Empire Market is a dark web shop that resembles the AlphaBay marketplace. Its look, design, options, and interface are exactly the exact copy of its competitor, but everything else, including buyers, vendors, and servers, is different. At its launch, the platform accepted payments through Litecoin, but now it has incorporated support for other payment methods like Monero and Bitcoin.
What Is WPA2 (Wireless Protected Access ?
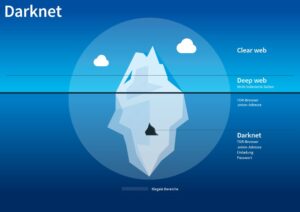
Near total anonymity and a complete lack of regulation can easily attract criminality, and onion sites can harbor malware such as ransomware or spyware. Onion sites are dark web sites that can only be reached through online routing via Tor, in which encrypted data passes through multiple nodes before reaching its destination. Decrypting the data involves peeling back layer upon layer of encryption, hence the “onion” analogy. ProtonMail is an email service that uses end-to-end encryption, making your email accessible to you and only you. The service retains no copies of any data that passes through a ProtonMail account. Although ProtonMail also exists on the clear web, accessing it via Tor provides an extra layer of privacy if you don’t want to leave a trace of you even using ProtonMail.
Install The Tor Browser

The dark web is designed in such a manner that it hides the identities and locations of its visitors. This extra privacy makes it much harder for authorities to track down who runs these markets and where they are located. For these reasons, most of these stores naturally like the dark web due to its protection. For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy.
Category #2: Details Needed For Physical Fraudulent Use
My dedication to continuous learning fuels my passion for delving into the complexities of the cyber world. ProPublica, a famous non-profit news organization that has been awarded the prestigious Pulitzer Prize, is committed to exposing power abuses and public trust issues through its investigative journalism. There’s a reason why this onion website is called the Imperial Library; with over downloadable 500,000 books and articles, this may be one of the largest digital libraries, period. It’s alleged that the strange noises and voices are actually coded messages, probably sent by secret operatives.
- We will address paying child pornography sites in the next volume.
- The place is as messy and chaotic as you would expect when everyone is anonymous, and a substantial minority are out to scam others.
- Prices for credit cards, for example, are falling because the market is flooded with records, and botnets and DDoS capabilities are cheaper because so many more options are available.
- But anything that’s against the law on the regular web or offline is also illegal on the dark web.
- WeTheNorth has a strong community vibe, with an active forum where users interact and share updates.
Keep Your Identity Hidden
You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here. These sites are a hybrid tutorial-underground where wannabe hackers ask questions and professionals sell their services or stolen data. Blockchain.info (now Blockchain.com) is a popular cryptocurrency wallet and blockchain explorer service (one of the first sites to launch on the dark web). It was initially created to provide additional security and eliminate cryptocurrency theft. It’s a wallet, explorer service, not a dark web marketplace itself, but still a helpful resource. ProtonMail is a Swiss-based email service that is very easy to use.
Video Tutorial: Set Up VPN To Access Darknet Markets Anonymously
It enhances buyer transparency by importing vendor feedback with PGP proof. Torzon offers a premium account option for additional benefits and is valued at approximately $15 million, accepting payments in Bitcoin (BTC) and Monero (XMR). In contrast, sites hosted on the dark web can only be accessed via onion routing with Tor, or another dark web browser. In countries including India and Nepal, the price of fuel is set by the government, and it is illegal to sell the fuel at a higher price. During the petrol crisis in Nepal, black marketing in fuel became common, especially during mass petrol shortage.

Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc.
ASAP Market (Best For Drug-Free Listings)

Using TAILS is yet another security measure that protects your online identity on the dark web. It is a specific Debian-based version of Linux software that leaves no traces of the user activity or the operating system on the computer. It uses the Tor network because it is a popular network that helps to circumvent censorship and online surveillance.
Best Free VPNs For The Dark Web In 2025: Secure & Fast
- These hackers don’t hide in the shadows as much as you might think.
- It contains 7,500 terabytes of information, compared with only 19 terabytes of information in the “surface” web.
- Users must look for platforms employing robust encryption protocols, secure escrow services, and advanced anti-phishing measures.
- PatrickStash has two categories, Cards and Cards NoVBV (short for Verified By Visa).
- They really don’t care about the loss and dilemma of the victims whose data has been stolen.
Such activities are generally referred to using the definite article, e.g., “the black market in bush meat”. Wizardshop.cc was established in 2022, and offers a wide range of leaked CVVs, database dumps and even RDPs. In the past 6 months, the site has increased the volume of cards sold, placing itself as one of the top sites selling credit cards today. The site has a unique news section, where the admin updates the buyers about new leaks and dumps, the source of the dumps, structural site updates and more. Since it was established in 2020, Real and Rare has been considered to be a stable credit card site that suffered very few downtimes. The number of card packages offered on the site has consistently increased, and today it also has an active Telegram channel from which it operates and sells stolen credit card details and announces new dumps.
The anonymous group behind Tunnels alleged that the materials were produced while exploring the forbidden tunnels, built underneath some of the most prestigious American Universities. No info is available on the explored institutions or how these sections can be accessed. I think it’s safe to say that these are unsanctioned exploits, all the more reason to boast them on the dark web. I have to admit to having a soft spot for Tunnels, an onion website about underground “urban” exploration.
Typical Use-Cases Of Dark-Web Marketplaces In 2025
However, note that the site only uses non-sensitive and public data for the metrics. The Tor Metrics is a good place to get more information about the Tor project. It collects data from the public Tor network and archives historical data of the Tor ecosystem. Awazon became the successor of the popular AlphaBay market, which the authorities shut down successfully in July 2023. Like any other site of such nature, Awazon Market isn’t free from risks, so be careful while accessing it. It is an excellent option if you want to surf the web anonymously.
Best Black Business Names

So, if a “business opportunity” sounds too perfect, it probably is. Imagine trusting a site where you’ve been buying or selling for months, and everything seems legit. Some marketplace operators first build trust by running a legitimate platform. They sell these files for just a fraction of the original cost on the surface web or even share freely, which makes them tempting for people looking for shortcuts. While it might be tempting, remember that downloading such content has serious legal and cybersecurity risks.
You can rely on this .onion site if The Hidden Wiki goes down temporarily or permanently. Email is one of the least secure communication systems; the email providers have access to the contents of your inbox. For evidence, look no further than the way Google automatically adds travel information, meetings, and other diary entries onto your calendar.