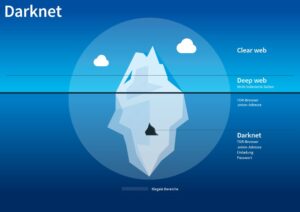
This is a free software tool that allows users to access the dark web and browse anonymously. The dark web is also a dynamic and ever-changing space, with new sites and services constantly emerging and others being taken down by law enforcement or other actors. Therefore, any estimate of its size is likely to be imprecise and quickly outdated. The black market refers to the trade of goods and services that operate outside of the official economy, governed by supply and demand laws.
Get Started
The conversion of dollars to Bitcoins was legal and relatively safe. Actually engaging in black market shopping, though, connects you to various kinds of illegal activities. We’ll continue our walkthrough but we are NOT endorsing these activities. This information can help security professionals understand how stolen identities and credit cards are used, how products are fenced or distributed illegally, and more. Therefore, if a person accesses the dark web with the intention of engaging in illegal activities or purchasing illegal goods and services, they could be committing a crime.
Types Of Dark Web Websites
The vendors aren’t required to register or apply for a vendor account while using this platform. It ensures the buyer’s identity is kept hidden and accepts payments through cryptocurrencies, including Bitcoin, Litecoin, Ethereum, and Monero. Another dark net marketplace that has grabbed a lot of attention is the Hydra market. The entire website is in Russian, but the vendors are present worldwide. It accepts payments through Bitcoin and the Escrow system and ensures that your identity remains anonymous during your purchases. It’s a user-only marketplace, meaning you need to register to enter.
Digital Black Markets
In some authoritarian states, accessing Tor nodes can flag you for surveillance. The Darknet is a subset of the Internet operating over encrypted, anonymous overlay networks that require special software like Tor, Freenet, or I2P. The dark web is known to host illegal and disturbing types of pornography, including child exploitation and violent content. After connecting to the Tor network, the Brave browser in the bottom left corner, “If your personal security depends on staying anonymous, use Tor Browser instead.” gives a warning. In the early 2000s, Tor was released to the public and became popular among users who wanted to protect their privacy online.
How To Access The Dark Web Safely

The impact of such breaches extends beyond financial loss, as it can erode trust and damage reputations. With Brandefense’s Dark Web Monitoring, businesses gain visibility into where and how their data is being exploited, allowing them to take immediate action to prevent further harm. Another danger lurking in the Dark Web is the proliferation of phishing scams. Fraudulent websites mimic legitimate ones, tricking users into sharing login credentials, financial details, or other sensitive information. These scams not only affect individuals but can also tarnish a company’s reputation. Brandefense’s Threat Intelligence platform proactively identifies phishing campaigns and provides real-time data to protect brands from exploitation, ensuring your online presence remains secure.
Minimize Or Rescale Your Tor Browsing Window
Additionally, Tor exit nodes are often blocked by websites that don’t trust them, and Tor over VPN can’t do anything about that, either. That information is hidden simply because most users won’t find it relevant. Much of it is tucked away in databases that Google is either uninterested in or barred from crawling. Even when using security measures and your common sense, accessing deep web content still poses a risk. Antivirus will ensure that any viruses or malware downloaded from the dark web are removed.
Dark Web Tools And Services
However, there are several “.onion” search engines like “onion.city”, “onion.to”, and “notevil” that you can use to find suitable marketplaces. NordVPN offers a 30-day, no-risk trial subscription when you sign up on this page. This provides a full month’s access to all of the features of the #1 VPN for the Dark Web.
Don’t Store Sensitive Information On The Same Device
It can only be used to access the content uploaded to the Freenet, which is a peer-to-peer distributed data store. Once you upload something, it stays there indefinitely even if you stop using Freenet, so long as it is popular. Tor over VPN requires you to place some trust in your VPN provider but not your ISP, and is best if you want to access .onion websites. VPN over Tor requires you to place trust in your ISP but not your VPN and is best if you want to avoid bad Tor exit nodes.
Understanding VPN Locations
The dark web is also a place for scammers to attract vulnerable and unwitting victims. The platform is also used by governmental cyber departments to identify and track potential criminals or offenders. You can never be sure who’s really behind the other end of the line.
You can use your real information—you aren’t doing anything illegal. In about three days you will be given a fraud test and have to identify small transfers in your Dwolla and personal bank account. Once your account is confirmed, wire any amount from your personal bank to Dwolla from a lump sum or the estimated price of your purchase you have in mind. After you confirm the transfers, your legit money will now be stored in a new global bank with less restriction than US banks.
In fact, a recent judgment by the US Supreme Court denoted that simply using Tor was sufficient probable cause for law enforcement to search and seize any computer around the world. Perhaps the best-known thing you can buy on the Dark Web is information collected in what seems like the almost daily data breaches we read about in the news. That information can include checking and credit card account numbers, social security numbers, and other sensitive information.
Methods To Access The Black Market: A Brief Look
At first glance, Tor doesn’t look that different from your regular browser – it has a search bar, lots of quick-launch icons, the peeled onion icon smack in the middle of the screen. All you’ll need is an 8GB thumb drive, an installation package, and a couple of minutes to get things up and running. I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows.
- A vast number of URLs have domain endings such as “.onion”, which means that the URLs are only accessible by Tor users.
- Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP.
- If you do need to access a dark web website for legitimate reasons, you can check directories like The Hidden Wiki to help find options.
- While visiting any of the sites you find on those Wiki sites, do not maximize your browser, as it can help identify you by your monitor resolution.
This hides your activity and personal identifiers so you can browse safely, protected from prying eyes and identity theft. Some dark web search engines are designed specifically for darknet browsing, while others also work on the clear web. All are fine as long as they can retrieve information from the non-indexed dark web and protect your privacy. Some popular search engines that can help you explore hidden content and anonymize your web traffic include DuckDuckGo and Ahmia.