than English and Russian.
Frequently Asked Questions (FAQs) About Dark Web Marketplaces
Solutions like Stripe Radar, Sift, and ThreatMetrix use machine learning and global fraud data to block high-risk transactions automatically. In a global enforcement operation, U.S. authorities seized over 145 domains tied to BidenCash, a major carding marketplace launched in March 2022. A single campaign may test thousands of cards within minutes, overwhelming servers and bypassing simple rate-limiting tools. We will discuss what carding means, how it operates on the dark web, and most importantly, what businesses can do to defend themselves against this costly threat. Limit the personal information you share on social media or other online platforms.
What We Know So Far About The Supposed ‘Mother Of All Data Breaches’
Bots also enable the carder to rapidly change the IP address from which they are attacking, which makes it much more difficult for traditional anti-fraud technologies to identify and block an attack. Moreover, it’s essential to provide the company staff with enough training as well as defined objectives of what they should look for to bolster the monitoring efforts. Perhaps that’s their option for generating consistent traffic and a steady influx of new members. Perhaps its strong community is helping the administrators to keep the forum alive after all the attempts by authorities to seize. Russian Anonymous Marketplace (RAMP) is a hybrid marketplace that strongly focuses on ransomware groups.

Protect Against Carding And Other Fraud
Throughadvanced tooling and techniques, such as the “Ghost Tap”method and remote transaction relays, they can bypass detectionsystems and cause significant financial damage to victims. The globalnature of NFC payments and the anonymity provided by money mules andencrypted communication channels make these fraud operationschallenging to track and shut down. Typically,these merchants have a daily limit, so cybercriminals are alwayslooking for new ways to scale their operations by adding new moneymules who can open accounts for a commission. Traditional payments typically require some Cardholder Verification Method (CVM) such as PIN or signature.
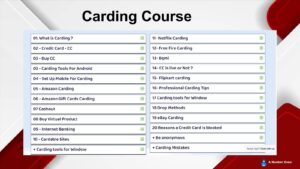
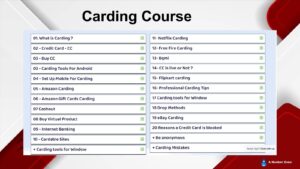
A combination of factors—law-enforcement action, increased defenses, the list goes on—has many threat actors predicting the death of carding entirely. Carding sites facilitate the trade of stolen card data, tools and tutorials, often operating on the dark web. The data posted on these online illicit shops is a goldmine for threat actors who are looking to commit financial crimes.
Engaging in such activities not only causes financial harm to individuals and businesses but also perpetuates a cycle of illegal actions. The victims of carding may suffer significant financial losses, damage to their credit scores, and emotional distress. Moreover, the profits made from carding often fund other criminal activities, such as drug trafficking or human exploitation. By offering free access to such a vast amount of stolen data, the operators aim to build credibility among cybercriminals and entice them to purchase premium services or datasets from their platforms. For instance, cybercriminals can buy credit card details with a $5,000 balance for just $110.
Protecting Yourself From Credit Card Data Theft
The app sets up the execution environment, loads encrypted native libraries, and dynamically replaces the visible application with the real one at runtime. This multi-layered initialization allows the app to evade static analysis and delay execution of malicious components until runtime, effectively hiding the bulk of its behavior from traditional analysis tools. After successful payment forlicense activation, it can be downloaded as an Android softwareinstallation package from a host generated by the Telegram bot.
Why Monitor Dark Web Hacker Forums?
Bots can attempt thousands of transactions in a short period of time to identify valid combinations at scale. For example, if the carder has a card number and expiration date, but not the 3-digit CVV code, a bot can very quickly attempt transactions using all 999 possible codes until the correct one is identified. Specifically, she’s crazy about the three C’s; computing, cybersecurity, and communication. In today’s digital era, where information is constantly on the move across all digital platforms, an… It routes your connection via several encryption servers to help you stay anonymous and secure.
Moreover, Exploit dark web forum features a highly organized structure as well as membership policies that make it attractive to most threat actors. The controlled and professional landscape has led many people to view the forum as the most reliable source. Its popularity can be as a result to the ease of use on it, as the forum features a clean and accessible design with enhanced moderation and a wider scope of the leak topics and sources. But disputing fraudulent charges is a hassle, and carding can have other impacts including negatively affecting your credit score, so it’s important to take steps to protect yourself. This latest pack is the fourth credit card dump the carding market has released for free since October 2022, with the previous leaks counting 1.22 million, 2 million, and 230,000 cards.
- Awareness and education are critical first steps toward reducing vulnerability to these sophisticated and pervasive forms of cybercrime.
- NFC fraud can result in significant financial losses, especially when attacks are scaled.
- Launched in March 2022 as a successor to RaidForums, BreachForums quickly became one of the leading forums for discussing data breaches and sharing stolen information.
- By understanding their inner workings and staying one step ahead in the ongoing battle against cybercrime, we can strive to create a safer digital landscape for all.
- Even highly secure financial institutions and payment processors are vulnerable to data breaches.
After buying stolen credit card information, fraudulent actors use carding bots to validate the information. These bots automate the process of making small transactions on e-commerce websites to test if the card is active, and they can be used without triggering fraud alerts. Card data on the dark web is a valuable commodity, and it’s often sold on specialized marketplaces known as Card Shops. These platforms are hubs for cybercriminals to buy and sell compromised payment card details. These platforms serve as hubs for cybercriminals to easily buy and sell compromised payment card details, including credit card numbers, CVV codes, expiry dates, and cardholder information.
The dark web’s decentralized nature makes it challenging for law enforcement agencies to track down and apprehend carders. In other words, you can say that the dark web and deep web communities (forums) are a breeding ground for cybercriminals, malicious schemes, and black market activities. Unlike the normal social platforms, these forums are mainly focused on cybercrime discussions, offering anonymity, access to high-value digital data, and escrow services. Cybercriminals use a range of nefarious technological and social engineering techniques to steal credit card information. And, once obtained via malware, phishing, or card-skimming attacks, the data may be sold or shared with other crooks on so-called carding forums. The BidenCash stolen credit card marketplace is giving away 1.9 million credit cards for free via its store to promote itself among cybercriminals.
Those involved in carding activities can face severe legal consequences, including imprisonment and hefty fines. Law enforcement agencies worldwide are actively working to identify and prosecute carders to deter cybercriminals from engaging in these illicit activities. The carder authenticates card numbers en masse by deploying a bot network to attempt small purchases on multiple online payment sites. The bots will plug in different combinations of credit card numbers, expiration dates, and CVV codes until a transaction goes through. Once the card information is authenticated, the carder can either purchase gift cards online, clone a physical card, or resell them on the dark web for a quick profit. There’s more to it than just sharing things such as hacked databases, stolen credentials, exploits, or hacking tools.
As technology continues to evolve, so too will the methods criminals use to exploit credit card data, prompting an ongoing arms race between fraudsters and cybersecurity experts. The future landscape of carding will undoubtedly see significant shifts driven by emerging technologies, evolving criminal strategies, and proactive legislative efforts. Finally, criminals “cash out,” converting assets like resold electronics, gift cards, or cryptocurrencies into cash. This final stage completes the monetization cycle, allowing criminals to realize profits from stolen card information. Immediately upon completing the transaction, buyers receive access to the purchased data. This information is usually delivered electronically within the marketplace, either displayed directly or provided as encrypted files accessible via secure downloads.