
The goal was to make Tor available for public domain use eventually. The logic was that messages couldn’t be hidden if nothing was available for them to hide behind. Another advantage of Tor and the dark web was to assist political dissidents in countries where they were suppressed by their governments and denied free speech. It is a way of allowing them to communicate and voice their opinions without fear of being monitored, trailed and punished. While the idea certainly sounds noble, criminals worldwide were quick to recognize and take advantage of the anonymity it offers. The deep web is more extensive than the surface web familiar to most web surfers.
Misconception 5: “The Deep Web Is Only For Cybercriminals And Hackers”
Other content on the Deep Web include private files like medical records, legal documents, and sites that have blocked search engine crawlers. Because the Deep Web contains valuable information like login credentials and personal data, fraudsters will target these sites to steal and sell data on the Dark Web. The deep web refers to all parts of the internet that are not indexed by search engines like Google or Bing. Unlike public web pages that anyone can find with a simple search, deep web content is hidden behind login forms, encryption, or restricted access. It includes everything from private databases and academic research to your personal email inbox or corporate intranet.
Conclusion: Navigating The Digital Landscape Safely
On the other hand, the dark web welcomes more distinct groups of users, like criminals, whistleblowers, or political dissidents, who leverage off the anonymity the dark web provides. With that said, any regular internet user can visit the dark web, which is not illegal to use. The dark web hosts all kinds of illegal activities, many of which are the buying and selling of firearms, drugs, counterfeit money, fake passports, and stolen accounts. Tor and other onion routers like I2P, Freenet and Subgraph OS aren’t the only way to mask your identity online, but they are the most comprehensive. Internet users familiar with encryption and cybersecurity likely know about VPNs, which can also mask your IP, but only to a certain point.
Internet And Search Engines

The deep web contains hidden content, such as private databases, government websites, and intranets. These parts of the internet require users to log in to access the data, and they consist of cloud servers that are protected with encryption and unlisted by search engines. Just below the surface web is the deep web, which includes private databases, web pages not indexed by search engines, password protected accounts, and more.
Security teams often focus on dark web monitoring while overlooking equally critical deep web sources like GitHub or Telegram. However, threats can often originate in the deep web before escalating to the dark web. Falling for these scams can result in financial loss, identity theft, and even physical harm. Engaging with fake hitman services may expose individuals to dangerous criminals, while falling for phishing scams can lead to identity theft and financial ruin. Sooner or later, some of your data will spill over to collections available for sale on the dark web. What you can do to protect yourself is to make sure that data is not accurate anymore, not detailed enough to cause harm, and that you have multi-factor authentication enabled everywhere you can use it.
It’s a critical component of the internet’s infrastructure, distinct from the often-overhyped realm of the Dark Web, which occupies just a small corner of this far larger digital expanse. Moreover, the deep web is not completely hidden and is a part of WWW (World Wide Web), whereas the dark web is completely hidden and cannot be accessed by any normal search engines. Have you ever wondered how come a result pops up on your screen when you type something on a search bar?
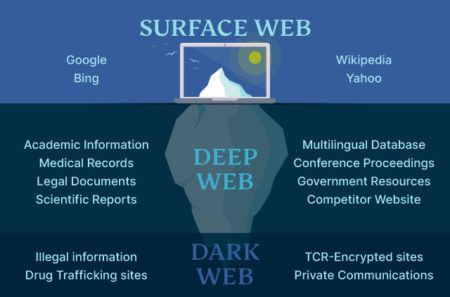
The dark web refers to any number of self-contained, encrypted overlay networks that live on top of the internet, inaccessible save for special tools and protocols, hence dark. The deep web is defined as the internet section that is not indexed by web crawlers. The dark web, on the other hand, is defined as a subsegment of the deep web that can be accessed only with special tools.
Difference Between Deep Web And Dark Web

