To combat the trade of falsified academic credentials, educational institutions can implement improved security measures, such as holograms or unique identifiers, on their official documents. The sale and use of stolen SSNs on the dark web constitute criminal activity and can lead to severe legal consequences for all parties involved. Law enforcement agencies actively track and investigate individuals engaged in the trade of stolen personal information, working to disrupt criminal networks and bring the perpetrators to justice. The trade of SSNs on the dark web enables criminals to assume someone’s identity, open fraudulent bank accounts, file false tax returns, or commit various types of financial fraud.
- Talk to our cybersecurity experts at WebOrion and let us help you stay two steps ahead of the bad guys.
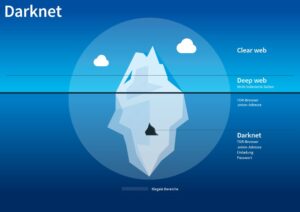
- Content and services on the deep web are accessible through a regular browser.
- Even if you still have a regular in-person dealer that you trust, they may not know what they’re selling, or, for that matter, be able to find a supplier whose gear isn’t compromised.
- The shop accepts payment through Bitcoin and Monero, while some vendors accept the coins.
What Is The Dark Web? How To Access It Safely?
This involves implementing robust data protection protocols, enforcing strict access controls, and educating individuals about the importance of securing their personal information. Education and awareness play a crucial role in protecting against DDoS attacks. Individuals and organizations should stay informed about the latest attack techniques, implement responsive security measures, and employ services that provide DDoS protection.
That’s finally starting to shift, and it looks like one of Google’s productivity apps is the heir apparent. The company’s Google Docs solution (or to be specific, the integrated word processor) is cross-platform and interoperable, automatically syncs, is easily shareable, and perhaps best of all, is free. – Remain cautious of vendors with no or limited feedback, as it becomes more challenging to assess their credibility and reliability. – Examine the feedback relevance and authenticity by considering the comments and overall sentiment expressed by previous buyers. Next, we will explore the significance of evaluating seller feedback and ratings on the Dark Web and how it can assist in making better purchasing decisions. The passport market is a particularly interesting one and can be divided into three main categories.
Tor2door Market

Others are looking for stolen data, hacking services, or even banned books and political content. For sellers, it’s often about making money while staying off the radar. Some are looking for illegal stuff they can’t buy elsewhere, like drugs or counterfeit documents. The story of dark web marketplaces kicks off with Silk Road, launched in 2011.
Step 3: Picking Your Darknet Market

That information can include checking and credit card account numbers, social security numbers, and other sensitive information. Credit card details are highly sought-after commodities on the dark web, where cybercriminals buy and sell stolen card information. These stolen credit card details include the cardholder’s name, card number, expiry date, and security code, which can be used to make unauthorized purchases or engage in fraudulent activities. Law enforcement agencies worldwide are actively engaged in combating the trade of hacking tools and services on the dark web. They work closely with international partners and cybersecurity experts to identify and apprehend individuals involved in these illegal activities. The dark web is home to a vast marketplace where individuals can acquire hacking tools and services.
Of Drugs Bought On Dark Web Are Not As Advertised
Some vendors offer services to help people “clean” illegally obtained funds using cryptocurrency and fake transactions. They mix and transfer funds through various privacy wallets and escrow services to hide the original source and make the illicit transactions harder to trace. Whether you want some pharmaceutical products (drugs) or digital items, you will probably find the products here, and that too at affordable prices. Vice City listens to the problems faced by its customers and vendors and solves them so that they can keep using the platform with ease.

Is The Dark Web Illegal? Everything You Need To Know
The best way to protect yourself from the dangers of darknet markets is to simply avoid them altogether. Even browsing these sites can put you at risk of malware infections or attract unwanted attention from law enforcement. BidenCash became known for regularly leaking huge amounts of stolen credit card data and personal information — often for free. This strategy, along with a strict sign-up process, helped it grow fast.
How Much Is Your Personal Information Sold For On The Dark Web?
The dark web provides a secretive platform for individuals seeking anonymity to conduct their online transactions. This anonymity, combined with the use of cryptocurrencies such as Bitcoin, makes it appealing to those involved in illegal activities. It is crucial to understand that engaging in illicit transactions on the dark web is not only illegal but also poses significant risks to both buyers and sellers. The dark web, a hidden part of the internet that requires special software to access, has gained notoriety for being a hub of illegal activities. In this article, we will explore some of the popular items that people buy on the dark web. It’s one of the largest darknet markets that launched in 2022 and trades sensitive financial credential transactions.
Marie had never purchased drugs in the conventional way—and still hasn’t. Major marketplaces like Silk Road, AlphaBay, and Hansa Market have been shut down through coordinated global efforts. Privacy-conscious users, including journalists and political activists, use the dark web to communicate securely, especially in oppressive regimes. Farwa is an experienced InfoSec writer and cybersecurity journalist skilled in writing articles related to cybersecurity, AI, DevOps, Big Data, Cloud security, VPNs, IAM, and Cloud Computing. Also a contributor on Tripwire.com, Infosecurity Magazine, Security Boulevard, DevOps.com, and CPO Magazine. When you use it, all the web traffic automatically routes through Tor.
Technology can play a role in combating the trade of fake diplomas and certificates. As advancements in digital credentials emerge, utilizing secure and tamper-proof digital platforms can enhance the verification process, making it more reliable and efficient. Organizations have a responsibility to implement robust security measures to protect user account information. This includes enforcing password requirements, implementing multi-factor authentication, encrypting sensitive data, and educating users about best practices in account security. Government agencies and organizations must continually improve security measures to protect SSNs and other sensitive personal information.
- To access this marketplace, you must register, but before that, you must verify yourself as a human by passing a CAPTCHA test.
- Business operational data, such as operational data, financial data, intellectual property, and trade secrets can be found on the dark web.
- Hackers spend a lot of time on the dark web, and it’s not too difficult to get access to hacking tools and data leaks in this part of the internet.
- Unlike the regular internet, the dark web doesn’t use standard URLs or search engines.
- That means that only 0.024% of all the known pages are findable in Google’s search engine.
- Buyers can acquire personal information and financial details without revealing their identities, giving them the means to engage in criminal activities without being traced.
Accessing it requires special software, such as the Tor browser, which provides anonymity by routing your connection through multiple servers. Social media platforms and online communities play a critical role in reporting any suspicious activities related to hitmen or assassination services. Individuals should promptly notify law enforcement agencies, providing any available information to aid in their investigations. Government agencies, law enforcement bodies, and healthcare organizations are actively working to identify and dismantle the networks involved in organ trafficking on the Dark Web.
It’s the place where you can buy or sell stolen credit card numbers, SSH login credentials, and personally identifiable information (PII). The Dark Web provides a platform for sellers and buyers to engage in the trade of counterfeit goods with a level of anonymity and reduced risk of detection. These marketplaces offer a wide range of counterfeit items that are designed to resemble the genuine products as closely as possible.