Essential precautions include using updated security software, avoiding downloading suspicious files, and never revealing personal information. Common mistakes to avoid while accessing darknet links include using regular browsers, clicking random links, and failing to verify site authenticity. By following proper security protocols and staying informed about potential risks, users can more safely explore the darknet while protecting their privacy and security.
How To Access Dark Net?
Many phishing sites imitate trusted platforms like the Hidden Wiki to trick users. These clones often use nearly identical URLs to lure visitors into scams or malware traps. It deliberately avoids any tracking or logging of user activity, providing a minimalistic interface that loads quickly over Tor.
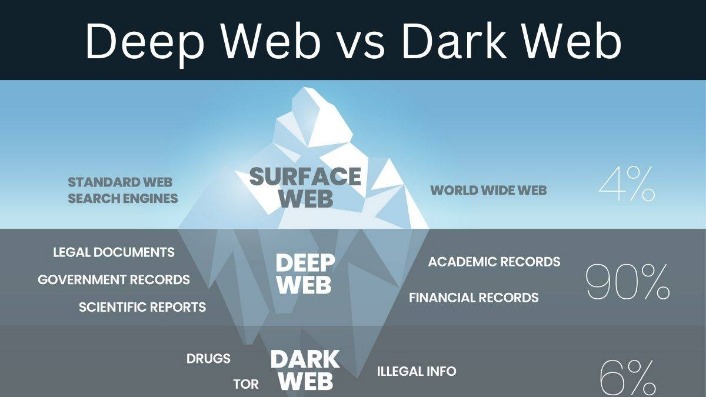
Its emphasis on privacy extends to encrypted messaging and multisig escrow systems, fostering safer transactions. The dark web is highly dynamic; sites frequently change addresses, disappear, or become scams. This ongoing maintenance ensures users can safely and confidently navigate the dark web with the help of the Hidden Wiki. The Hidden Wiki is one of the most well-known directories on the dark web, serving as a gateway for users looking to explore .onion sites securely and anonymously. For many, it’s the first stop when venturing into the depths of the dark web. The dark web is a hidden division of the internet that can only be accessed by those with special tools and is concealed below regular browsing.
Discover The Best Onion Links For Safe Browsing
That’s why knowing which dark web websites are safe to visit is vital. But anything that’s against the law on the regular web or offline is also illegal on the dark web. This includes buying or selling illicit goods, illegal transactions, and downloading copyrighted material. ProPublica is a non-profit, Pulitzer Prize-winning news outlet that focuses on abuses of power and issues of public trust. ProPublica’s investigative journalism can upset powerful interests, so the outlet joined the dark web to help their journalists and readers access their content anonymously.
How To Safely Access The Deep Web Using Tor
It’s a popular choice for users worried about online surveillance and data collection. Wherever you go online, but especially if you’re on dark web websites, using a VPN helps you secure your communication data and protect personal information you send or receive. Avast SecureLine VPN encrypts all of your internet traffic to help block hackers and keep snoops out. Install Avast SecureLine VPN today to browse safely and securely, wherever your online travels take you.

Why Tor Beats VPNs And Other Tools
Torch is one of the oldest dark web search engines, having served the darknet community for years. It boasts a vast archive of over 400,000 pages, providing comprehensive coverage of .onion sites, including forums, blogs, and marketplaces. The dark web is a part of the internet that isn’t accessible with regular browsers or search engines like Google and Bing.

Alt Address
Tor Metrics is a dark web site that keeps track of who’s using the Tor network and where they’re accessing it. It’s an interesting resource that translates Tor internet traffic levels into easy-to-digest stats. Riseup is available on the surface web, but its presence on the Tor network extends its privacy benefits by letting you use its services without exposing their real-world identities. You can access encrypted email services through the onion site without getting tracked.
What Are Onion Sites?
Always double-check the spelling of a link and compare it against a trusted directory or the official announcement thread (if available on Dread or Reddit). Avoid clicking links posted on surface web comment sections or unverified forums. And never bookmark .onion links unless you’re sure they come from a trusted, PGP-signed source. Visit us to discover more and become a part of our growing community dedicated to exploring the depths of the internet. Ahmia is one of the search engines intended to get into the Tor browser. It filters out dangerous sites and has been instrumental in raising awareness about sites that attempt to trick users.
- Meanwhile, transactions are secured to addresses that are randomly created alphanumeric cords.
- For safer browsing, it is highly recommended to also use a VPN and antivirus software.
- It organizes links into sections like forums, blogs, marketplaces, and privacy tools.
- Use strong, unique passwords and enable two-factor authentication where possible.
Using a reliable VPN like ExpressVPN with dark web search engines is essential for protecting your privacy. It hides your IP address, encrypts your internet traffic, and prevents your activity from being traced. A VPN also masks your online behavior from ISPs, which could flag you as suspicious for accessing the dark web. This added layer of security keeps your identity hidden and shields you from online threats. Since regular search engines don’t index .onion sites, finding what you need on the dark web can be tricky.

Lastly, to stay up-to-date with the happenings on a particular dark web website, forums are set up as a hub for information exchange. It can’t provide solutions should users encounter issues while using the website. The developers of ProtonMail recommend using the Tor browser to visit the dark web version of the service.
Hidden Wiki, although comprehensive, contains some very disturbing and very illegal info. While you don’t need to log in to access any of the dark web links listed here, you can’t find them with a search engine like Google. The only way to access the dark web is by using the correct browser and knowing the URLs of the pages you want to visit. Scroll on to learn more about dark web links (also called Tor links or onion sites), get the right links for some of the best Tor sites, and find out how to visit them safely. Additionally, one should be wary of counterfeit Hidden Wiki pages that exist online.
Final Thoughts: Actionable Steps For Safely Accessing Darknet Links
It goes without saying that I do not advise you to seek this sort of service. Try ZeroBin, a covert, dark web-based, communication platform that allows you to send media and text messages to your confederate. ZeroBin has a cool autodestruct feature that makes the message go kaboom (not literally) after the recipient reads it. Radar Rundown Free firewall software allow privacy ethusuiasts to secure their network and block mal…
How To Use Tor, And Is It Safe To Access The Dark Web?
Blockchain uses a shared and unchallengeable record that authorized members can only retrieve. The network members rheostat what info each member may grasp and what actions they can take. Nodes store and propagate the network payments’ state efficiently, going straight from one person to another. BTC is the first and most extensively known digital cryptocurrency created in 2009 by an unknown person using the codename Satoshi Nakamoto.