Dark web search engines usually don’t track web activity or log your search history. But that doesn’t mean your dark web activity is completely anonymous. Before you start browsing websites on the dark web, make sure to protect yourself by using a VPN, proxy, or Tor. If you go premium, you’ll lose the ads and gain additional data insights and access to historical versions of websites. Haystak is one of the best dark web search engines on the Tor network. The platform offers uncensored and unfiltered web search results.
Some do, like Ahmia; others like Torch index nearly everything, including illicit content. The dark web is estimated to be significantly larger than the surface web, but much of it remains hidden or inaccessible. Use community-trusted directories, forums, and check reputation scores or comments on Reddit/darknet forums. If you’re not using Tor, a VPN, or proper anonymity tools, there is a risk of being tracked. Yes, DuckDuckGo has a .onion version that works through the Tor browser for anonymous searching. Unique in that it can be accessed via the clearnet (not just Tor).
The 9 Most Private Cryptocurrencies In 2025
RiseUp is a top dark web website that offers secure email services and a chat option. It was created in 1999 as a secure communication platform for people and groups working on liberatory social change. The platform is protected from government interference and malicious attacks to protect the user.
What Is Candle Search Engine?
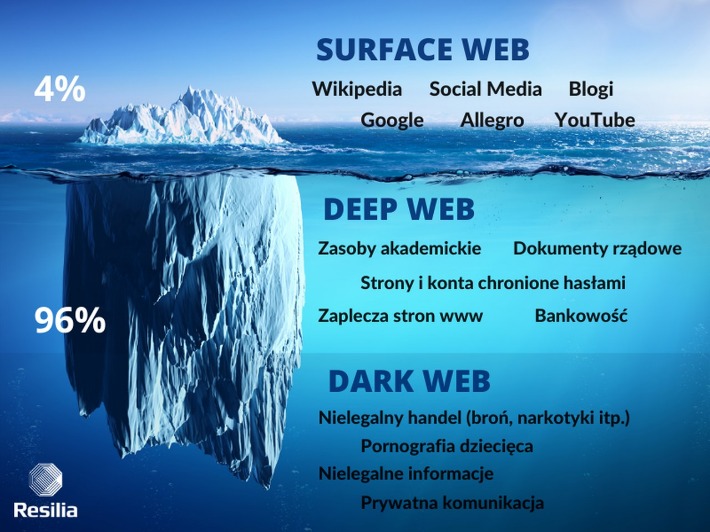
With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential. It is a good way to prevent third parties from tracking online activities. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web. It relies on P2P connections and requires specialized tools and software. Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity.

What Is The Surface Web?
Vendors often build up reputations through ratings and reviews, just like sellers on mainstream platforms. To reduce scams, many markets also use escrow systems, where the site holds the buyer’s payment until they confirm the item has been delivered. Dark web markets work much like regular e-commerce websites but with extra layers of anonymity and encryption. Buyers browse listings, place orders, and pay with cryptocurrency — typically Bitcoin or Monero — to obscure transaction trails.
Implications For Security Leaders
Once you are certain that you have the correct URL, save it in an encrypted note—the Tor browser will not cache it for later. Otherwise, there’s a good chance of falling victim to a phishing scam like this fake Bitcoin mixer. The easiest way to access Tor is through a special browser known as the Tor Browser. You might want to hide your Tor Browser download using a VPN and your existing browser’s private/incognito mode. Our rigorous research and testing have revealed revealing truths and busted myths.
There’s nothing stopping sellers from packing up and leaving the market at any time. They could get a batch of bad products, get arrested before they can ship your order, or any other number of things. There’s no guarantee that placing an order with any DNM vendor will be safe or shipped.
Roundup – Best VPNs For The Dark Web
- To stop the marketplaces is not a walk in the park as it takes immense effort from authorities like the FBI and international law enforcement.
- For 2025, they’re hyping a peer-to-peer escrow twist—could cut out middlemen and shake up how deals flow, which I’m stoked to see play out.
- If you’re into a darknet market with a community pulse and solid uptime, Bohemia Dark Market’s climbing the ranks—give it a spin if you like a vibe that’s less corporate, more crew.
- Your real information could be exposed at these nodes, allowing third parties to intercept your dark web activity.
- LeakLooker indexes live and historical data leaks found on underground forums, often used to identify early data breach activity.
- This service not only masks your IP address but also encrypts your data, adding an extra layer of security.
This means your activities cannot be traced or your browser history exposed. Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities. Onion links have no regular domain names registered under the domain name registry.
Explicit Content
- All your device’s internet traffic first goes to the VPN server, then bounces through the Tor Network before ending up at its final destination.
- And the search box can’t read certain characters like parentheses or quotation marks, which can be limiting.
- Radar Rundown Ad blockers are the best protection against disruptive ads.
- Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web.
- The dark web is a hidden collective of sites that you can only access through special browsers, most commonly Tor Browser.
You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity.
You can also take a look at the blogs & essays section if you want to find some nifty coding resources. Well, now it’s time to fire up Tails and do a little bit of tinkering. Chill, because nobody will ever find a record of you ever fiddling around the darknet. Note that Tails’ installation package is the .img format, which means that you’ll need software capable of burning images on your thumb drive. All you’ll need is an 8GB thumb drive, an installation package, and a couple of minutes to get things up and running.
After all, it’s much less popular, can’t be used to access normal websites, and isn’t as easy to use, among other disadvantages. Both rely on a peer-to-peer routing structure and layered encryption to make browsing private and anonymous. Tor over VPN also doesn’t protect users from malicious Tor exit nodes. Because Tor nodes are made up of volunteers, not all of them play by the rules. The final relay before your traffic goes to the destination website is known as the exit node.
For example, you can find information unavailable to the public and share data privately while protecting your online identity. Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies. These markets sell a range of illegal goods and services, including drugs, weapons, stolen data, and counterfeit items, and they typically require special software like Tor for access. The darknet, also known as the dark web, is a concealed section of the internet that’s inaccessible via standard search engines.

Keybase is an exciting identity service that aims to make it easy for you to link the presence of your online identities together in a cryptographic way. You can upload your PGP key or have the site create one for you, and use it to cryptographically link your Twitter profile, Github account, or Bitcoin address together. Based in Switzerland, ProtonMail is an encrypted email service that is very popular with cryptocurrency enthusiasts. The process costs a fee, but unlike other “tumbler” or “mixing” services, there is no risk that Wasabi or any of its users could scam you out of your coins.
Keep in mind that many criminal organizations use the dark web to communicate or sell merchandise. You may very well end up in the middle of a stakeout that could turn ugly. So, if the website looks fishy, close the tab, and forget about it. Fortunately, in Hidden Wiki, every website is followed by a brief description so that the user knows what to expect.