Perhaps the best-known thing you can buy on the Dark Web is information collected in what seems like the almost daily data breaches we read about in the news. That information can include checking and credit card account numbers, social security numbers, and other sensitive information. Silk Road became one of the most famous online black markets on the dark web for illegally selling drugs. In a September interview with Wired, DeSnake wrote that he reappeared to re-establish AlphaBay’s popularity as the go-to online black market.
A Dark Web Search Engine
- While it’s a deep resource, it’s also illegal in many countries, because it may violate copyright restrictions, so check out the laws in your area before visiting.
- You can’t access these .onion sites from your normal web browser like the one you’re probably viewing this page on.
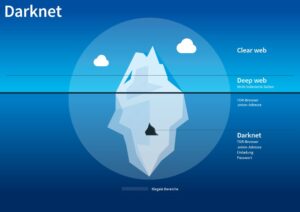
- The dark web contains content that’s only accessible through networks like Tor.
- Those risks were mitigated with cryptocurrencies, but we explore how even the new, supposedly anonymous cryptocurrency solution is not without risk or incredible insecurity, either.
- From there, these products are then passed on to distributors, which are the dark web marketplaces in this context.
Nielsen’s Law of Internet Bandwidth is an observation that states the average bandwidth speed will grow by 50% each year. Currency, as we mentioned earlier, became a digital thing, as did practically everything else. Music to Movies, financial and transaction information, software to corrupt it all. Everything could be uploaded and downloaded with expedience, and legal or not, everything began to find its way through the series of tubes. Have you ever wondered about what happens in the digital black market, or as better known the dark web?
Then get a VPN to help protect your privacy on dark web websites or wherever you browse online. You can use dark web monitoring tools, such as NordVPN’s Dark Web Monitor, to check if your data has been leaked. These tools scan dark web forums and marketplaces for any signs of your compromised credentials.

Is There A Future For Dark Web Marketplaces?
Rapid response can prevent unauthorized transactions, minimize financial losses, and protect your customers’ trust in your business. Whatever the risk involved, some users of the Internet felt that being told what they can and cannot possess, physical or digital, was akin to oppression. Telling someone they cannot do something is among the easiest ways to inspire them to do it.
White Hat Market’s Differentiator Was Security
To access the dark web, you’ll need a specific set of tools – more about that later in the step-by-step section. The surface web (often referred to as the “visible web”) is the portion of the web available to the general public and indexed in the standard web search engines such as Google, Bing, and Yahoo. Pixel Privacy believes in digital privacy and does not believe in using it for heinous and/or illegal activities, and so the focus of this article will be on legal activities.
The 9 Most Private Cryptocurrencies In 2025
However, if you’re considering browsing the dark web, be advised of the risks, including illegal content, malware, scams, and potential legal consequences. Silk Road operated via a hidden darknet feature in the anonymous Tor network. Accessed with an app, the Tor network allowed users to anonymously browse Silk Road without the threat of traffic monitoring. All transactions were conducted in cryptocurrency — namely Bitcoin — which further ensured anonymity. Tor project coined the term Onion Routing (TOR stands for The Onion Router) to describe the process by which users gain online privacy and anonymity using the network.
FBI Can Neither Confirm Nor Deny Investigations Into Darknet Markets That It Confirmed Are Ongoing
This means that the JavaScript will be disabled by default on every website and some symbols and images will not be displayed. Advocacy groups are also reaping the advantages of the darknet because, here, the term of censorship is as popular as HTTPS. And finally, we have political outcasts, refugees, and people who want to get in touch with the outside world, being from a totalitarian country that suppresses all means of communication and information.
What Is The Main Cryptocurrency Used On The Dark Web?

When both buyers and sellers are anonymous, the credibility of any ratings system is dubious. Ratings are easily manipulated, and even sellers with long track records have been known to suddenly disappear with their customers’ crypto-coins, only to set up shop later under a different alias. Dark web websites look pretty much like any other site, but there are important differences. Instead of ending in .com or .co, dark web websites end in .onion. That’s “a special-use top level domain suffix designating an anonymous hidden service reachable via the Tor network,” according to Wikipedia. Browsers with the appropriate proxy can reach these sites, but others can’t.
It makes up about 6% of the internet, and it’s where you find everything from illegal marketplaces to forums for whistleblowers. The deep web is just the part of the internet you can’t find with a search engine. It’s not mysterious or spooky; it’s home to everyday things like scientific research, medical records, private financial information, and secure communications. Even if you’re using a private, anonymized crypto wallet, there are other ways your identity can be revealed—even if it’s something as simple as letting a personal detail slip in an instant message.
Afterwards, your request will be matched with the appropriate website. Tricky, but effective; that’s why it’s, by far, the best method to access dark web content. A VPN hides your internet activity, making it harder for your connection requests to be traced back to you. It’s a precaution to protect yourself before diving into the dark web. For recommendations on choosing a VPN, look for expert reviews and articles.
These domain names are not registered with a central authority but are instead derived from cryptographic keys. Offering books for free, shadow libraries face the morality question of copyright vs. access to information and knowledge. Just Another Library is one such service, with a wealth of books covering computer programming, science, and niche hobbies (sailors’ knots, anyone?).
Should You Use A VPN And Tor?
Too-good-to-be-true investment offers are another classic scam on the dark web. Early participants may see some profit, but that money usually comes from new victims, not actual earnings. Eventually, the system collapses, and most people lose their entire investment. So, if a “business opportunity” sounds too perfect, it probably is. Once many users begin to rely on the site and store funds in escrow, the operators disappear, taking all the money with them and leaving their customers and clients with nothing. Some sellers offer cracked versions of expensive software that you’d typically pay hundreds of dollars for.
Common Scams And Fraudulent Activities On Darknet Markets
Today, Exodus Marketplace works from 3 different domains, two of which are its mirrors. KEY TAKEAWAYS Whether you are using Android or iPhone, you can easily access the dark web on your ph… KEY TAKEAWAYS The Deep and the Dark web are the hidden part of the internet. KEY TAKEAWAYS If you live in a country where you don’t have internet freedom and face extreme … Farwa is an experienced InfoSec writer and cybersecurity journalist skilled in writing articles related to cybersecurity, AI, DevOps, Big Data, Cloud security, VPNs, IAM, and Cloud Computing.
Some imitate Silk Road (there was even a “new” Silk Road market operating for a while), while others find ways to innovate. Worth approximately $1 billion at the time, it was later revealed that the US Government made these transfers in a civil forfeiture action. According to a press release, the Bitcoin wallet belonged to “Individual X” who had stolen the Bitcoin by hacking into Silk Road. When the Silk Road was in operation, you could search for the Silk Road link on Tor, then redirect to a signup screen requiring a username and password.
Riseup is a volunteer-run collective that offers secure chat and email services primarily used by progressive activists and social justice communities. It’s maintained by an independent organization committed to digital privacy and security. It runs an onion site to help like-minded people mobilize more securely and anonymously. Normally these markets employed less reliable exchange methods like physical trade, leaving cash at one drop point and retrieving the purchase elsewhere.