AllWorld . cards has been operating since at least June and already has more than 2.5 million stolen cards selling between at between thirty cents and $14.40 apiece, CPO says. Digital banking has transformed both consumer banking and the threats posed to banks and their customers. In addition to new scams and schemes targeting online banking customers, we have seen the evolution of criminal marketplaces to trade in stolen information, stolen accounts, and stolen money. This has been a particularly interesting history of development around stolen payment card information. Carders tend to target specific sites that don’t have VBV or other protections against fraud.
- His work has appeared in Time, Success, USA Today, Credit Karma, NerdWallet, Wirecutter and more.
- Additionally, biometric facial recognition technologies can be used to offer remote identity verification via face scans.
- It’s an ever-evolving ecosystem—constantly shifting, reinventing itself, and adapting.
- The site has a unique news section, where the admin updates the buyers about new leaks and dumps, the source of the dumps, structural site updates and more.
- Group-IB’s cybercrime research unit has detected two major leaks of cards relating to Indian banks in the past several months.
Keeping Your Data Safe
Like legitimate commodity markets, the black market on the internet is extremely competitive. Cybercriminals must market their commodities to other criminals to be profitable. They design promotions, displays, service warranties, and even discounts for large purchases, all of which are advertised on secret forums and occasionally on social media. In a world where everything has gone digital, keeping your business secure should be your number one priority.
This makes it crucial to monitor accounts closely and use strong security measures. Also, the researchers discovered that debit cards were more common than credit cards, which is particularly worrisome since debit cards don’t have the same level of protections as credit cards. Unlike a credit card, a debit card is connected directly to your checking account, allowing fraudsters to immediately drain your account. Even if you report the fraudulent activity quickly and limit your losses, you may still face the issue of bounced checks or being late on payments, Krebs says.
Customers
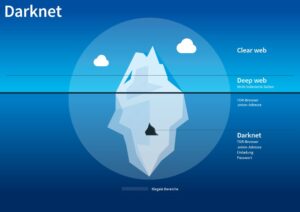
Back in the day, carding forums were the busiest of online crime hangouts, selling packs of stolen credit card data to anyone with the cash. That was then; now, you are more likely to find a roaring trade being made on the dark web in the likes of stolen passwords and account credentials, phishing exploit kits and malware-as-a-service platforms. A new report has revealed that the B1ack Stash crime forum has just given away more than a million stolen credit cards for free. Carding shops are a type of dark web marketplace that hosts the trade of credit cards and other stolen financial information. These platforms serve as hubs for cybercriminals to buy and sell compromised payment card details.
The 10 Biggest Dark Web Markets In 2025 – Updated List & Security Insights
These cards are then used by cybercriminals to make online purchases, including buying gift cards, that are hard to track back to them. Cybercriminals looking to buy stolen information usually prefer Brians club stolen credit cards. Exploring the realm of credit card transactions on the Dark Web is a journey into a dangerous and illegal world. While the allure of cheap credit card details and the potential for financial gain may be tempting, the risks and consequences of engaging in such activities cannot be ignored. The few public references to the website are on Reddit forums or specialty tech blogs.
How Stolen Credit Cards Are Sold On The Dark Web
So when WHM unexpectedly closed on October 1, it came as a shock to the platform’s dedicated user base. The Experian Smart Money™ Debit Card is issued by Community Federal Savings Bank (CFSB), pursuant to a license from Mastercard International. Not all personal information is valued the same on the dark web. Prices can vary based on demand, how complete the data is and how easily it can be monetized by criminals.
- As terrible as its reputation may be, some vendors sell legitimate goods or services.
- Hidden Tor Servers are now the norm for storing, accessing and hiding illicit activity such as child pornography.
- The exfiltration process can be stealthy, designed to avoid detection, or more blatant, particularly in ransomware attacks where the data is held hostage.
- The categories are well organized, ranging from drugs and fraud to digital products, guides, and malware.What really sets it apart is its focus on security and usability.
- Then, you can set up 2FA (two-factor authentication) for that extra touch of security in case someone somehow figures out your password.
