The integration of cryptocurrencies like Bitcoin and Monero continues to provide unparalleled anonymity, making these markets a preferred choice for buyers and sellers alike. In 2025, the landscape of darknet markets has evolved significantly, offering users a streamlined and secure environment for drug trade. The integration of advanced encryption technologies and user-friendly interfaces has made these platforms more accessible and efficient than ever before.
Security And Anonymity Features
The dark web market hosts a variety of cybercriminal groups, ranging from state-sponsored actors to independent ransomware gangs. These groups operate globally, leveraging sophisticated tools and networks to execute large-scale attacks and maintain anonymity. Having JavaScript enabled on the dark web can cause havoc because it can reveal your IP address to your website.
WhatsApp 0-Day Vulnerability Exploited To Hack Mac And IOS Users
Dark-web marketplaces attract sophisticated cybercriminals adept at launching phishing scams, malware attacks, or ransomware threats. Buyers and sellers frequently face risks from malicious actors posing as legitimate vendors or customers, potentially leading to financial loss or exposure of sensitive personal information. Experienced users typically prefer marketplaces with robust vendor rating systems, detailed feedback options, and transparent dispute resolution processes.
Detailed Analysis Of Darkweb Market Activity
The best darknet markets have evolved to prioritize user safety, transaction efficiency, and product quality. These platforms rely on advanced encryption and decentralized systems to ensure anonymity and reliability for both buyers and sellers. The darknet has become a cornerstone for secure and reliable drug trade, offering users unparalleled privacy and efficiency.
As these platforms continue to innovate, they are likely to remain the cornerstone of the global drug trade, offering a safe and efficient alternative to traditional methods. One of the key features of these markets is their use of Tor networks, which anonymize user activity by routing traffic through multiple nodes. This ensures that transactions remain untraceable, providing a layer of security unmatched by traditional online platforms. Additionally, many markets now integrate PGP encryption for communication, further safeguarding sensitive information.
Shifts In User Behavior And Marketplace Structures

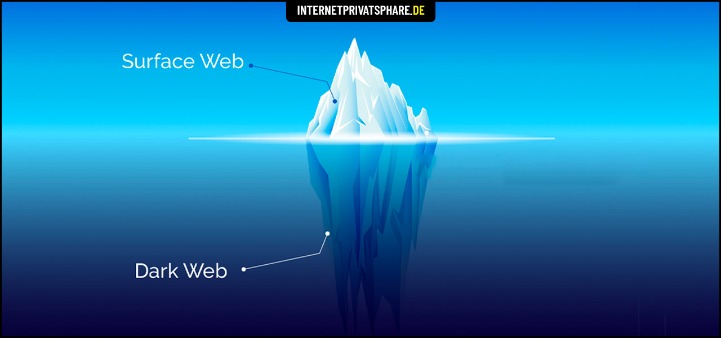
N 2025, dark web websites frequently change domains and are often short-lived. Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks. Apart from the dark web markets that are operating online today, some raided platforms influenced many markets.
In 2025, the dark web no longer exists in isolation—it interacts with mainstream platforms, influences real-world crime, and exploits cutting-edge financial systems. The ability to understand and counteract its growth will define the future of cybersecurity and digital law enforcement. However, you can trace its roots to the development of technologies like the Tor network or Freenet. In March 2000, an Irish grad student named Ian Clarke created the software application, Freenet.
State-sponsored Threat Actors
I grabbed mine from the official site a while back after dodging a sketchy mirror that tried to sneak in some junk software. In many countries, strict laws limit who can legally buy, own, or carry firearms. This is an estimated reading time to let you know how long it will take you to read all the content on this particular PrivacySavvy.com page. However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired. They use pseudonymous wallets, privacy coins (like Monero), mixers, chain-hopping, and non-KYC platforms to obscure transaction trails.
What Kind Of Content Is On The Dark Web?
Unlike Chrome, Bing, or Firefox, people can’t access the dark web without certain software or configurations. For example, they might need to log in via Freenet or the Tor browser, which uses onion routing to encrypt data via several different nodes. The evolution from IRC to Telegram represents more than just a shift in tools, it signals a transformation in how cybercrime infiltrates daily digital life. Criminals no longer retreat to hidden enclaves; they co-opt mainstream platforms. This trend will likely accelerate, with future coordination tools mirroring the usability of legitimate apps like Slack or Discord, but weaponised for fraud, ransomware, and data theft.
- For 2025, they’re teasing a peer-to-peer escrow setup—could be a game-changer.
- It has a huge and active user base as well as a marketplace that makes trading of hacked credentials and stolen data seamless.
- When you try to connect to a .onion website, Tor will route your traffic through three or more randomly chosen nodes before it reaches your destination website.
- Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums.
- However, if we’re being honest, the majority of activity on darknet markets involves illegal or heavily regulated items.
- A VPN hides the fact that you’re using Tor, which is blocked in some countries and always raises doubts because of its criminal reputation.
Why Cybercriminals Use Dark Web Forums And Deep Web Communities

To make its journalism more accessible to readers around the world, the New York Times launched its onion service in 2017. You won’t find any “hidden” stories here—it’s the same content as the normal web edition—but users in countries with government censorship will appreciate having a secure way to access it. Founded by security researcher Juha Nurmi, Ahmia is essentially a list of “hidden” sites that do want to be found. Onion sites are “crawled” and added to the list provided their “robots.txt” file permits it, and if it is not on their blacklist of sites with abuse material. Darknet markets, also known as “cryptomarkets,” are online marketplaces where users can buy and sell illegal goods and services using cryptocurrencies such as Bitcoin.
Tor Browser: Accessing The Darknet
The first step for any organization that wants a successful dark web forum monitoring is to start by establishing the goals, the areas to monitor, and the rules of engagement. Moreover, it’s essential to provide the company staff with enough training as well as defined objectives of what they should look for to bolster the monitoring efforts. Nevertheless, a lot of things happen in the dark web social hubs; it’s shady and illicit business most of the time, but interestingly, very active. It’s a platform for both beginners and elite hackers where they share knowledge on a wide range of topics like carding and advanced hacking techniques. Perhaps that’s their option for generating consistent traffic and a steady influx of new members.
Telegram & Session-Based Markets
Some markets are invite-only or have strict registration rules to keep out scammers and law enforcement. In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily. The landscape of darkweb markets is dynamic, influenced by technological, economic, and regulatory factors. As we move through 2024 and into 2025, these markets are expected to grow in both complexity and scope. Stakeholders, from law enforcement to market operators, will need to continuously adapt to the evolving environment. You could try to visit a major site like Facebook’s onion site to check if your browser is working at all.