Avoid downloading files, clicking on unfamiliar links, and sharing personal information. Additionally, do not attempt to buy anything on the dark web as most transactions are illegal and can lead to scams. The Darknet is a subset of the Internet operating over encrypted, anonymous overlay networks that require special software like Tor, Freenet, or I2P. For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy.
The Hidden Wiki
Use cryptocurrency to buy anything, and use a disposable email address for any type of communication on the dark web. Check around with other users and ask if they know anything about the new marketplace. But remember, it’s essential to take all the necessary and important security steps before entering such sites on the dark web. As mentioned before, your ISP and government institutions are not able to see what sites you visit on the Tor network, but they can probably see that you use Tor. From this point onwards, you can enjoy complete anonymity and security while being able to access “.onion” websites and other dark web browser domains. When you install a VPN, all of your activities on the dark web will be hidden from unwanted snoops from your ISP or the FBI.
Unlike other search engines, it does not collect or share web activities and personal data of users. While people and organizations do host legitimate and useful sites on the dark web, it’s still best to tread cautiously. Despite Tor’s privacy-focused design, malicious entities are more likely to target your data in transit and on .onion sites. Using Tor to access dark web links isn’t illegal, but your ISP will notice, and others may too. It’s, ironically, more conspicuous than using popular browsers and sites.
How Do Hackers Access The DarkWeb?
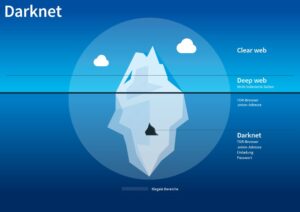
A study by researchers at King’s College London that examined the contents of over 2,700 darknet sites found that approximately 60% of them hosted illicit content. Because of its anonymity, the dark web is filled with illegal services and is used by numerous criminal groups, including ransomware gangs. It is also used by whistle-blowers, journalists, and other individuals who are not involved in illegal activity but need to protect their communications and identities. Through the dark web, users in places of high censorship can also access information and news.
Network Structure Of Transactions
Too-good-to-be-true investment offers are another classic scam on the dark web. Early participants may see some profit, but that money usually comes from new victims, not actual earnings. Eventually, the system collapses, and most people lose their entire investment.
First Deep Web Black Markets
You need to have a special browser like the Tor Browser to access it. It’s relatively easy for anyone to access this encrypted network. Swensen said the most common dark web networks are Tor, I2P, and Freenet, but “Tor is, by far and away, the most popular.” Dread is a Reddit-like forum on the dark web where users discuss cybersecurity, marketplaces, tools, and underground activities. The Tor browser is a privacy-focused web browser that allows users to browse the internet anonymously, including accessing .onion domains on the dark web. OSINT professionals use the dark web to gather intelligence from hidden forums, marketplaces, and databases that provide early indicators of cyber threats and leaks.
Dominant Markets
OSINT helps cybersecurity professionals gather publicly available intelligence—often from hard-to-access sources like the dark web—to predict, prevent, and respond to threats. Always prioritize ethical practices, and ensure that your dark web investigations are conducted with full legal compliance and operational security. Identifying specific individuals who use the dark web can be quite tricky. However, we advise connecting to one of our recommended VPN services to stay anonymous. One of the great things about Tor is that it can be used to access both the dark and surface web.
Easy Steps To Access Dark Web On Your Phone Safely In 2024
- Established in 2019, Versus quickly gained a reputation for a user-friendly UI and intuitive search options.
- KEY TAKEAWAYS The Deep and the Dark web are the hidden part of the internet.
- Other sites explicitly block search engines from identifying them.
- Malicious vendors often infect buyers with spyware, ransomware, or infostealer malware hidden in downloadable files.
As a result, you should avoid opening unfiltered sources, torrent sites, and dark web links unnecessarily and downloading every file you come across. While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity. That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy.
For obvious reasons—I don’t want to get you or me into trouble, after all—I’m not going to get too specific when it comes to what you can find for sale on the dark web. A lot of transactions are handled via cryptocurrencies such as Bitcoin, which is relatively (but not completely) private and anonymous. Another private cryptocurrency you’ll find being used is Monero, which prides itself on being untraceable. Bear in mind too, that your internet provider will be able to see you connecting to Tor nodes, even if it doesn’t know exactly what you’re doing. Many people install a VPN as well, but then you’re putting your trust in an additional third party to not track your activities or report them to anyone else.
The users of the dark web are typically aiming to block governments from snooping on them. This can often be for political reasons, but also because they may be involved in illegal activities, such as the ones listed above. Unlike the surface and deep web, you can’t access the dark web via a standard or specialized search engine.
It is easily accessible by the general public and requires no special configuration. You can find sites like Facebook, Wikipedia, e-commerce sites, YouTube, and more here. The anonymity provided by onion routing comes at the cost of slowing your internet considerably.
What Is The Darknet Market?

The Onion Router (Tor) also made the technology available in 2002. In addition, it has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails. Accidental leaks at the Tor entry nodes can potentially expose your IP address.
In the internet’s darkest corners, a myriad of hidden websites cater to an array of needs and interests. From encrypted communication channels and hacking forums to illicit marketplaces, the dark web is a destination for millions of daily users. Read on to learn more about the five main types of darknet websites and what they contain. People use dark markets when they want extra privacy and anonymity. Many users value the protection that comes with keeping their identity hidden. This secure setup is useful for those who want to avoid government surveillance or keep their personal information safe from online threats.