
For instance, services like ProtonMail and SecureDrop (mentioned above already) have hidden sites for their users who live in countries with high levels of censorship. With the onion browser, you can access ordinary HTTPS websites on the web. This is a great way to improve your privacy because Tor isolates each website you visit, meaning third-party trackers and ISPs can’t reveal your identity. It works by sending internet traffic through volunteer-operated nodes all over the world. This network of over 6,000 relays hides your location, thus protecting you from online surveillance and third-party tracking by your websites.
TOR (The Onion Router) Network
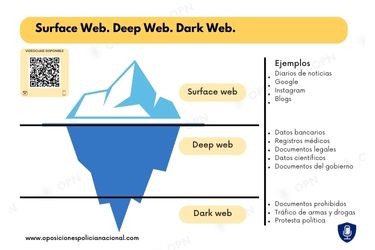
Differentiating between the deep web and dark web allows you to better understand the challenges involved in preventing hacking attempts and complications arising from the need for data privacy online. Unlike the Deep Web, Darknets are intentionally hidden and designed to preserve privacy and anonymity. Even platforms like Netflix, which require paid access, are technically part of the Deep Web.
What Should I Do If My Social Security Number Is On The Dark Web?
Knowing about various types of ransomware and common hacks can help you better prepare to spot cybersecurity threats on the dark web. You can use these dark web investigation tools to check if your company’s data is available on the dark web. The dark web also offers access to blocked resources in countries with strict government censorship on the internet. Citizens of such countries can use the dark web to bypass firewalls and access global information.
Is The Deep Web Illegal?
No, the dark web isn’t illegal, but what you do while in the underbelly of the internet matters. A lot of illegal activity takes place on the dark web, and engaging in any of that activity can be a criminal offense. The dark web is part of the hidden web, which comprises non-indexed websites that are mostly used for illegal and illicit activity. If you have heard your peers or colleagues throw this term around and are wondering, “What is the dark web?
Dark Web Tools And Services
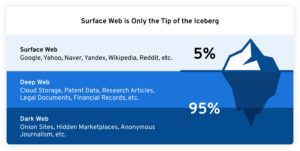
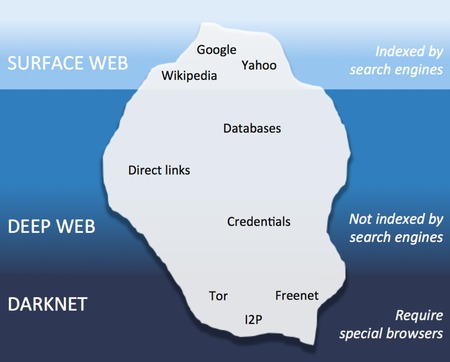
The tip of the iceberg floating above the surface is the portion of the internet we can access through normal means — i.e. browsers and search engines. Tor and other onion routers like I2P, Freenet and Subgraph OS aren’t the only way to mask your identity online, but they are the most comprehensive. Internet users familiar with encryption and cybersecurity likely know about VPNs, which can also mask your IP, but only to a certain point.
Protect Your Personal Information While Browsing
Surfing the dark web could cause you to access dangerous websites or illegal content. The deep web can also be termed an “Incognito Mode” of the web which cannot be accessed by search engines. If your work or lifestyle requires you to use the dark web, however, there are ways to protect yourself. Just as you need the right tools to access the dark web, you also need the right protections to be able to stay safe on it.
What Are EWallets And How Safe Are They?
Let’s explore their differences and the security implications of each layer. Would you be able to tell if a cybercriminal changed one character to send you to a malware-infested copycat site? There are a lot of misconceptions about it, but we’ll answer that question once and for all in this guide. We’ll also discuss why it’s dangerous and why you should inform yourself about the dark web even if you don’t plan to be on it.
For example, you can find information unavailable to the public and share data privately while protecting your online identity. Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies. Tor can be used to visit everyday internet websites, but it also has numerous hidden websites and services which can’t be accessed on the regular internet.
Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine). It might sound weird that Google doesn’t index these pages, but it does carry some logical sense. Google’s purpose is to show the most relevant information to all of its users quickly and easily. That means that Google wants to minimize the amount of time users spend searching for certain queries.

- Tails always starts with a clean slate and any evidence of the activities you engage in while using Tails disappears when you shut down Tails.
- The World Wide Web is a service that runs on internet infrastructure.
- The dark web is a subsegment of the deep web that can only be accessed with special tools, such as the Tor browser.
- This is high-level protection; no one can intercept your data or activities.
- It is the dark web’s version of Wikipedia with a massive links directory.
- These groups develop their own sophisticated malware, sometimes combined with pre-existing tools, and distribute them through “affiliates”.
Obviously, the search engines won’t be opting for a monthly subscription to index the catalog of such websites. “The Dark Web” is an overused term that can be a source of mystery and confusion for most cybersecurity professionals. Put simply, the Dark Web is any site, messaging platform, community, or other online entity that is not indexed by any search engine. A subset of the Deep Web, the Dark Web is intentionally hidden from your standard search engines, and is much more difficult to access as all its data is encrypted. It also includes paywalled services such as video on demand and some online magazines and newspapers.
The search engine crawlers do the same work as done by the explorer submarines. Most of this limited collection is in the form of Google sites and services. In reality, the internet is enormous, and it has around one billion websites existing on servers around the globe. Scammers often target users on the dark web, employing phishing tactics to steal personal information and financial details. These scams can result in significant financial loss and identity theft. The danger comes in when you download illegal materials that contain viruses or malware, like trojans, worms, or keyloggers.
- Unlike the deep web, which everyone uses daily, the dark web requires deliberate effort to access.
- Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc.
- His articles have appeared in many respected technology publications.
- For instance, Harvard University received a bomb threat via a disposable email in December 2013.
- The dark web has flourished thanks to bitcoin, the crypto-currency that enables two parties to conduct a trusted transaction without knowing each other’s identity.
The kinds of content present in this region include private databases, medical records, academic journals, and other sensitive information that requires special permission to access. For example, every academic institution holds valuable resources within its online libraries that are important to its students and researchers who have legitimate access but not for public consumption. The deep web contains hidden content, such as private databases, government websites, and intranets. These parts of the internet require users to log in to access the data, and they consist of cloud servers that are protected with encryption and unlisted by search engines. The deep web is a layer of the internet that’s not indexed by search engines and requires further permissions to access, like a paywalled academic resource or an employee-only corporate website.
You can never be sure of the motive of the person operating the node that your traffic is routed through. So hey, we’ve beaten around the bush quite a bit, let’s finally get you what you came here for, here’s how to access the deep web. First of all, you need to make sure there are no digital traces leading back to you associating you with your deep/dark web activities. (The isn’t list I believe is non-existent when it comes to the Dark web). Note that the dark web sites do not have extensions such as .com / .net / .org etc, as these are clearnet domain extensions and can be traced quite easily. I just mentioned the Tor network, and it’s a major part of both the deep as well as the dark web so let me explain what it is in brief.


