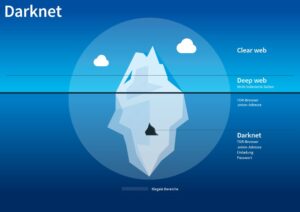
For example, when you sign in to your healthcare provider’s portal to view test results or request prescription refills, you’re accessing the deep web. That said, there’s more to this lawless digital frontier than its reputation as a hive of grotesque content and organized crime. Of course, that anonymity makes it harder to spot scams and confirm important information, and enables all manner of criminal activity, so it cuts both ways.
Use A VPN Or Proxy For An Extra Layer Of Security
Because of this, not many people are willing to give it a shot except if they have a very good reason. If you’re one of them, good luck finding a provider that supports it. Once you do, that provider will need to configure the entire thing on a specific server first. This server will route your Tor traffic and perform what you want.
Step 4: Configure Basic Settings
Browsers with the appropriate proxy can reach these sites, but others can’t. The Tor browser stands as the venerable luminary of darknet browsers, leveraging onion routing and encryption for unparalleled anonymity. Developed under the aegis of the non-profit Tor project, with sponsorship from the U.S. government and various organizations. While Tor Browser provides a degree of anonymity, accessing the dark web inherently involves exposure to a multitude of potential dangers. Users should be well aware of these risks before venturing into this part of the internet.
Tor Over VPN Vs VPN Over Tor — Which Is Safer?

As you might expect, Bitcoin is the top cryptocurrency being used on the Dark Web. Chainalysis says that $790 million worth of cryptocurrencies were used to shop in darknet markets during 2019. While some studies have claimed that illegal Bitcoin activity is as high as 44%. Tails is a mere 1.3 GB download, so on most connections it will download quickly. You can install it on any USB stick that has at least 8 GB of space.
Choose A Dark Web Search Engine
- While it’s generally safe to use, dark web activity can be detected at the entry and exit nodes of the Tor network.
- All you’ll need is an 8GB thumb drive, an installation package, and a couple of minutes to get things up and running.
- Its competitive pricing ensures that robust privacy protection is as affordable as a cup of coffee.
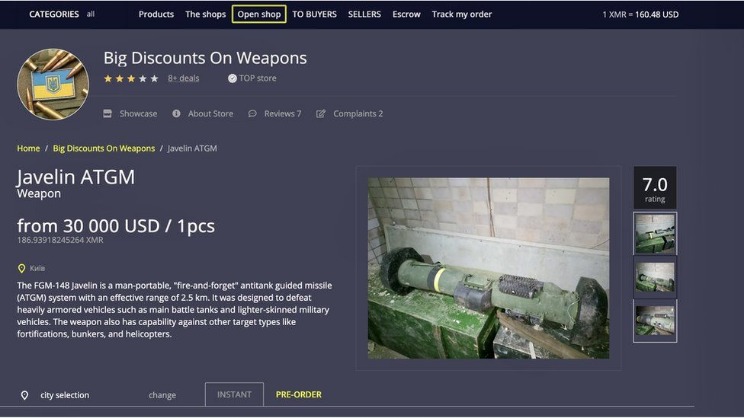
- Books, video games, apparel and rare collectibles are some of the legal items you can buy on dark web commerce sites.
Install Tor Browser from the official website, adjust security settings to “Safer” or “Safest,” and only use trusted onion links from verified directories. This blog offers a complete guide on how to access the Dark Web using the Tor Browser, along with step-by-step instructions, security tips, legal warnings, and real-world examples. Use encrypted communication platforms instead of the standard ones with less robust security features. For example, you can use Signal as your daily messaging app– it has end-to-end encryption and collects minimal data unlike many other messaging apps. Downloading tainted files or clicking suspicious links can install malware on your device, so be cautious when surfing the web. Tor doesn’t support external plugins and extensions, unlike standard browsers.
What Services And Tools Are Available On The Dark Web?
This addon allows you to control which sites can executive JavaScript and which ones can’t. Tor blocks JavaScript by default, but this addon lets you permit it for trusted sites. The tradeoff is that you don’t get personalized search results, as DuckDuckGo doesn’t collect user data. But this tradeoff is worthwhile when seeking to browse with the utmost privacy. To surf the web privately, you need to connect to the Tor network from your browser.
Pairing Tails And Tor
That’s the desktop edition, but there’s a version for Android and an unsupported onion browsing app for iOS. The dark web is infamous as a dangerous place, where drugs are bought and hitmen hired, but it can be a safe way to browse the internet if your privacy is serious concern. You should review access to your camera, location, and microphone regularly to ensure no website has unnecessary permissions. So, you should never share your personal information on the dark web. What’s more, they can also sell you personal information on the dark web as your personal data has a monetary value on the dark web. You should never trust websites and forums on the dark web with your personal information.
Secure Account Management And Communication

I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows. Because it’s easier to contain malware in a virtual environment, which can be fully controlled. It makes up about 6% of the internet, and it’s where you find everything from illegal marketplaces to forums for whistleblowers. The Dark Web is a hidden part of the internet, completely different from the clear web we all use daily.
For all intents and purposes, click Connect to get onto the Tor Network. It’ll take a few seconds, but in a moment the Tor browser will launch. Therefore, you should understand the legal risks of accessing the dark web before you venture into this murky world.
- This routing, through at least three nodes distributed worldwide, introduces latency, especially when there’s congestion on specific nodes.
- In fact, a recent judgment by the US Supreme Court denoted that simply using Tor was sufficient probable cause for law enforcement to search and seize any computer around the world.
- The entry node knows your IP address but not the intended destination.
- A VPN encrypts your web traffic to ensure it’s hidden from the big brother who could be watching you online.
Because dark web pages generally aren’t indexed, you can’t find them using traditional search engines, but some search engines like DuckDuckGo may help you navigate the dark web more easily. The Hidden Wiki is a directory hosted on the clear net (also called the “surface web”) that contains a list of .onion links for many of the best dark web websites. I2P is a private network built for secure, anonymous communication.
There is also a high risk of falling victim to scams or malware attacks on the dark web. Moreover, the dark web is a haven for cybercriminals who engage in fraudulent schemes and identity theft. It is a place where anonymity reigns supreme, offering both promise and peril to those who dare to venture into its shadowy depths. It shouldn’t surprise you that your web activity is being monitored and recorded by a vast array of parties from your ISP on down. Do not install the browser from any other location, as it may be infected with spyware or other nefarious programs.
Once connected to Tor, you’re ready to begin exploring the dark web. However, keep in mind that the dark web is not organized like the regular internet. Instead of search engines, you’ll need to rely on directories or specific .onion links.