Card Shops are a type of dark web marketplace that hosts the trade of credit cards and other stolen financial information. Many users value the protection that comes with keeping their identity hidden. This secure setup is useful for those who want to avoid government surveillance or keep their personal information safe from online threats. To prevent the users from DDoS attacks, it provides personal marketplace domains to high-volume buyers and sellers. Moreover, this shop provides detailed statistics about each user profile on the platform, giving users a better idea about the vendors for the buyers and vice versa. This marketplace accepts payments via Monero but also supports the Escrow system.
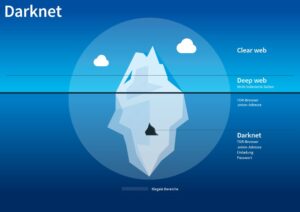
Individuals attempting to engage in these practices often do so for various reasons, but it is essential to understand the risks involved. The Dark Web operates as a shadow marketplace, with prices for stolen data influenced by the interplay of database security vulnerabilities, demand, and risk. From gift cards to full identity profiles and bank account access, each category reflects the nuanced economics of cybercrime. Understanding these dynamics is crucial for organizations to stay ahead of attackers, mitigate risks, and fortify their defenses against an ever-changing threat landscape. The dark web is a part of the internet that is not indexed by search engines and requires special software to access.
What Exactly Is Sold On These Marketplaces?
This can be a lucrative way to earn money, as miners are rewarded with a certain amount of cryptocurrency for each block they mine. However, it requires a significant investment in specialized hardware and a lot of electricity, so it may not be suitable for everyone. Aldon indicated that the other man with him, Shahal Lewis, of Stone Mountain, was his friend who came along for the money. Lewis was already on state probation, investigators say, and had a warrant out of Maryland. One of the clerks was too scared to say anything while the men were still in the store.
Monitoring Dark Web Activities
One of the primary features that sets the dark web apart is its emphasis on anonymity. Users on the dark web can conceal their identities by communicating through encrypted channels, making it difficult for their real-life information to be traced back to them. This anonymity provides protection for individuals who require privacy for legitimate reasons. Selling on the dark web can be a unique and profitable venture, but it requires careful consideration and adherence to ethical boundaries. By following the guidelines we’ve outlined here, you can navigate this hidden realm with confidence and potentially find success in your dark web selling endeavors.
The Best Dark Web Markets To Consider In 2025
The darknet can take care of this (and much more) by discretely delivering the legal compound to your door with no questions asked. S2T delivers cyber intelligence solutions based on real-world operational experience combined with deep technological expertise. Our AI driven Webint, Data Discovery and Fusion is a complete suite of products and solutions for your Cyber Intelligence needs, are at your fingertips. In most cases, the antivirus program that detected the threat should be sufficient to remove it. By following these steps and staying vigilant, you can better safeguard your security and privacy while engaging with the Dark Web.

Keep Your Data In The Dark — And Off The Dark Web
Still, even with these crackdowns and better defenses, dark web markets just keep coming back. As long as people want to buy and sell illegal stuff online, be it stolen data, narcotics, drugs, or malware, these markets will keep resurfacing, no matter how many times authorities take them down. The Dark Web is a collection of hidden websites accessible only through specialized software like Tor. Unlike the surface web, it is not indexed by traditional search engines and requires specific knowledge to navigate. This anonymity fosters a marketplace where both legal and illegal goods and services are exchanged.
Darknet or dark web marketplaces are a hidden part of the internet that surface web users can’t access; they can only be accessed with special anonymity software called Tor. Many people (mostly criminals) use these sites to perform illegal transactions such as selling banned goods and services. Comparitech researchers gathered listings for stolen credit cards, PayPal accounts, and other illicit goods and services on 13 dark web marketplaces. For legal reasons, we will not publicly disclose which marketplaces were used.
- The anonymity provided by the dark web enables buyers and sellers to conduct drug transactions without fear of being identified.
- The buyer, meanwhile, has to move out of the shadows to profit from their purchases.
- For shopping of last resort, you need money of last resort – bitcoin, or possibly monero.
- Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks.