Shadow web is nearly guaranteed to be an urban legend about a net deeper than the darknet that contains even more illegal stuff. The easiest way to access the dark web is to download a Tor browser and then access the Tor Network. The deep web is part of your everyday web and thus has to comply with all sorts of security standards and be hosted by companies that have at least some interest in maintaining their users’ privacy. Due to the fluid and unofficial nature of the dark web, nobody knows how big it is. To understand the deep web and dark web, you also need to understand the open web.
Deep Vs Dark Web: 17 Critical Differences
Attackers also used a ransomware-as-a-service (RaaS) kit supplied by the DarkSide collective via dark web marketplaces. The 2021 Colonial Pipeline ransomware attack shut down a critical energy pipeline on the Eastern Seaboard, leading to a $4.4 million ransom payment. Attackers used stolen employee credentials to access an unused Virtual Private Network account that remained accessible and active. Although a vast database was available for sale, the company stated that it had found no evidence of data breaches. This highlights the need for proactive monitoring that anticipates breaches, not waiting for the symptoms of cyber attacks. These operational, legal, and ethical issues make clear policies about accessing the dark web are critically important.
Just because a page cannot be accessed by search engines doesn’t mean it’s trying to promote illicit activity. Similarly, logging on to the Tor browser in order to browse the dark web doesn’t mean you’re breaking any laws. The dark web’s anonymity makes it a safe space for whistleblowers, which also makes it a valuable source of information for the government. Additionally, the technology for onion routing was actually developed by the U.S. Naval Research Laboratory to provide levels of protection for classified government communication online.
Can Search Engines Like Google Access The Deep Web Or Dark Web?

Be careful what data permissions you give (don’t just mindlessly click ‘yes’ on every pop-up just to get to a website). Still, according to investigations by the world’s best cybersecurity researchers and hackers, this shadow web is just a rumor. As you can notice if you read the list, many of the things for sale on the dark web are shams, designed to get your bitcoins without making good on the promise. Of course, if someone is actually looking to buy access to such things, they don’t earn a lot of sympathy as victims of the scam.
- Both the deep web and dark web come with their risks, however, the dark web presents a greater one.
- The chances of you stumbling onto an illegal page by mistake on the deep web are much higher than on a dark web.
- On the other hand, the dark web is a small subset of the deep web that uses encryption to stay hidden from the surface web.
- Let’s have a look at how the web is structured, so you can understand the differences between the deep web and the dark web.
- Cybercriminals take advantage of the privacy and anonymity that the Dark Web provides for a variety of purposes.
This version of the web is used by most of the world’s population for shopping, banking, entertainment and receiving the latest news. It is also heavily monitored by the world’s intelligence agencies and law enforcement on behalf of their governments. For instance, your Gmail inbox and your Google Drive are part of the deep web because they don’t exist as publicly accessible domains. Other examples include your bank account page and the settings page of your social media account, the admin page of your blog, and some academic journals. These websites exist in directories that Google (and other search engines) are barred from crawling. Darknets and Dark Web sites are encrypted, peer-to-peer networks that are only accessible via certain tools.
Cyber criminals phish users and exploit vulnerabilities in websites, databases, networks, and web apps to gain access to confidential data, such as user credentials. This information is then often traded or sold on underground online platforms, commonly known as the dark web. The deep web refers to all internet content not indexed by standard search engines like Google or Bing. Basic online hygiene can prevent security lapses when accessing the deep web.
Free Internet Provider Outernet Launching Its Own Satellites
Domain addresses on the dark web typically use non-standard top-level domains like “.onion” instead of common extensions like “.com” or “.org,” making them inaccessible through conventional browsers. Understanding the relationship between Tor and the dark web is essential—Tor (The Onion Router) is the primary software used to access these hidden sites. As a deep web subsection, the dark web shares many characteristics. However, noteworthy differences exist in operation, scope, size, access methodology, applications, and security.
The deep web and the dark web are often confused, but they serve different purposes and have different levels of accessibility. If you go browsing the deep or dark web, you may find plenty of advertisements which claim to offer up the gateway to this hidden corner of the web, in exchange for bitcoins. It’s a well-known scam, so be careful what you click if you go looking for it.