Beacon Cybersecurity Newsletter

For police, who would prefer criminals to face justice, this kind of exit causes mixed feelings. In October 2021, White House Market – the largest darknet market of its kind – announced that it would shut down. This was followed by Cannazon in November and Torrez over Christmas. Matthew McKenzie is a seasoned writer with a passion for finance and technology. The players in this market come from all over the world, but most of the Web sites where they meet are run from computer servers in the former Soviet Union, making them difficult to police. They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails.
Monero and Bitcoin are two of the most commonly used digital currencies on the dark web markets. Due to being the most popular and the oldest coin, Bitcoin is traceable. However, Monero, on the other hand, is untraceable and the most trusted payment method on these markets. Therefore, most cybersecurity experts recommend using Monero while shopping on darknet markets. The anonymity and lack of rules that define darknet marketplaces are exactly what make them breeding grounds for fraudulent activities.
Most people start by using the Tor Browser, which hides your IP address. The second category consists of data stores, which specialize in stolen information. We’re back with another video in our Webz Insider video series on everything web data. In addition to a clearnet domain, they also shared the new URLs through various hacking and carding forums. Sponsored content is written and edited by members of our sponsor community.
How A PayPal Account Or Credit Card Ends Up On The Dark Web
The data posted on these online illicit shops is a goldmine for threat actors who are looking to commit financial crimes. It provides them with valuable information needed to carry out a variety of attacks. All of these features, its competitive pricing, along with the volume of credit card information listings, make Real and Rare one of the prime sites to trade credit card information online. It comes just under a year since the retirement of the previous market leader Joker’s Stash, which facilitated the sale of nearly $400 million in stolen cards. UniCC benefited from the gap in the market left by Joker’s Stash – quickly taking the lead with a 30% market share. What is surprising to many is the deep web is 90% of the entire web, which is full of unharmful and legal items – they’re just not indexed for search engines.
The Dark Web And Black Market For Stolen Credit Cards** (200-250 Words)
To expand their reach, some marketplaces established parallel channels on Telegram. This further complicates monitoring efforts because now you need to search for the related Telegram channels and track activity there and on the marketplace itself. The researcher’s revealed hackers have discovered a way to find card numbers without breaking into a database, and there’s also a booming underground black market for them.
The leak of 26+ million stolen card records disrupted the market by exposing buyers, sellers, and transactions. It allowed financial institutions to cancel cards and reduce fraud losses. Brians club login acted as a central hub for buying and selling stolen card data, providing tools like search filters, pricing tiers, and customer support to attract fraudsters. When engaging in any transaction, it is essential to take protective measures and precautions to safeguard personal information and privacy. This includes using a secure and anonymous internet connection, using a reputable VPN (Virtual Private Network), utilizing trusted marketplaces and vendors, and practicing good online security hygiene. Now that we understand why individuals are enticed to buy credit cards on the Dark Web, let us explore the risks and challenges involved in these transactions and how to navigate this treacherous landscape.
Identity Security Lessons: Comparing AI Agents With Humans

RussianMarket specializes in the sale of “logs”, CVVs, dumps and RDP access. MuckRock is a non-profit collaborative news site that gives you the tools to keep our government transparent and accountable. This is the new breed of dark net markets—one that will make the next big international takedown much harder to pull off. The site’s limited number of vendor registrations also created a level of exclusivity to the site. The trade-off was that their sales value never exceeded at most a fifth of AlphaBay’s peak. Engstrom, who faces a mandatory-minimum of 10 years in federal prison if convicted, later told pretrial services that he owned somewhere between $8 million and $10 million in cryptocurrency.
In some markets, like the US market, those interchange fee revenues can approach 3% of all transactions. Simultaneously, customers face the risks of identity theft, damaged credit scores, and the emotional toll of financial fraud. The sooner you become aware of compromised information, such as stolen credit card numbers on dark web, the faster you can take steps to mitigate damage. Rapid response can prevent unauthorized transactions, minimize financial losses, and protect your customers’ trust in your business. The Silk Road was a marketplace for illegal products such as drugs online.