- It might be no surprise after the number of illicit hackers that are on the Dark Web that you can also buy a new identity.
You’ve no doubt heard talk of the “dark web” as a hotbed of criminal activity — and it is. Researchers Daniel Moore and Thomas Rid of King’s College in London classified the contents of 2,723 live dark web sites over a five-week period in 2015 and found that 57% host illicit material. It is important for individuals and organizations to collaborate in sharing information about security threats and promoting good cybersecurity practices. Cryptocurrency enthusiasts and legitimate businesses are actively working to promote responsible usage and compliance with regulatory measures. Additionally, efforts are being made to educate individuals about the risks and benefits of cryptocurrencies, as well as measures to ensure they are used for legal and ethical purposes. Efforts to counter DDoS attacks and mitigate their impact involve deploying advanced network security measures, such as firewalls, traffic filtering, and load balancing.
What Are Stolen Credit Cards Used For?
Once you have installed Tor, you can access the dark web by typing in the .onion URL of the site you want to visit. When one goes down, two more emerge with new ideas, better technology, and greater difficulty to track. It’s an ever-evolving ecosystem—constantly shifting, reinventing itself, and adapting. Many cybercriminals operating on the dark web have been arrested by law enforcement agencies, proving that anonymity isn’t foolproof.
It has a bidding feature, with new batches of stolen data being frequently added. The Abacus Market links to the new dark web marketplace sections and took over much of the vacuum left by the AlphaBay takedown. Stick to cryptocurrency, avoid downloading anything, and don’t share any personal info. Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement.
However, there are plenty of honeypots amongst the images, trapping customers attempting to buy them. It might be no surprise after the number of illicit hackers that are on the Dark Web that you can also buy a new identity. Identity theft can be used a method to gain financial advantages, such as obtaining a better credit score, in order to gain financially or to cause disadvantages on others. It’s one of the most common services offered out there that makes a huge amount of money. They’re tightening security and carefully screening anyone who wants to join.
Legal Risks
This is another money-spinner for illegal investors to make a quick profit. The way illegal match-fixing works is that a “Fixer” has an athlete or team already lined up to lose a specific sporting match. This would be a game where bets are taken (either legally in Vegas or in underground sports betting organizations). As an “investor,” you give a certain amount of money, and the “fixer” guarantees a percentage back (sometimes as much as 50%). For those with loose morals, instead of going to to your local store to purchase a new flat-screen TV or the latest gadget in the market, you can hire someone to steal it for you.
After it relaunched in June 2022, BidenCash initiated a promotional campaign that included sharing a dump of 8 million lines of compromised data for sale, which included thousands of stolen credit cards. These markets host hundreds, or in some cases thousands, of people who sell drugs, commonly referred to as “vendors”. The dark web offers vital anonymity for vendors and buyers, who use cryptocurrencies such as Bitcoin to process transactions. Although the dark web still accounts for just a fraction of all illicit sales online, it appears poised for rapid growth, according to the report. The increased use of the dark web is also a boon to cyber extortionists, who feed off traffic to their data leak portals and work to build relationships with the mainstream media. It’s clear that criminal activity on the dark web continues to grow and thrive.

The prices of counterfeit bills vary depending on factors such as quality, denominations, and the seller’s reputation. While the dark web may appear to offer opportunities for quick financial gain by allowing users to buy money on the dark web, the risks far outweigh any perceived benefits. Legal troubles, financial loss, and potential dangers from cyber threats should serve as significant deterrents against engaging in such activities.
Therefore, you must know how to access dark web marketplaces safely (covered later in this article). Of course, not all activity on the dark web is criminal, but such marketplaces are where a lot of illegal trade and money laundering happens. By relying on encryption, pseudo-anonymous currencies, and network-level anonymity, they create a false sense of safety, drawing in both buyers and sellers. A dark web market is a hidden online platform where users can anonymously buy, sell, and trade illegal or sensitive items. Such markets are typically accessible through the Tor network, which anonymizes traffic by routing it through multiple relays and encrypting each layer. This encryption makes attribution and tracking more difficult for authorities and cybersecurity professionals.